- Principales informations
- Getting Started
- Agent
- API
- Tracing
- Conteneurs
- Dashboards
- Database Monitoring
- Datadog
- Site Datadog
- DevSecOps
- Incident Management
- Intégrations
- Internal Developer Portal
- Logs
- Monitors
- OpenTelemetry
- Profileur
- Session Replay
- Security
- Serverless for AWS Lambda
- Software Delivery
- Surveillance Synthetic
- Tags
- Workflow Automation
- Learning Center
- Support
- Glossary
- Standard Attributes
- Guides
- Agent
- Intégrations
- Développeurs
- OpenTelemetry
- Administrator's Guide
- API
- Partners
- Application mobile
- DDSQL Reference
- CoScreen
- CoTerm
- Remote Configuration
- Cloudcraft
- In The App
- Dashboards
- Notebooks
- DDSQL Editor
- Reference Tables
- Sheets
- Alertes
- Watchdog
- Métriques
- Bits AI
- Internal Developer Portal
- Error Tracking
- Change Tracking
- Service Management
- Actions & Remediations
- Infrastructure
- Cloudcraft
- Resource Catalog
- Universal Service Monitoring
- Hosts
- Conteneurs
- Processes
- Sans serveur
- Surveillance réseau
- Cloud Cost
- Application Performance
- APM
- Termes et concepts de l'APM
- Sending Traces to Datadog
- APM Metrics Collection
- Trace Pipeline Configuration
- Connect Traces with Other Telemetry
- Trace Explorer
- Recommendations
- Code Origin for Spans
- Observabilité des services
- Endpoint Observability
- Dynamic Instrumentation
- Live Debugger
- Suivi des erreurs
- Sécurité des données
- Guides
- Dépannage
- Profileur en continu
- Database Monitoring
- Agent Integration Overhead
- Setup Architectures
- Configuration de Postgres
- Configuration de MySQL
- Configuration de SQL Server
- Setting Up Oracle
- Setting Up Amazon DocumentDB
- Setting Up MongoDB
- Connecting DBM and Traces
- Données collectées
- Exploring Database Hosts
- Explorer les métriques de requête
- Explorer des échantillons de requêtes
- Exploring Database Schemas
- Exploring Recommendations
- Dépannage
- Guides
- Data Streams Monitoring
- Data Jobs Monitoring
- Data Observability
- Digital Experience
- RUM et Session Replay
- Surveillance Synthetic
- Continuous Testing
- Product Analytics
- Software Delivery
- CI Visibility
- CD Visibility
- Deployment Gates
- Test Visibility
- Code Coverage
- Quality Gates
- DORA Metrics
- Feature Flags
- Securité
- Security Overview
- Cloud SIEM
- Code Security
- Cloud Security Management
- Application Security Management
- Workload Protection
- Sensitive Data Scanner
- AI Observability
- Log Management
- Pipelines d'observabilité
- Log Management
- CloudPrem
- Administration
Personal Access Tokens
Cette page n'est pas encore disponible en français, sa traduction est en cours.
Si vous avez des questions ou des retours sur notre projet de traduction actuel, n'hésitez pas à nous contacter.
Si vous avez des questions ou des retours sur notre projet de traduction actuel, n'hésitez pas à nous contacter.
Join the Preview!
Personal Access Tokens are in Preview.
Overview
Personal Access Tokens (PATs) are a credential type that authenticates Datadog API calls. Unlike application keys, PATs do not need to be paired with an API key. They are short-lived and scoped by default, giving you tighter control over what each token can access and how long it remains valid.
With PATs, you can:
- Authenticate API calls with a single credential.
- Enforce the principle of least privilege by selecting only the scopes your workflow needs.
- Limit the blast radius of leaked credentials through mandatory time-to-live (TTL) values. Expired tokens are automatically revoked, so inactive credentials do not persist indefinitely.
- Separate concerns by reserving API keys for telemetry submission (Agent, logs, metrics) and use PATs for all other web API calls.
PATs compared to application keys
| Personal Access Tokens | Application keys | |
|---|---|---|
| Standalone authentication | Yes; no API key pairing needed | No; requires an API key |
| Scoped by default | Yes; scopes are mandatory | Optional; unscoped by default |
| Time-to-live (TTL) | Required (24 hours to one year) | No expiration |
| Identifiable prefix | Yes; ddpat_ | Yes; ddap_ (new) |
| Linked to | Individual user | Individual user |
Prerequisites
- A Datadog user account with the
user_app_keyspermission - The
org_app_keys_writepermission if you want to manage PATs for other users in the organization
Create a Personal Access Token
- Navigate to Personal Settings > Access Tokens.
- Click + New Access Token.
- Enter a Name for the token.
- Select an Expiration Date. The minimum expiration is 24 hours and the maximum is one year from creation.
- Click Select Scopes to choose the scopes that define what this token can access. At least one scope is required. Grant only the permissions your workflow requires, then click Save.
Datadog displays the token secret only once at creation time. Copy and store it securely. You cannot retrieve it later.
Use a Personal Access Token
PATs support two authentication methods.
Authorization header (recommended)
Pass the PAT as a Bearer token in the Authorization header. This method does not require an API key:
curl -X GET "https://api.datadoghq.com/api/v2/users" \
-H "Authorization: Bearer <YOUR_PAT>"
Application key header
Pass the PAT in the dd-application-key header. This is useful for migrating existing integrations that already use the application key header format:
curl -X GET "https://api.datadoghq.com/api/v2/users" \
-H "dd-application-key: <YOUR_PAT>"
Note: When a valid PAT is provided in the dd-application-key header, Datadog authenticates with the PAT only. The dd-api-key header is optional and its value is not evaluated.
Manage Personal Access Tokens
View your tokens
Navigate to Personal Settings > Access Tokens to see all PATs associated with your account, including their names, scopes, expiration dates, and last usage information.
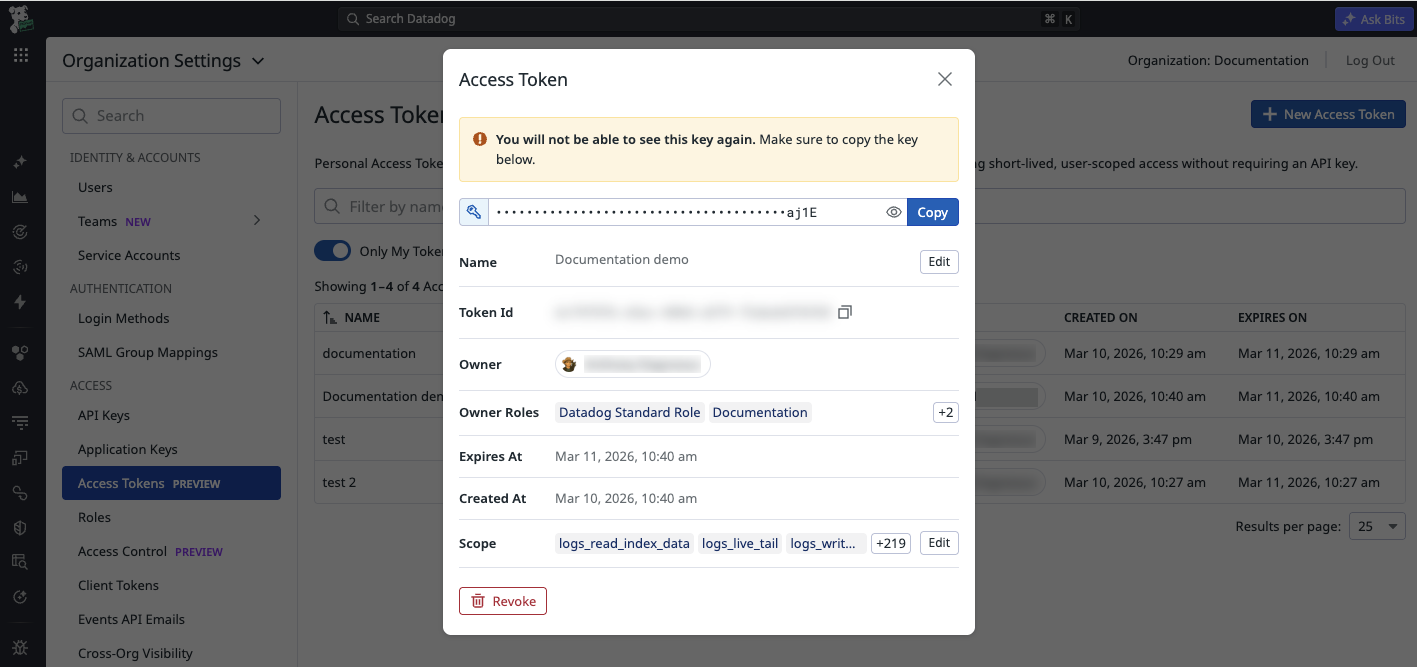
After creating a token, a details panel displays the token secret, name, Token ID, owner, scopes, and expiration date. From this panel, you can also edit or revoke the token.
Manage tokens as an administrator
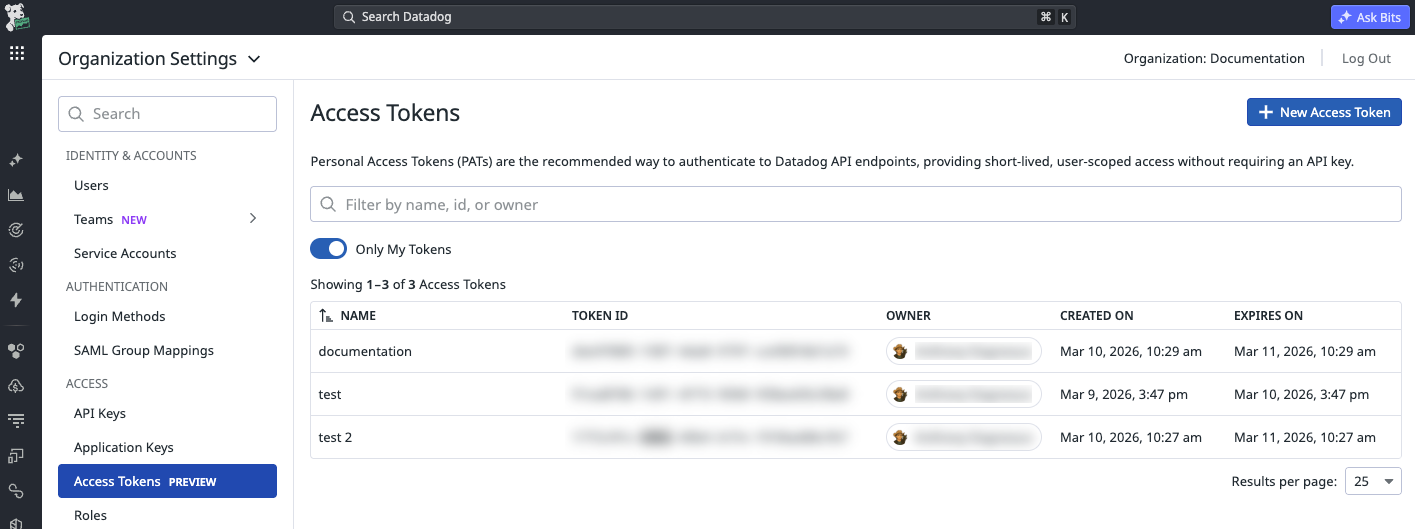
Organization administrators with the org_app_keys_read and org_app_keys_write permissions can view and manage PATs for all users in the organization from Organization Settings > Access Tokens.
Revoke a token
- Navigate to Personal Settings > Access Tokens, or Organization Settings > Access Tokens for administrators.
- Mouse over the token you want to revoke and click the Revoke Token icon.
Revoked tokens can no longer authenticate API calls. Revocation takes effect within seconds.
Edit a token
You can update the name and scopes of an existing PAT. You cannot modify the TTL after creation. To change the TTL, revoke the existing token and create a token with the desired configuration.
Token format
PATs use an identifiable format that supports secret scanning and key management:
ddpat_<ALIAS>_<SECRET><CHECKSUM>
| Component | Description |
|---|---|
ddpat_ | Prefix identifying the credential as a Personal Access Token |
<ALIAS> | Base62-encoded token identifier, derived from the token UUID |
<SECRET> | 32-byte randomly generated secret |
<CHECKSUM> | CRC32 checksum following the GitHub checksum standard |
The identifiable prefix and checksum enable automated detection by secret scanning services, including GitHub secret scanning, Sensitive Data Scanner, and GitGuardian.
Permissions
PATs use the same permissions as application keys:
| Permission | Description |
|---|---|
user_app_keys | Create and manage your own PATs |
org_app_keys_read | View PATs for all users in the organization |
org_app_keys_write | Create, edit, and revoke PATs for any user in the organization |
For more information about permissions, see Role Based Access Control.
Audit Trail
If Audit Trail is enabled for your organization, Audit Trail records all PAT creation, usage, and revocation events. Audit Trail captures the authentication method and token metadata for each API call made with a PAT, giving administrators visibility into credential usage across the organization.
To review PAT activity, navigate to Security > Compliance > Audit Trail and filter by the Personal Access Token authentication method.
API reference
Manage PATs programmatically through the Datadog API:
| Operation | Endpoint |
|---|---|
| List PATs | GET /api/v2/personal_access_tokens |
| Create a PAT | POST /api/v2/personal_access_tokens |
| Get a specific PAT | GET /api/v2/personal_access_tokens/<PAT_ID> |
| Update a PAT | PATCH /api/v2/personal_access_tokens/<PAT_ID> |
| Revoke a PAT | DELETE /api/v2/personal_access_tokens/<PAT_ID> |
For the full API reference, see Key Management.
Key propagation delay
PATs follow an eventual consistency model. After creation or revocation, changes may take a few seconds to propagate across all Datadog systems. Do not use a token immediately after creation in critical workflows. Implement a retry strategy with short exponential backoff to handle transient errors during the propagation window.