- 重要な情報
- はじめに
- 用語集
- Standard Attributes
- ガイド
- インテグレーション
- エージェント
- OpenTelemetry
- 開発者
- Administrator's Guide
- API
- Partners
- DDSQL Reference
- モバイルアプリケーション
- CoScreen
- CoTerm
- Remote Configuration
- Cloudcraft
- アプリ内
- ダッシュボード
- ノートブック
- DDSQL Editor
- Reference Tables
- Sheets
- Watchdog
- アラート設定
- メトリクス
- Bits AI
- Internal Developer Portal
- Error Tracking
- Change Tracking
- Service Management
- Actions & Remediations
- インフラストラクチャー
- Cloudcraft
- Resource Catalog
- ユニバーサル サービス モニタリング
- Hosts
- コンテナ
- Processes
- サーバーレス
- ネットワークモニタリング
- Cloud Cost
- アプリケーションパフォーマンス
- APM
- Continuous Profiler
- データベース モニタリング
- Data Streams Monitoring
- Data Jobs Monitoring
- Data Observability
- Digital Experience
- RUM & セッションリプレイ
- Synthetic モニタリング
- Continuous Testing
- Product Analytics
- Software Delivery
- CI Visibility (CI/CDの可視化)
- CD Visibility
- Deployment Gates
- Test Visibility
- Code Coverage
- Quality Gates
- DORA Metrics
- Feature Flags
- セキュリティ
- セキュリティの概要
- Cloud SIEM
- Code Security
- クラウド セキュリティ マネジメント
- Application Security Management
- Workload Protection
- Sensitive Data Scanner
- AI Observability
- ログ管理
- Observability Pipelines(観測データの制御)
- ログ管理
- CloudPrem
- 管理
Azure AD で SSO を有効にする
アイデンティティプロバイダーとして Azure AD を使用してシングルサインオン (SSO) を有効にすると、Cloudcraft への認証とログインアクセスを簡素化できます。
この記事では、アイデンティティプロバイダーが Azure AD の場合の SSO のセットアップ方法について説明します。その他のアイデンティティプロバイダーについては、以下の記事を参照してください。
Cloudcraft で SSO を使用するための一般的な情報については、アカウントで SSO を有効にするをご覧ください。
SAML/SSO のセットアップ
アカウントオーナーのみが SAML SSO 機能を設定できます。アカウントオーナーが SSO を設定できない場合は、Cloudcraft サポートチームに連絡してこの機能を有効にしてください。
- Cloudcraft で、User > Security & SSO に移動します。
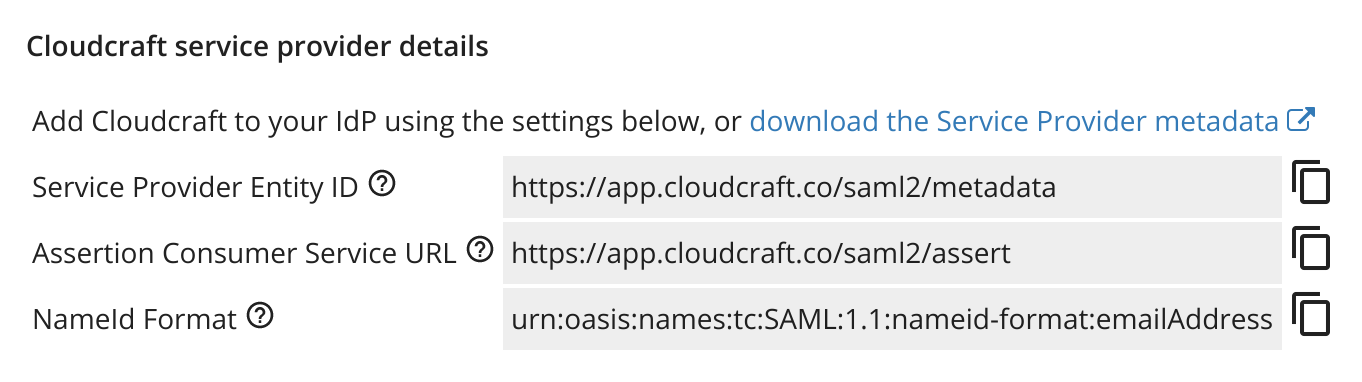
- Azure で新しいアプリケーションを作成するために必要な詳細は、Cloudcraft サービスプロバイダーの詳細セクションに記載されています。
- 管理者として Azure にログインします。
- 画面左上のハンバーガーメニューをクリックし、Azure Active Directory を選択します。
- 左メニューの Manage セクションで、Enterprise applications をクリックします。
- New application をクリックし、Non-gallery application を選択します。
- アプリケーション名として Cloudcraft を入力し、Add をクリックします。
次に、Cloudcraft から提供された詳細を使用して SAML インテグレーションを構成します。
- Getting started セクションで、Set up single sign on を選択し、SAML をクリックします。
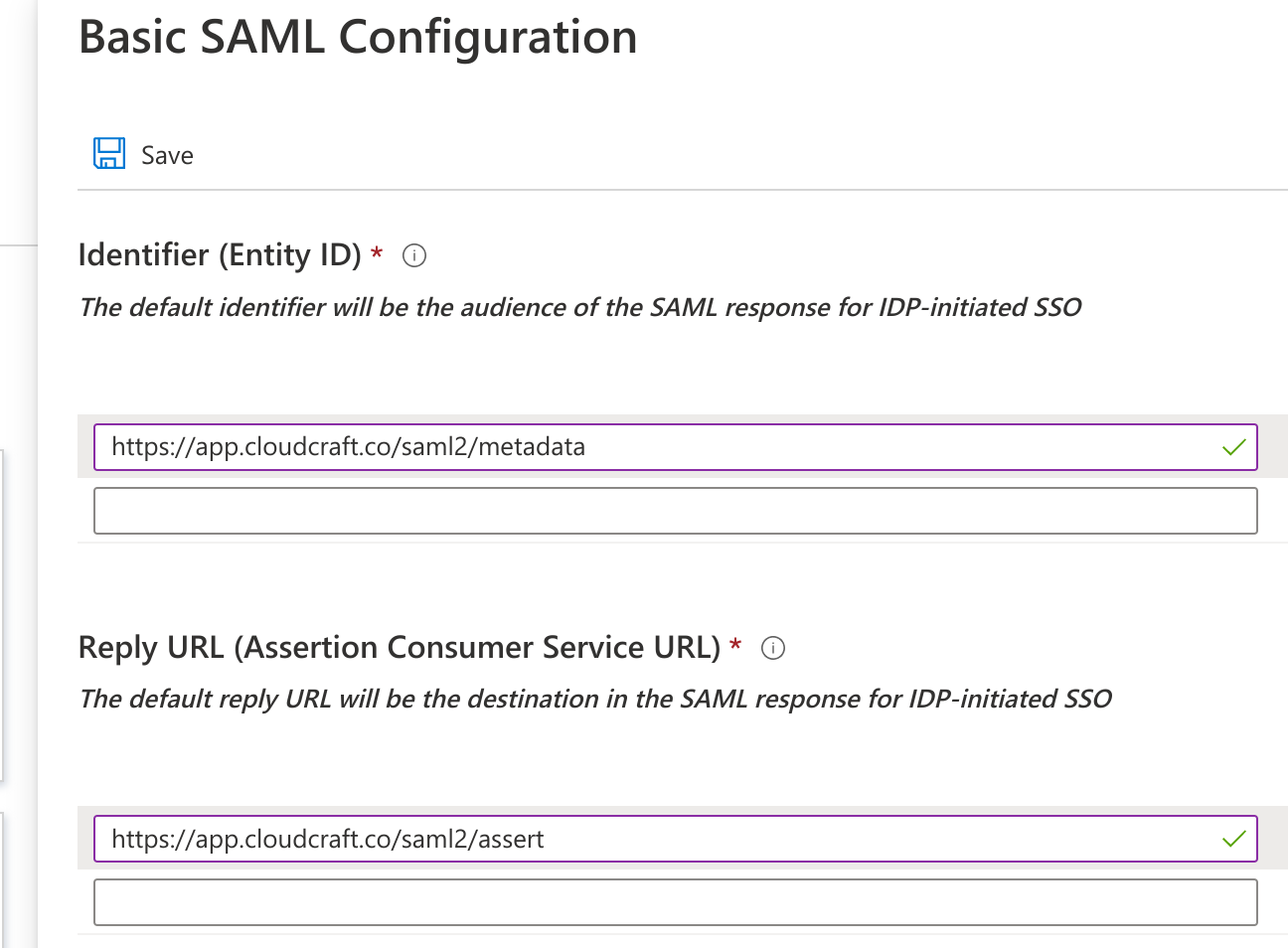
- Basic SAML Configuration セクションで、Edit をクリックします。
- Cloudcraft から提供された詳細を入力します。フィールドは以下のようにマッピングされ、最初の値は Azure AD のラベル、2 番目の値は Cloudcraft ダイアログのラベルです。
- Identifier: サービスプロバイダーエンティティ ID
- Reply URL: アサーションコンシューマーサービス URL
- Sign on URL: アイデンティティプロバイダー主導の SSO を許可する場合は空白のままにします。
- Save をクリックして、前の画面に戻ります。
- SAML Signing Certificate セクションで、Federation Metadata XML を選択し、XML ファイルをコンピュータにダウンロードします。
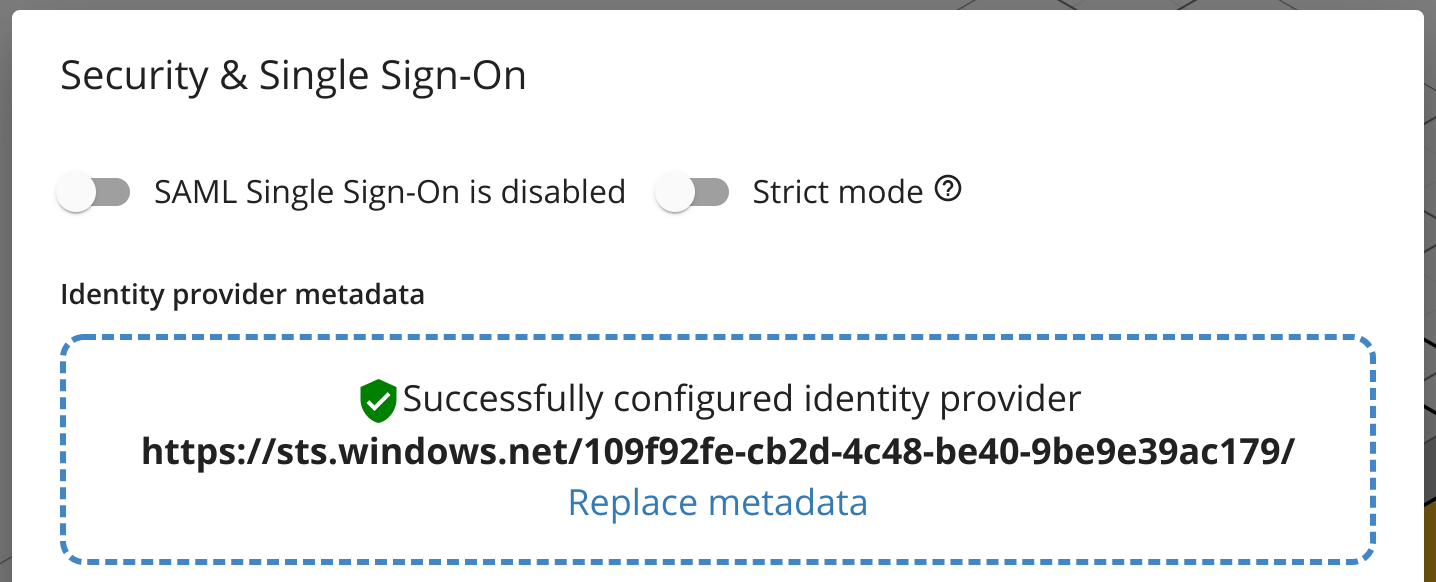
- Cloudcraft に戻り、メタデータ XML ファイルをアップロードします。
- SAML Single Sign-On is enabled オプションを切り替えます。
- Azure ポータルに戻ります。
- Test single sign-on with Cloudcraft セクションで、Test をクリックしてインテグレーションをテストします。
- ユーザーが Azure AD 経由でのみ Cloudcraft にアクセスするようにしたい場合は、Strict mode オプションを有効にすると、他のすべてのログイン方法が無効になります。
注: 組織内のユーザーにアクセスを許可するには、Azure AD ドキュメントを参照してください。