- Esenciales
- Empezando
- Agent
- API
- Rastreo de APM
- Contenedores
- Dashboards
- Monitorización de bases de datos
- Datadog
- Sitio web de Datadog
- DevSecOps
- Gestión de incidencias
- Integraciones
- Internal Developer Portal
- Logs
- Monitores
- OpenTelemetry
- Generador de perfiles
- Session Replay
- Security
- Serverless para Lambda AWS
- Software Delivery
- Monitorización Synthetic
- Etiquetas (tags)
- Workflow Automation
- Centro de aprendizaje
- Compatibilidad
- Glosario
- Atributos estándar
- Guías
- Agent
- Arquitectura
- IoT
- Plataformas compatibles
- Recopilación de logs
- Configuración
- Automatización de flotas
- Solucionar problemas
- Detección de nombres de host en contenedores
- Modo de depuración
- Flare del Agent
- Estado del check del Agent
- Problemas de NTP
- Problemas de permisos
- Problemas de integraciones
- Problemas del sitio
- Problemas de Autodiscovery
- Problemas de contenedores de Windows
- Configuración del tiempo de ejecución del Agent
- Consumo elevado de memoria o CPU
- Guías
- Seguridad de datos
- Integraciones
- Desarrolladores
- Autorización
- DogStatsD
- Checks personalizados
- Integraciones
- Build an Integration with Datadog
- Crear una integración basada en el Agent
- Crear una integración API
- Crear un pipeline de logs
- Referencia de activos de integración
- Crear una oferta de mercado
- Crear un dashboard de integración
- Create a Monitor Template
- Crear una regla de detección Cloud SIEM
- Instalar la herramienta de desarrollo de integraciones del Agente
- Checks de servicio
- Complementos de IDE
- Comunidad
- Guías
- OpenTelemetry
- Administrator's Guide
- API
- Partners
- Aplicación móvil de Datadog
- DDSQL Reference
- CoScreen
- CoTerm
- Remote Configuration
- Cloudcraft
- En la aplicación
- Dashboards
- Notebooks
- Editor DDSQL
- Reference Tables
- Hojas
- Monitores y alertas
- Watchdog
- Métricas
- Bits AI
- Internal Developer Portal
- Error Tracking
- Explorador
- Estados de problemas
- Detección de regresión
- Suspected Causes
- Error Grouping
- Bits AI Dev Agent
- Monitores
- Issue Correlation
- Identificar confirmaciones sospechosas
- Auto Assign
- Issue Team Ownership
- Rastrear errores del navegador y móviles
- Rastrear errores de backend
- Manage Data Collection
- Solucionar problemas
- Guides
- Change Tracking
- Gestión de servicios
- Objetivos de nivel de servicio (SLOs)
- Gestión de incidentes
- De guardia
- Status Pages
- Gestión de eventos
- Gestión de casos
- Actions & Remediations
- Infraestructura
- Cloudcraft
- Catálogo de recursos
- Universal Service Monitoring
- Hosts
- Contenedores
- Processes
- Serverless
- Monitorización de red
- Cloud Cost
- Rendimiento de las aplicaciones
- APM
- Términos y conceptos de APM
- Instrumentación de aplicación
- Recopilación de métricas de APM
- Configuración de pipelines de trazas
- Correlacionar trazas (traces) y otros datos de telemetría
- Trace Explorer
- Recommendations
- Code Origin for Spans
- Observabilidad del servicio
- Endpoint Observability
- Instrumentación dinámica
- Live Debugger
- Error Tracking
- Seguridad de los datos
- Guías
- Solucionar problemas
- Límites de tasa del Agent
- Métricas de APM del Agent
- Uso de recursos del Agent
- Logs correlacionados
- Stacks tecnológicos de llamada en profundidad PHP 5
- Herramienta de diagnóstico de .NET
- Cuantificación de APM
- Go Compile-Time Instrumentation
- Logs de inicio del rastreador
- Logs de depuración del rastreador
- Errores de conexión
- Continuous Profiler
- Database Monitoring
- Gastos generales de integración del Agent
- Arquitecturas de configuración
- Configuración de Postgres
- Configuración de MySQL
- Configuración de SQL Server
- Configuración de Oracle
- Configuración de MongoDB
- Setting Up Amazon DocumentDB
- Conexión de DBM y trazas
- Datos recopilados
- Explorar hosts de bases de datos
- Explorar métricas de consultas
- Explorar ejemplos de consulta
- Exploring Database Schemas
- Exploring Recommendations
- Solucionar problemas
- Guías
- Data Streams Monitoring
- Data Jobs Monitoring
- Data Observability
- Experiencia digital
- Real User Monitoring
- Pruebas y monitorización de Synthetics
- Continuous Testing
- Análisis de productos
- Entrega de software
- CI Visibility
- CD Visibility
- Deployment Gates
- Test Visibility
- Configuración
- Network Settings
- Tests en contenedores
- Repositories
- Explorador
- Monitores
- Test Health
- Flaky Test Management
- Working with Flaky Tests
- Test Impact Analysis
- Flujos de trabajo de desarrolladores
- Cobertura de código
- Instrumentar tests de navegador con RUM
- Instrumentar tests de Swift con RUM
- Correlacionar logs y tests
- Guías
- Solucionar problemas
- Code Coverage
- Quality Gates
- Métricas de DORA
- Feature Flags
- Seguridad
- Información general de seguridad
- Cloud SIEM
- Code Security
- Cloud Security Management
- Application Security Management
- Workload Protection
- Sensitive Data Scanner
- Observabilidad de la IA
- Log Management
- Observability Pipelines
- Gestión de logs
- CloudPrem
- Administración
- Gestión de cuentas
- Seguridad de los datos
- Ayuda
Bits AI Security Analyst
Este producto no es compatible con el sitio Datadog seleccionado. ().
Esta página aún no está disponible en español. Estamos trabajando en su traducción.
Si tienes alguna pregunta o comentario sobre nuestro actual proyecto de traducción, no dudes en ponerte en contacto con nosotros.
Si tienes alguna pregunta o comentario sobre nuestro actual proyecto de traducción, no dudes en ponerte en contacto con nosotros.
Overview
Bits AI Security Analyst is an autonomous AI agent that investigates Cloud SIEM signals end to end. It queries security signals and logs, and uses data-based reasoning to help security engineers investigate threat alerts and make a recommendation on the verdict of each alert signal. By reducing manual effort and analyst fatigue, Bits AI Security Analyst makes security operations smoother and more efficient.
Key capabilities
Bits AI Security Analyst investigations are autonomous. If a detection rule is enabled, Bits AI autonomously investigates signals associated with it.
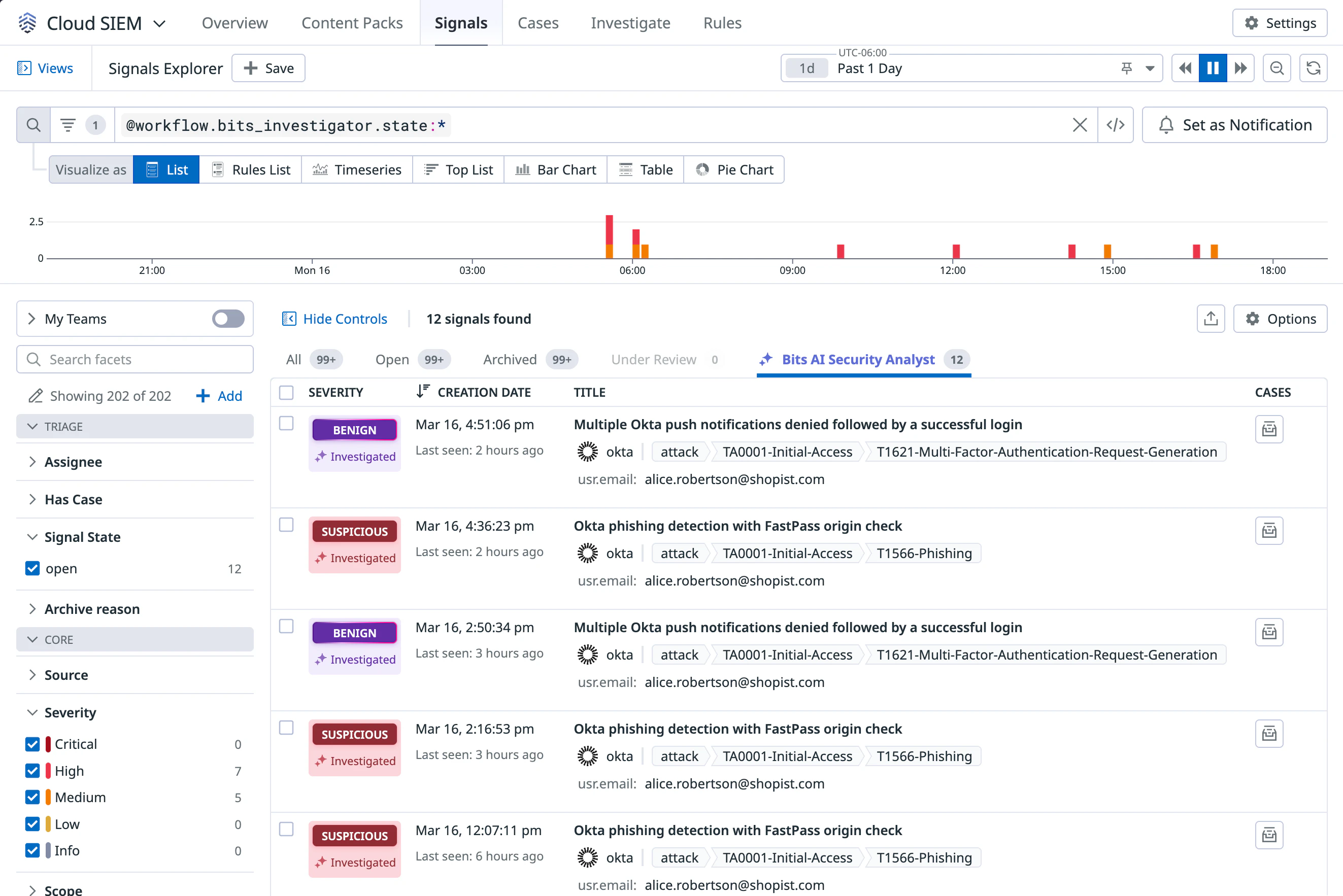
In the Cloud SIEM Signals Explorer, you can click the Bits AI Security Analyst tab to only show signals that Bits AI investigated. In the Severity column, a Bits AI status displays as Investigating, until marking the signal as either Benign or Suspicious.
When you click a row with a Bits AI investigation, the Bits AI Investigation side panel opens:
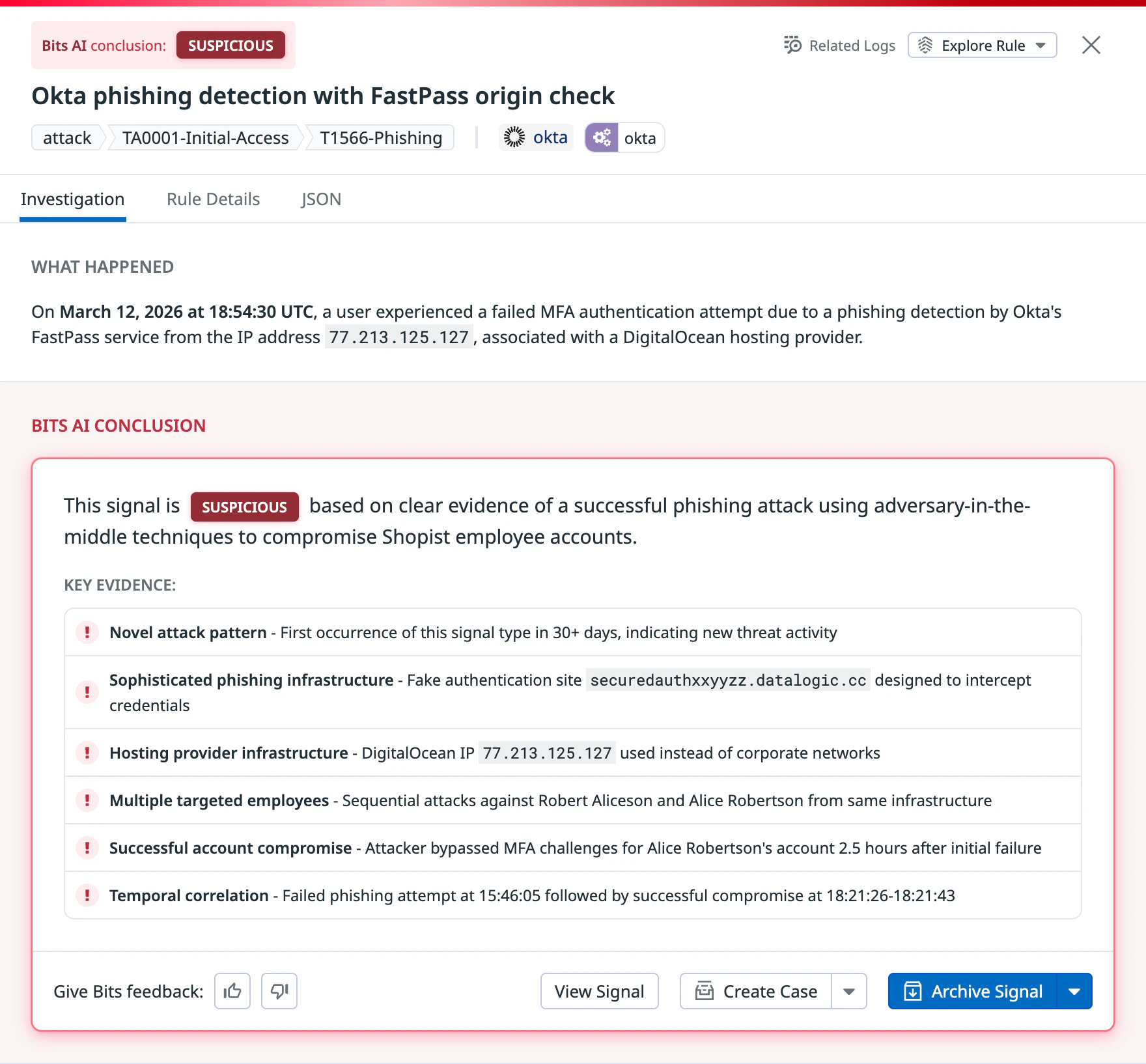
In the side panel, you can see Bits AI’s investigative findings, including:
- Overall conclusion
- Key evidence used to come to that conclusion
- Investigative steps showing Bits AI’s data queries, including embedded results and links to full queries
- Analysis on each investigative step
You can also take additional steps directly from the side panel:
- Create a case with pre-populated Bits AI investigation results
- Run a workflow with a SOAR blueprint
- Declare an incident
- Add a rule suppression
- Archive the signal, or view the signal with the usual Cloud SIEM interface
- Give Bits AI feedback on its analysis
Additionally, when you use Cloud SIEM notifications to send new signal alerts to Slack or Jira, Bits AI automatically updates those notifications. It includes replies showing the Bits AI investigative conclusion, with a link to the full investigation.
Supported sources
Bits AI can run investigations on the following Security log sources:
- AWS CloudTrail
- Azure
- GCP
- Kubernetes
- Microsoft Entra ID
- Okta
- Google Workspace
- Microsoft 365
- GitHub
- Snowflake
- SentinelOne
- Email phishing
Set up Bits AI Security Analyst
Prerequisites
To use Bits AI Security Analyst:
- Ensure your organization is using a non-legacy version of Cloud SIEM. If you need assistance, contact Datadog support.
- To set up Bits AI Security Analyst, you need the Bits AI Security Analyst Config Write permission.
- To view investigations, you must have 14 days or more of log history. If you have a shorter log history, you can still set up Bits AI Security Analyst, but won’t see any investigations until you have that much history.
Setup
When you enable Bits AI Security Analyst, Datadog analyzes your rules, including custom rules, to determine whether it can confidently investigate signals associated with them. For all eligible rules above medium severity, it starts autonomously investigating signals.
Rule eligibility depends on whether Datadog has built the investigation capability for the log source, and whether the Agent is able to investigate the specific rule. If you have new custom rules to evaluate, or want to ask about a rule that wasn’t made eligible, contact Datadog support.
- In Datadog, go to Security > Settings > Bits AI Security Analyst.
- Turn on the toggle to enable Bits AI Security Analyst. Additional settings appear.
- (Optional) Configure which rules and which severities you want Bits AI Security Analyst to automatically investigate signals for. There are two ways to do so:
- Click Rule Settings to configure investigations for individual rules. You can change the minimum severity for signals to be investigated, and enable or disable individual rules for investigation.
- Click Query Filter to write a signal query filter, so Bits AI Security Analyst only investigates signals that match your filter.
- Some log sources require credentials to run or enhance investigations by accessing logs, telemetry, or other data that isn’t in Datadog. To add credentials, click Edit credentials. In the Select or Add Connection window that opens, follow the prompts to select an existing connection from Actions Catalog, or add a connection. Datadog securely stores and restricts all credentials using Actions Catalog.
- Some log sources require additional setup so you can create HTTP connections. Here’s an example:
Configure SentinelOne
- In SentinelOne, ensure you have permission to create an API token. Create an S1 API service user, then assign the Viewer role to that user.
- In Datadog, in the Select or Add Connection window, in the dropdown, select New Connection, then click the HTTP tile.
- Add the following information:
- In the Description field, Datadog recommends adding your token expiry date, to make it easily accessible.
- In the Base URL field, enter your SentinelOne Management Console URL.
- Under Token Auth, enter a name for your token in the Token Name field, and your API token in the Token Value field.
- Click Next, Confirm Access to verify your connection.
- Some log sources require additional setup so you can create HTTP connections. Here’s an example:
Disable Bits AI Security Analyst
- In Datadog, go to Security > Settings > Bits AI Security Analyst.
- Scroll to the bottom of the page. Under Disable Bits AI Security Analyst, turn off the Enabled toggle.Disabling Bits AI Security Analyst permanently resets all configuration settings.
Further reading
Más enlaces, artículos y documentación útiles: