- Principales informations
- Getting Started
- Agent
- API
- Tracing
- Conteneurs
- Dashboards
- Database Monitoring
- Datadog
- Site Datadog
- DevSecOps
- Incident Management
- Intégrations
- Internal Developer Portal
- Logs
- Monitors
- OpenTelemetry
- Profileur
- Session Replay
- Security
- Serverless for AWS Lambda
- Software Delivery
- Surveillance Synthetic
- Tags
- Workflow Automation
- Learning Center
- Support
- Glossary
- Standard Attributes
- Guides
- Agent
- Intégrations
- Développeurs
- OpenTelemetry
- Administrator's Guide
- API
- Partners
- Application mobile
- DDSQL Reference
- CoScreen
- CoTerm
- Remote Configuration
- Cloudcraft
- In The App
- Dashboards
- Notebooks
- DDSQL Editor
- Reference Tables
- Sheets
- Alertes
- Watchdog
- Métriques
- Bits AI
- Internal Developer Portal
- Error Tracking
- Change Tracking
- Service Management
- Actions & Remediations
- Infrastructure
- Cloudcraft
- Resource Catalog
- Universal Service Monitoring
- Hosts
- Conteneurs
- Processes
- Sans serveur
- Surveillance réseau
- Cloud Cost
- Application Performance
- APM
- Termes et concepts de l'APM
- Sending Traces to Datadog
- APM Metrics Collection
- Trace Pipeline Configuration
- Connect Traces with Other Telemetry
- Trace Explorer
- Recommendations
- Code Origin for Spans
- Observabilité des services
- Endpoint Observability
- Dynamic Instrumentation
- Live Debugger
- Suivi des erreurs
- Sécurité des données
- Guides
- Dépannage
- Profileur en continu
- Database Monitoring
- Agent Integration Overhead
- Setup Architectures
- Configuration de Postgres
- Configuration de MySQL
- Configuration de SQL Server
- Setting Up Oracle
- Setting Up Amazon DocumentDB
- Setting Up MongoDB
- Connecting DBM and Traces
- Données collectées
- Exploring Database Hosts
- Explorer les métriques de requête
- Explorer des échantillons de requêtes
- Exploring Database Schemas
- Exploring Recommendations
- Dépannage
- Guides
- Data Streams Monitoring
- Data Jobs Monitoring
- Data Observability
- Digital Experience
- RUM et Session Replay
- Surveillance Synthetic
- Continuous Testing
- Product Analytics
- Software Delivery
- CI Visibility
- CD Visibility
- Deployment Gates
- Test Visibility
- Code Coverage
- Quality Gates
- DORA Metrics
- Feature Flags
- Securité
- Security Overview
- Cloud SIEM
- Code Security
- Cloud Security Management
- Application Security Management
- Workload Protection
- Sensitive Data Scanner
- AI Observability
- Log Management
- Pipelines d'observabilité
- Log Management
- CloudPrem
- Administration
Activer le SSO avec Okta
Si vous préférez que vos utilisateurs accèdent à Cloudcraft uniquement via votre fournisseur d’identité, activez l’option Strict mode.
Cet article vous aide à configurer le SSO si votre fournisseur d’identité est Okta. Pour les autres fournisseurs d’identité, consultez les articles suivants :
Pour des informations générales sur l’utilisation du SSO avec Cloudcraft, consultez la section Activer le SSO dans votre compte.
Configuration de SAML/SSO
Seul le propriétaire du compte peut configurer la fonctionnalité SAML SSO. Si le propriétaire du compte n'est pas en mesure de configurer le SSO, contactez l'équipe d'assistance de Cloudcraft pour activer cette fonctionnalité.
- Dans Cloudcraft, accédez à User > Security & SSO.
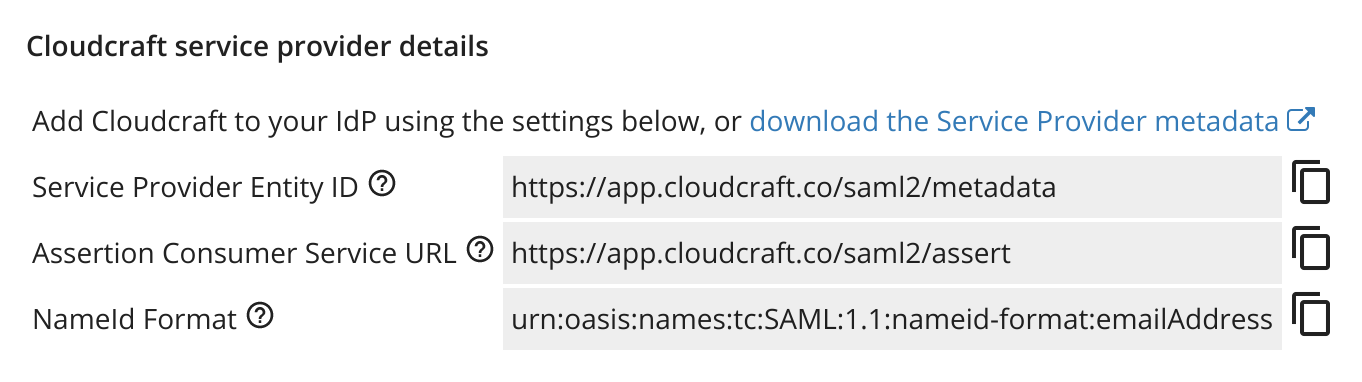
- Les détails dont vous avez besoin pour créer une nouvelle application avec Okta se trouvent dans la section Cloudcraft service provider details.
- Connectez-vous à Okta en tant qu’administrateur.
- Cliquez sur Application.
- Cliquez sur Add Application, puis cliquez sur Create New App.
- Sélectionnez SAML 2.0 comme méthode de connexion et cliquez sur Create.
- Saisissez Cloudcraft comme nom de l’application et laissez les valeurs restantes telles quelles.
- Cliquez sur Next.
Si vous préférez utiliser un logo d'application, vous pouvez utiliser ce logo qui respecte les restrictions de taille d'Okta.
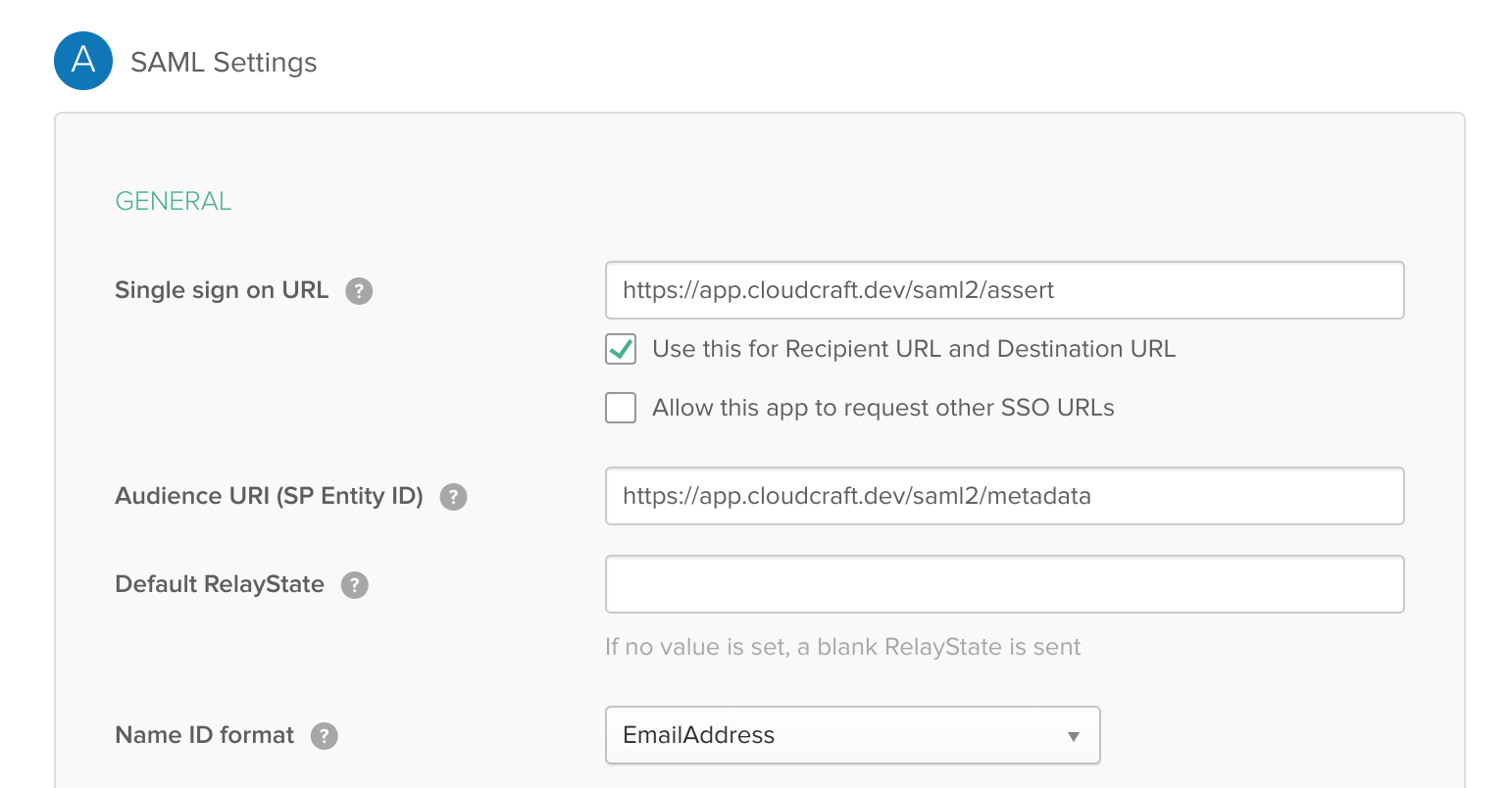
- Ensuite, configurez l’intégration SAML en utilisant les détails fournis par Cloudcraft. Les champs sont mappés comme suit, le premier étant l’étiquette dans Okta et le second étant l’étiquette chez Cloudcraft.
- Single sign on URL : URL du service consommateur d’assertions
- Audience URI : ID de l’entité prestataire de services
- Dans le menu déroulant Name ID format, sélectionnez EmailAddress.
- Passez à l’écran suivant et sélectionnez I’m an Okta customer adding an internal app pour répondre à la question « Are you a customer or partner? ».
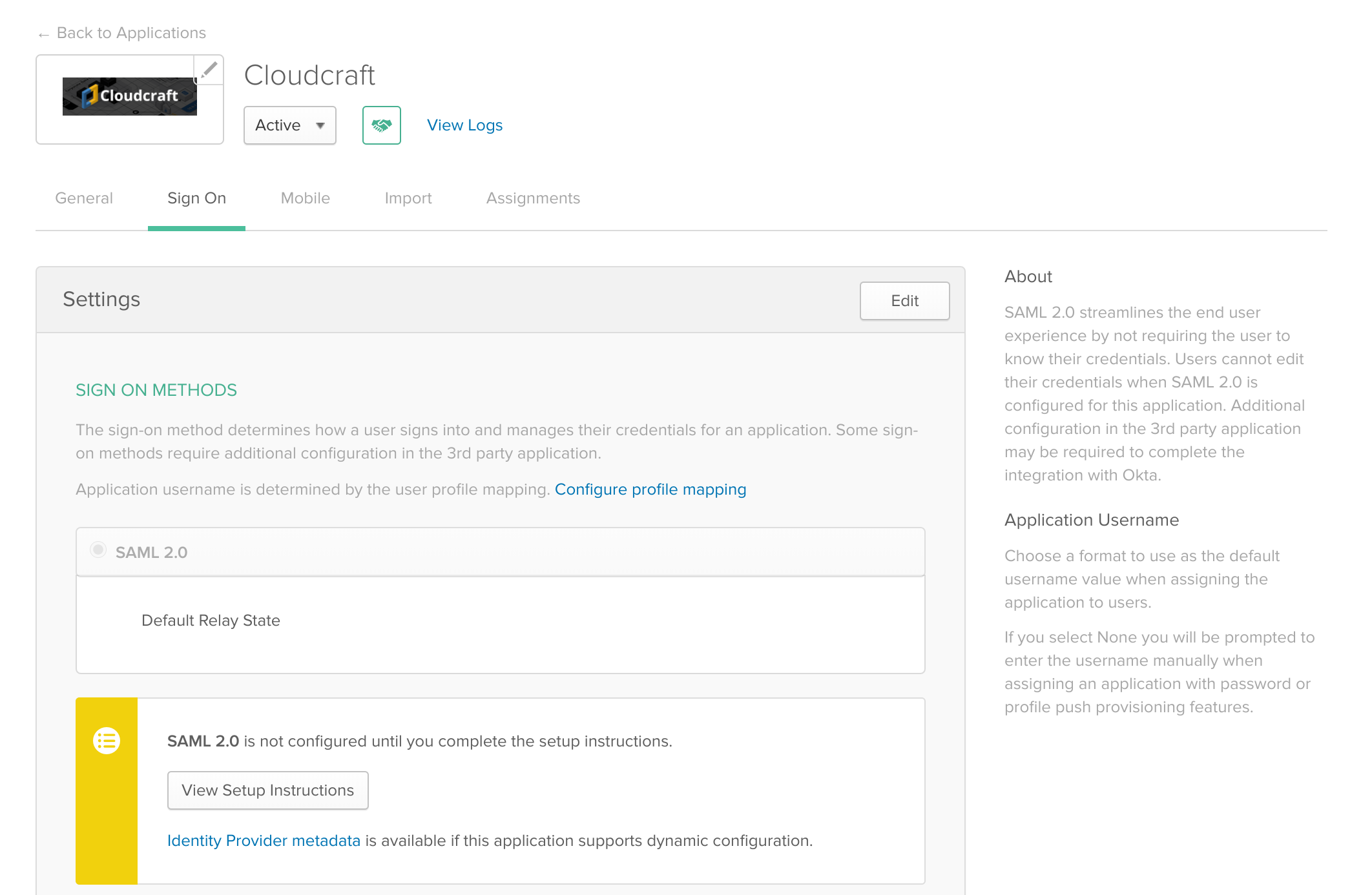
- Cliquez sur Finish. Maintenant que l’application est configurée dans Okta, vous pouvez y attribuer vos utilisateurs et une fois que vous avez terminé, accédez à l’onglet Sign On.
- Sous le bouton View Setup Instructions, cliquez sur le lien bleu pour télécharger le fichier requis pour le téléchargement vers Cloudcraft.
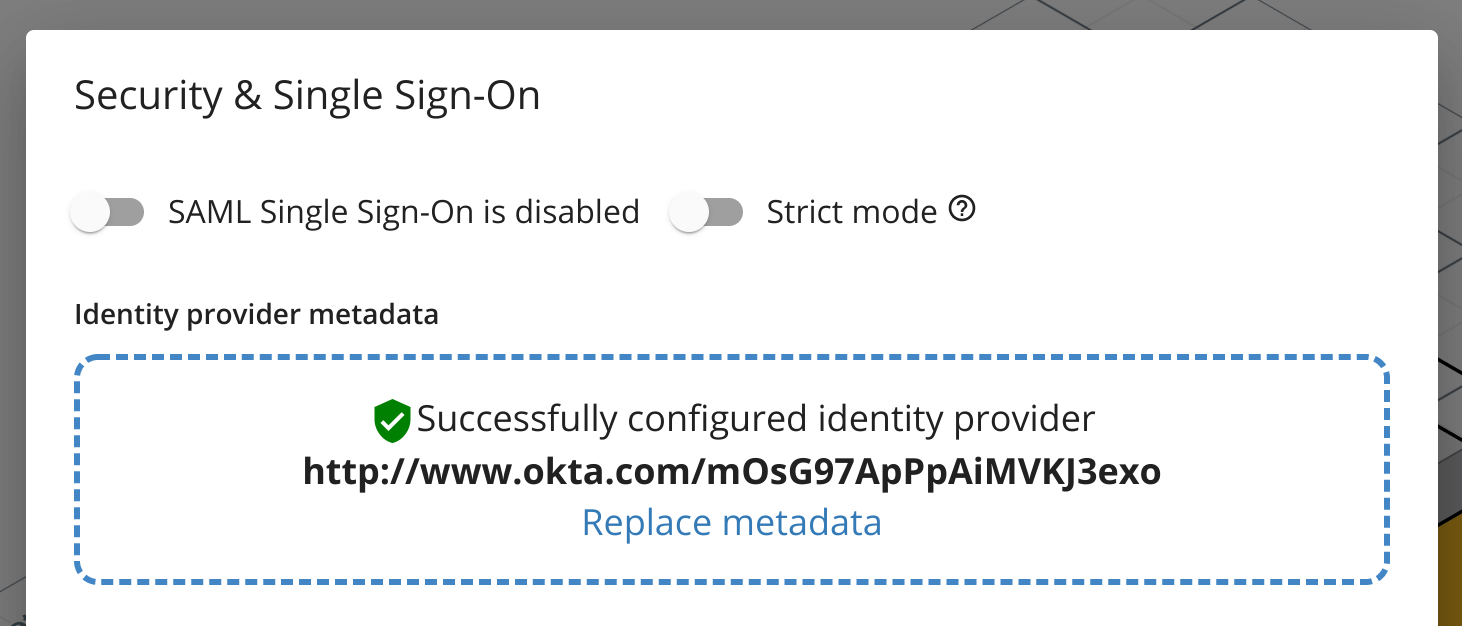
- Revenez à Cloudcraft et téléchargez votre fichier de configuration.
- Basculez l’option SAML Single Sign-On is enabled.
- Si vous préférez que vos utilisateurs accèdent à Cloudcraft uniquement via votre fournisseur d’identité, activez l’option Strict mode.