- Principales informations
- Getting Started
- Agent
- API
- Tracing
- Conteneurs
- Dashboards
- Database Monitoring
- Datadog
- Site Datadog
- DevSecOps
- Incident Management
- Intégrations
- Internal Developer Portal
- Logs
- Monitors
- OpenTelemetry
- Profileur
- Session Replay
- Security
- Serverless for AWS Lambda
- Software Delivery
- Surveillance Synthetic
- Tags
- Workflow Automation
- Learning Center
- Support
- Glossary
- Standard Attributes
- Guides
- Agent
- Intégrations
- Développeurs
- OpenTelemetry
- Administrator's Guide
- API
- Partners
- Application mobile
- DDSQL Reference
- CoScreen
- CoTerm
- Remote Configuration
- Cloudcraft
- In The App
- Dashboards
- Notebooks
- DDSQL Editor
- Reference Tables
- Sheets
- Alertes
- Watchdog
- Métriques
- Bits AI
- Internal Developer Portal
- Error Tracking
- Change Tracking
- Service Management
- Actions & Remediations
- Infrastructure
- Cloudcraft
- Resource Catalog
- Universal Service Monitoring
- Hosts
- Conteneurs
- Processes
- Sans serveur
- Surveillance réseau
- Cloud Cost
- Application Performance
- APM
- Termes et concepts de l'APM
- Sending Traces to Datadog
- APM Metrics Collection
- Trace Pipeline Configuration
- Connect Traces with Other Telemetry
- Trace Explorer
- Recommendations
- Code Origin for Spans
- Observabilité des services
- Endpoint Observability
- Dynamic Instrumentation
- Live Debugger
- Suivi des erreurs
- Sécurité des données
- Guides
- Dépannage
- Profileur en continu
- Database Monitoring
- Agent Integration Overhead
- Setup Architectures
- Configuration de Postgres
- Configuration de MySQL
- Configuration de SQL Server
- Setting Up Oracle
- Setting Up Amazon DocumentDB
- Setting Up MongoDB
- Connecting DBM and Traces
- Données collectées
- Exploring Database Hosts
- Explorer les métriques de requête
- Explorer des échantillons de requêtes
- Exploring Database Schemas
- Exploring Recommendations
- Dépannage
- Guides
- Data Streams Monitoring
- Data Jobs Monitoring
- Data Observability
- Digital Experience
- RUM et Session Replay
- Surveillance Synthetic
- Continuous Testing
- Product Analytics
- Software Delivery
- CI Visibility
- CD Visibility
- Deployment Gates
- Test Visibility
- Code Coverage
- Quality Gates
- DORA Metrics
- Feature Flags
- Securité
- Security Overview
- Cloud SIEM
- Code Security
- Cloud Security Management
- Application Security Management
- Workload Protection
- Sensitive Data Scanner
- AI Observability
- Log Management
- Pipelines d'observabilité
- Log Management
- CloudPrem
- Administration
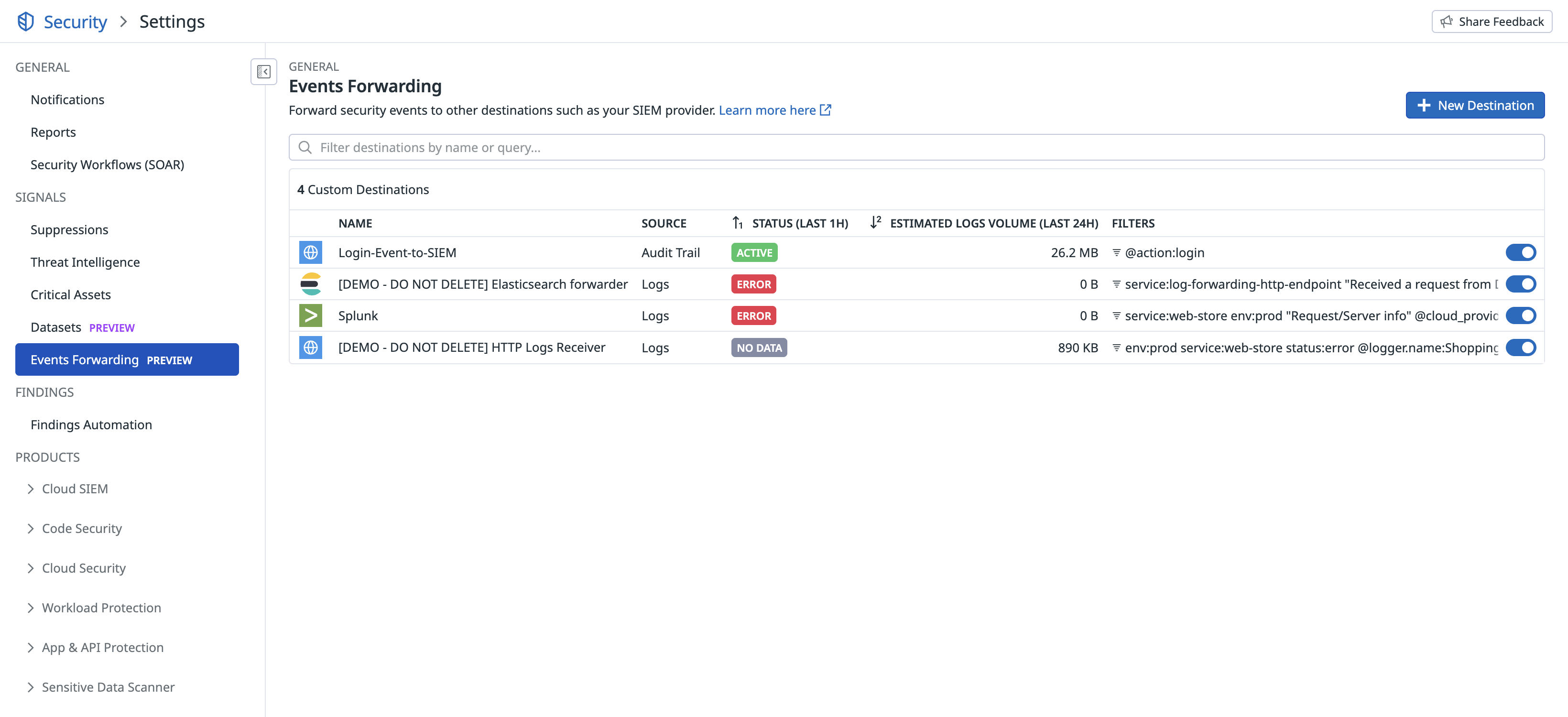
Events Forwarding
Cette page n'est pas encore disponible en français, sa traduction est en cours.
Si vous avez des questions ou des retours sur notre projet de traduction actuel, n'hésitez pas à nous contacter.
Si vous avez des questions ou des retours sur notre projet de traduction actuel, n'hésitez pas à nous contacter.
Overview
Events Forwarding sends logs, audit logs, security spans, security signals, and cloud workload security events from Datadog to custom destinations such as Splunk, Elasticsearch, and HTTP endpoints. Use Events Forwarding to route security and observability data to third-party SIEMs, data lakes, or internal tools.
Events Forwarding supports the following data types:
| Data Type | Description |
|---|---|
| Logs | Application and infrastructure logs |
| Audit Logs | Datadog platform audit events |
| Security Spans | Traces from App and API Protection |
| Security Signals | Signals generated by Detection Rules |
| Cloud Workload Security Events | Runtime security events from Workload Protection |
Note: For logs, additional destination types are available (Microsoft Sentinel, Google Chronicle). See Forwarding Logs to Custom Destinations for details.
Prerequisites
Permissions
Forwarding rules require data-type-specific permissions. The following table lists the required permission for each data type.
| Data Type | Permission |
|---|---|
| Logs | logs_write_forwarding_rules |
| Audit Logs | audit_logs_write |
| Security Spans | apm_pipelines_write |
| Security Signals | security_monitoring_signals_write |
| Cloud Workload Security Events | security_monitoring_cws_agent_rules_write |
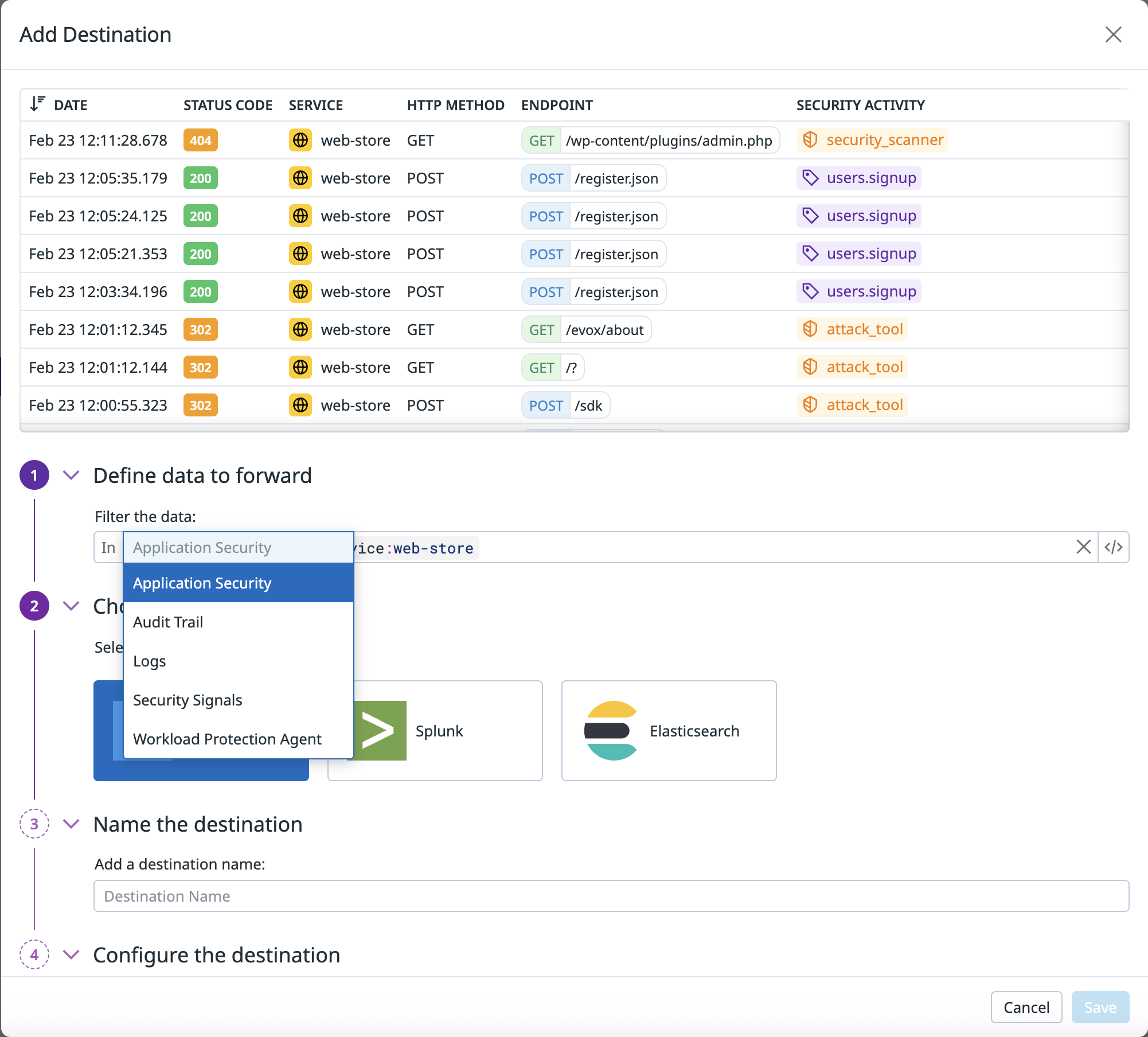
Set up Events Forwarding
Events Forwarding uses the same destination types and configuration as log forwarding. For detailed instructions on setting up destinations, see Forwarding Logs to Custom Destinations.
- Sending events to a custom destination is outside of the Datadog GovCloud environment, which is outside the control of Datadog. Datadog shall not be responsible for any events that have left the Datadog GovCloud environment, including without limitation, any obligations or requirements that the user may have related to FedRAMP, DoD Impact Levels, ITAR, export compliance, data residency, or similar regulations applicable to such events.
- Due to security protocols for the GovCloud site, only ports
443and8088are available for Events Forwarding. If your custom destination uses a different port, contact Datadog Support to explore opening your port for outbound communications.
To set up a forwarding rule:
- Navigate to Security Settings > Events Forwarding.
- Click New Destination.
- Select the data type you want to forward.
- Enter a query to filter events. Only matching events are forwarded.
- Select and configure the destination type.
- Click Save.
Supported destination types
The following destination types are available for all data types:
- HTTP - Send events to any HTTPS endpoint with basic authentication or custom headers.
- Splunk - Forward events using Splunk’s HTTP Event Collector (HEC).
- Elasticsearch - Send events to an Elasticsearch cluster with configurable index rotation.
For logs, these destinations are also supported: Microsoft Sentinel and Google Chronicle. See Forwarding Logs to Custom Destinations for setup details.
Monitoring
The following metrics report on events that have been forwarded successfully, including events that were sent successfully after retries, as well as events that were dropped:
datadog.forwarding.<data_type>.bytesdatadog.forwarding.<data_type>.count
Where <data_type> corresponds to the forwarded data type (for example, logs, trace, signal, secruntime).
Further reading
Documentation, liens et articles supplémentaires utiles: