- Agents
- Essentials
- Getting Started
- Agent
- API
- APM Tracing
- Containers
- Dashboards
- Database Monitoring
- Datadog
- Datadog Site
- DevSecOps
- Incident Management
- Integrations
- Internal Developer Portal
- Logs
- Monitors
- Notebooks
- OpenTelemetry
- Profiler
- Search
- Session Replay
- Security
- Serverless for AWS Lambda
- Software Delivery
- Synthetic Monitoring and Testing
- Tags
- Workflow Automation
- Learning Center
- Support
- Glossary
- Standard Attributes
- Guides
- Agent
- Integrations
- Extend Datadog
- Authorization
- DogStatsD
- Custom Checks
- Integrations
- Build an Integration with Datadog
- Create an Agent-based Integration
- Create an API-based Integration
- Create a Log Pipeline
- Integration Assets Reference
- Build a Marketplace Offering
- Create an Integration Dashboard
- Create a Monitor Template
- Create a Cloud SIEM Detection Rule
- Install Agent Integration Developer Tool
- Service Checks
- Community
- Guides
- OpenTelemetry
- Administrator's Guide
- API
- Partners
- Datadog Mobile App
- DDSQL Reference
- CoScreen
- CoTerm
- Remote Configuration
- Cloudcraft (Standalone)
- In The App
- Dashboards
- Notebooks
- DDSQL Editor
- Reference Tables
- Sheets
- Monitors and Alerting
- Service Level Objectives
- Metrics
- Watchdog
- Bits AI
- Internal Developer Portal
- Error Tracking
- Change Tracking
- Event Management
- Incident Response
- Actions & Remediations
- Infrastructure
- Cloudcraft
- Resource Catalog
- Universal Service Monitoring
- End User Device Monitoring
- Hosts
- Containers
- Processes
- Serverless
- Network Monitoring
- Storage Management
- Cloud Cost
- Application Performance
- APM
- Continuous Profiler
- Database Monitoring
- Agent Integration Overhead
- Setup Architectures
- Setting Up Postgres
- Setting Up MySQL
- Setting Up SQL Server
- Setting Up Oracle
- Setting Up Amazon DocumentDB
- Setting Up MongoDB
- Setting Up ClickHouse
- Connecting DBM and Traces
- Data Collected
- Exploring Database Hosts
- Exploring Query Metrics
- Exploring Query Samples
- Exploring Database Schemas
- Exploring Recommendations
- Troubleshooting
- Guides
- Data Streams Monitoring
- Data Observability
- Digital Experience
- Real User Monitoring
- Synthetic Testing and Monitoring
- Continuous Testing
- Experiments
- Product Analytics
- Session Replay
- Software Delivery
- CI Visibility
- CD Visibility
- Deployment Gates
- Test Optimization
- Code Coverage
- PR Gates
- DORA Metrics
- Feature Flags
- Developer Integrations
- Security
- Security Overview
- Cloud SIEM
- Code Security
- Cloud Security
- App and API Protection
- AI Guard
- Workload Protection
- Sensitive Data Scanner
- AI Observability
- Log Management
- Observability Pipelines
- Configuration
- Sources
- Processors
- Destinations
- Packs
- Akamai CDN
- Amazon CloudFront
- Amazon VPC Flow Logs
- AWS Application Load Balancer Logs
- AWS CloudTrail
- AWS Elastic Load Balancer Logs
- AWS Network Load Balancer Logs
- Cisco ASA
- Cloudflare
- F5
- Fastly
- Fortinet Firewall
- HAProxy Ingress
- Istio Proxy
- Juniper SRX Firewall Traffic Logs
- Netskope
- NGINX
- Okta
- Palo Alto Firewall
- Windows XML
- ZScaler ZIA DNS
- Zscaler ZIA Firewall
- Zscaler ZIA Tunnel
- Zscaler ZIA Web Logs
- Search Syntax
- Scaling and Performance
- Monitoring and Troubleshooting
- Guides and Resources
- Log Management
- CloudPrem
- Administration
Setting file permissions for rotating logs (Linux)
The Datadog Agent runs under the dd-agent user and dd-agent group. This prevents the Datadog Agent from accessing the logs in /var/log as they are only accessible by root (or a sudo admin).
Setting permissions using ACLs
In order to allow read-only access for datadog-agent only, create ACLs and modify logrotate to persist the permissions changes.
Verifying ACLs are enabled on your system
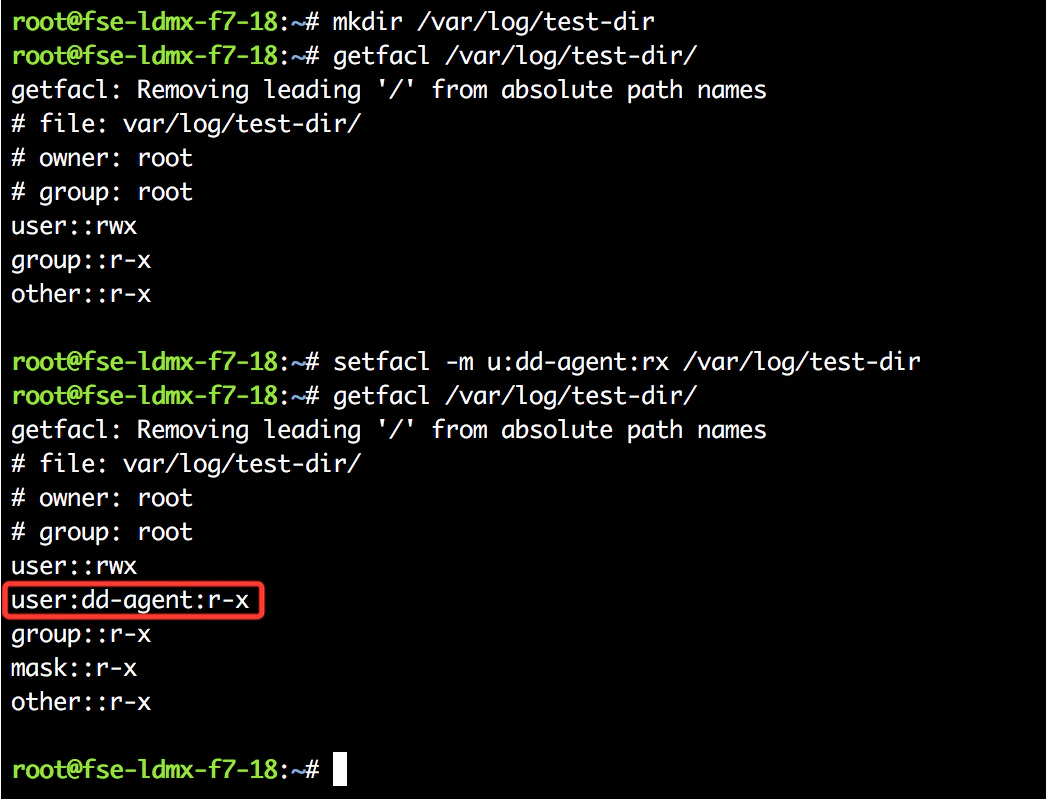
ACLs needs to be enabled on your file system to set permissions using the methods outlined in this article. Verify ACLs are enabled by using thegetfacl and setfacl commands to set permissions for the datadog-agent user on a test directory, for example:
mkdir /var/log/test-dir
getfacl /var/log/test-dir/
setfacl -m u:dd-agent:rx /var/log/test-dir
getfacl /var/log/test-dir/
The permissions set for datadog-agent appears in the output of getfacl if ACLs are enabled.
Granting dd-agent read and execute permissions on log directories
Once you have verified ACLs are enabled, grant read and execute permissions for the datadog-agent user on the appropriate directories for log collection. For example, to grant access to /var/log/apache , run:
setfacl -m u:dd-agent:rx /var/log/apache
Learn more about how to configure ACLs on linux
Setting permissions for log file rotation
Setting the permissions once will not persist for rotating logs, as logrotate does not re-apply the ACL setting. For a more permanent solution add a rule to logrotate to reset the ACL in a new file:
sudo touch /etc/logrotate.d/dd-agent_ACLs
Example file:
/var/log/apache/*.log {
postrotate
/usr/bin/setfacl -m g:dd-agent:rx /var/log/apache/access.log
/usr/bin/setfacl -m g:dd-agent:rx /var/log/apache/error.log
endscript
}
Check the ACL status of a file with:
getfacl /var/log/apache/access.log
Note: For PostgreSQL v10 and older, set the permission to 0700. For PostgreSQL v11, set either 0700 or 0750. Trying to start a server with a base data folder that has permissions different from 0700 or 0750 will result in a failure of the postmater process.
Note: The PostgreSQL logging directory cannot be located in the same directory as the base PostgreSQL installation.
Setting permissions when ACLs are not present
When ACLs are not present in a system, set your permissions based on group access.
For instance, if your MySQL service is logging to the following locations:
/var/log/mysql/mysql_error.log
/var/log/mysql/mysql-slow.log
Their permissions are associated with user ‘mysql’ and the group ‘mysql’ by default. This logging scheme denies access to the log file to any user not in the ‘mysql’ group. Typically you may see something like this:
$ ls -l /var/log | grep -i mysql
drwxr-x--- 2 mysql mysql 4096 Feb 20 06:25 mysql
The easiest path here is to give everyone read access to the file in the logrotate configuration:
/var/log/mysql/mysql_error.log /var/log/mysql/mysql-slow.log {
daily
rotate 7
missingok
create 644 mysql adm
compress
}
Each common off-the-shelf application will follow a similar nomenclature. The advantage is that you avoid providing privileged access to an individual account and use a standardized practice. This keeps your audit rules in check.
Further Reading
Additional helpful documentation, links, and articles: