- 重要な情報
- はじめに
- Datadog
- Datadog サイト
- DevSecOps
- AWS Lambda のサーバーレス
- エージェント
- インテグレーション
- コンテナ
- ダッシュボード
- アラート設定
- ログ管理
- トレーシング
- プロファイラー
- タグ
- API
- Service Catalog
- Session Replay
- Continuous Testing
- Synthetic モニタリング
- Incident Management
- Database Monitoring
- Cloud Security Management
- Cloud SIEM
- Application Security Management
- Workflow Automation
- CI Visibility
- Test Visibility
- Intelligent Test Runner
- Code Analysis
- Learning Center
- Support
- 用語集
- Standard Attributes
- ガイド
- インテグレーション
- エージェント
- OpenTelemetry
- 開発者
- 認可
- DogStatsD
- カスタムチェック
- インテグレーション
- Create an Agent-based Integration
- Create an API Integration
- Create a Log Pipeline
- Integration Assets Reference
- Build a Marketplace Offering
- Create a Tile
- Create an Integration Dashboard
- Create a Recommended Monitor
- Create a Cloud SIEM Detection Rule
- OAuth for Integrations
- Install Agent Integration Developer Tool
- サービスのチェック
- IDE インテグレーション
- コミュニティ
- ガイド
- Administrator's Guide
- API
- モバイルアプリケーション
- CoScreen
- Cloudcraft
- アプリ内
- Service Management
- インフラストラクチャー
- アプリケーションパフォーマンス
- APM
- Continuous Profiler
- データベース モニタリング
- Data Streams Monitoring
- Data Jobs Monitoring
- Digital Experience
- Software Delivery
- CI Visibility (CI/CDの可視化)
- CD Visibility
- Test Visibility
- Intelligent Test Runner
- Code Analysis
- Quality Gates
- DORA Metrics
- セキュリティ
- セキュリティの概要
- Cloud SIEM
- クラウド セキュリティ マネジメント
- Application Security Management
- AI Observability
- ログ管理
- Observability Pipelines(観測データの制御)
- ログ管理
- 管理
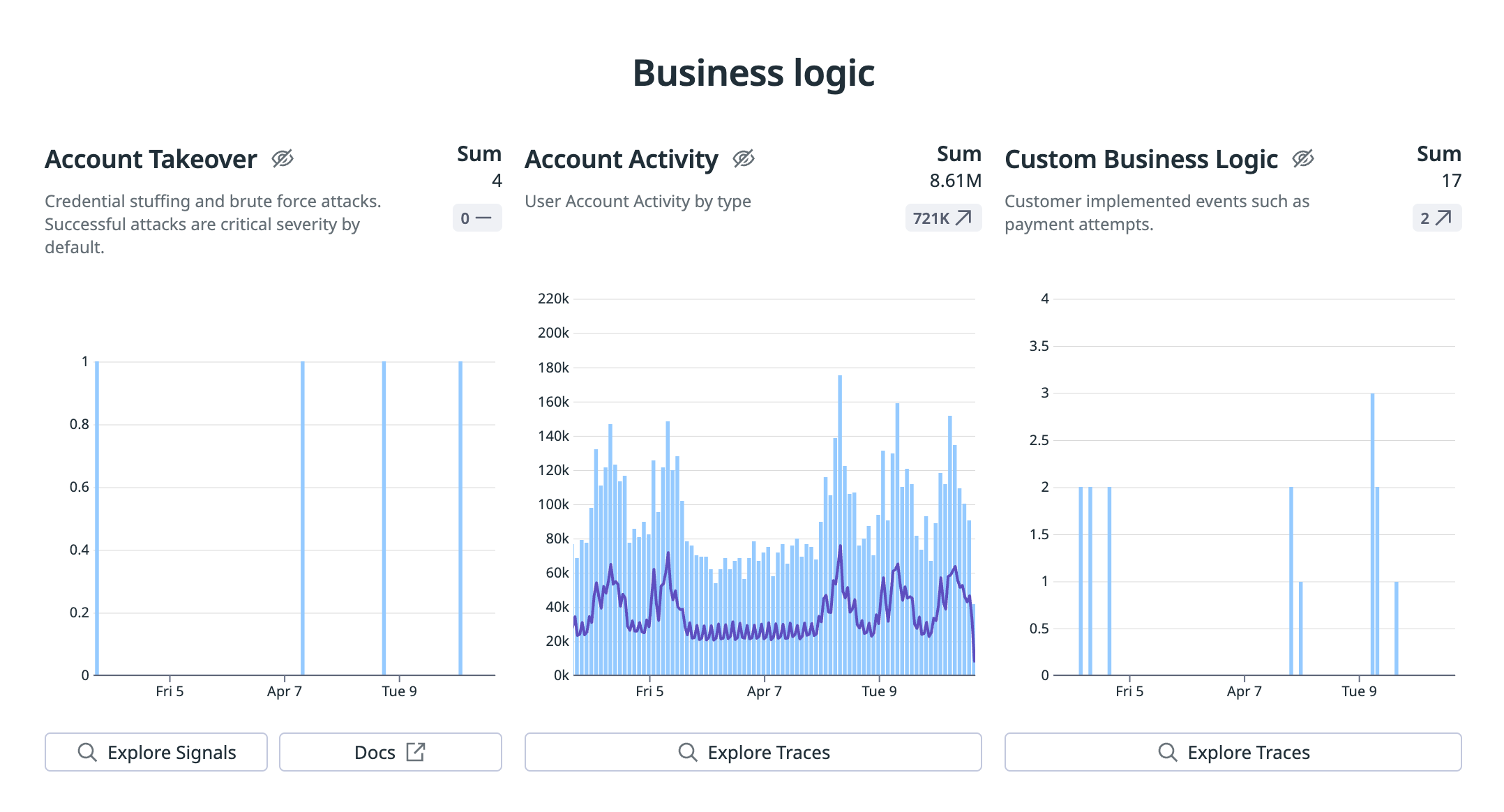
Account Takeover Protection
ASM はアカウント乗っ取り攻撃を検出および軽減するために、アカウント乗っ取り (ATO) 保護を提供します。
ATO 保護には次のような利点があります。
- 攻撃者をブロックし、ユーザーを無効にします。
- 標的とされたユーザーや侵害されたユーザーを識別します。
- 既存のユーザーとそうでないユーザーを区別します。
- 攻撃者を論理的なグループにまとめて軽減策を講じます。
アカウント乗っ取り保護の概要
アカウントの乗っ取りは、攻撃者がユーザーのアカウント資格情報にアクセスしてアカウントの制御権を奪うことで発生します。
以下の表は、ビジネス別の攻撃者の動機の一覧です。
| 金銭的窃盗 | アカウントの転売 |
|---|---|
| コンシューマーバンキングアプリ | SaaS プラットフォーム |
| クレジットカードを発行する金融サービスアプリ | ギフトカードを保管するコンシューマー向けプラットフォーム |
攻撃者の戦略
攻撃者は一般に公開されている自動化ツールを使用してユーザーのアカウント資格情報を侵害します。これらのツールの洗練度や規模はさまざまです。
一般的な戦略をいくつか紹介します。
- 資格情報スタッフィング
- 盗まれたアカウント資格情報 (ユーザー名、電子メールアドレス、パスワードなど) を使用してユーザーアカウントに不正アクセスする自動化されたサイバー攻撃です。アクセスは Web アプリケーションに対する大規模な自動ログインリクエストを通じて行われます。
- 資格情報スタッフィングは資格情報ダンプに依存しています。
- 資格情報ダンプ
- 資格情報ダンプは、セキュリティ侵害で盗まれた資格情報が公開されたり、ダーク Web 市場で販売されたりすることで発生します。この結果、大量のユーザー名、パスワード、その他のアカウント詳細が公開されることがよくあります。
- 資格情報クラッキング
- 資格情報クラッキングでは、正しいパスワードが見つかるまでさまざまなパスワードの組み合わせを系統的に試すことでユーザーのパスワードの解読を試みます。この方法では、さまざまなパスワード推測技術を用いたソフトウェアツールがよく使用されます。
- ブルートフォース
- ブルートフォースは、ユーザーのパスワードや個人識別番号 (PIN) などの情報を取得するために試行錯誤する手法です。この攻撃では、自動化を利用して連続的な推測を生成し、システムに不正アクセスを試みます。
ATO の検出と防止のセットアップ
ASM は ATO 攻撃の検出を管理します。
ATO の効果的な検出と防止には以下が必要です。
- 本番ログインエンドポイントのインスツルメンテーション。これにより、ASM 管理のルールによる検出が可能になります。
- リモート構成。これにより、Datadog ユーザーインターフェイスから攻撃をブロックし、リモートインスツルメンテーションをプッシュできます。
- 通知。侵害されたアカウントを通知することができます。
- 最初の検出を確認します。自動化された保護が攻撃やエスカレーションの要件にどのように適合するかを理解します。
本番ログインエンドポイントのインスツルメンテーション
ATO の追跡には以下のユーザーアクティビティイベントが使用されます。
| リッチ化 | 自動インスツルメンテーション | 使用例 |
|---|---|---|
users.login.success | 真 | アカウント乗っ取り検出ルール要件 |
users.login.failure | 真 | アカウント乗っ取り検出ルール要件 |
users.password_reset | 偽 | パスワードリセットによるユーザー列挙を識別する検出ルール要件 |
これらの付加情報では、usr.id としてユーザー識別子 (固有ユーザー、数値、その他) を保持する必要があります。ログインが失敗した場合、そのユーザーがデータベース上に存在していたかどうか (usr.exists) も把握する必要があります。これは、存在しないアカウントを定期的に狙う悪意のある活動を特定するのに役立ちます。
自動的にインスツルメンテーションされないイベントの追跡を有効にする手順については、ユーザーの監視と保護を参照してください。
関連する検出とインスツルメンテーション要件の最新リストについては、検出ルールページを参照してください。
自動インスツルメンテーションは、数多くの認証方式におけるユーザーのログイン成功・失敗を自動的に検知する Datadog 機能です。
Datadog がこれらのエンリッチメントを定義する方法に制限はありません。多くのプラットフォーム製品では、顧客組織やユーザーロールの識別など、他のエンリッチメントを追加できます。
リモート構成
Remote Configuration によって、ASM ユーザーは、ほぼリアルタイムでカスタム ビジネスロジック データをアプリにインスツルメントすることができます。
通知
通知は、攻撃を適切なチームメンバーに確実に通知するための柔軟な方法です。一般的なコミュニケーション方法とのコラボレーションインテグレーションはすぐに使えます。
最初の検出をレビュー
ASM は、検出タイプに基づいて最も関連性の高い情報をハイライトし、取るべきアクションを提案します。また、どのようなアクションが実行されたかも表示されます。
Compromised Users
Signals と Traces では、侵害されたユーザーと標的とされたユーザーを確認し、ブロックすることができます。
Signals
個々のユーザーは、Targeted Users を使用して Signals でブロックできます。
Traces
個々のユーザーは、User の Traces でブロックできます。このオプションを表示するには、任意のユーザーをクリックしてください。
シグナルの確認と保護のベストプラクティス
アカウント乗っ取り攻撃を検出および軽減するために、以下のベストプラクティスを確認してください。
インシデント対応計画の策定
インシデント対応計画を策定するために、次のセクションを確認してください。
認証済みスキャナーを使用していますか?
信頼できる IP を特定し、自動的にブロックされないようにします。この手順は、次の場合に役立ちます:
- ログインを試みる承認されたスキャンソース。
- 単一の IP アドレスの背後に多数のユーザーを持つ企業サイト。
信頼済み IP を構成するには、Passlist を使用して、Monitored エントリを追加します。監視対象エントリは自動ブロックから除外されます。
顧客の認証プロファイルを把握
以下のような、顧客が認証するネットワークを確認します。
- モバイル ISP
- 企業 VPN
- 住宅用 IP
- データセンター
認証ソースを理解することは、ブロッキング戦略に役立ちます。
例えば、あなたは顧客がデータセンターからコンシューマーアプリケーションで認証を行うことを想定していないかもしれません。その場合、そのデータセンターに関連する IP をブロックする自由度が高まります。
それにもかかわらず、顧客がモバイル ISP から全てを発信している場合、それらの ISP をブロックすると、正当なトラフィックに影響を与える可能性があります。
あなたの顧客がどのような人たちなのか、そして彼らのアカウント名の構造を考えてみてください。
あなたの顧客はこれらの属性に一致していますか?
- 整数、企業ドメイン、数字とテキストの組み合わせなど、予想される ID 形式を持つ従業員。
- 顧客企業に関連するドメイン名を使用している SaaS の顧客。
- Gmail や Proton Mail などの無料プロバイダーを使用しているコンシューマー。
顧客のアカウント名の構造を理解することで、攻撃が標的型なのか、それとも大量の資格情報を無差別に試すような攻撃なのかを判断することができます。
分散攻撃
攻撃は可用性、ユーザーの資金、および正規ユーザーに影響を与える可能性があるため、高度な分散攻撃については、多くの場合、ビジネス上の意思決定の上ブロックすることになります。
このような攻撃を軽減するための 3 つの重要なコンポーネントを紹介します。
- 適切なオンボーディング: ASM によるブロックの構成はできていますか?
- 適切な構成: クライアント IP と X-Forwarded-For (XFF) HTTP ヘッダーを正しく設定していますか?
- 内部コミュニケーション計画: セキュリティチーム、サービスオーナー、製品リードとのコミュニケーションは、大規模攻撃の軽減による影響を理解する上で非常に重要です。
対応者は、すべての ASM シグナルに含まれるタグを使用して、サービスオーナーを特定することができます。
傾向を知る
Threats Overview を使用して、サービスに対するログイン失敗の急増など、ビジネスロジックの傾向を監視します。
シグナルの確認
シグナルに関する以下のベストプラクティスを確認してください。
IP アドレス
攻撃者のブロックには短い時間を使用します。15 分以内を推奨します。攻撃者が分散型のアカウント乗っ取りで IP アドレスを再利用することは稀です。
データセンター
安価な仮想プライベートサーバー (VPS) やホスティングプロバイダーを利用した攻撃もあります。攻撃者の動機は、低コストで自動化されているため、データセンターで新しい IP アドレスにアクセスできることにあります。
多くのコンシューマーアプリケーションでは、データセンター、特に低コストのデータセンターや VPS プロバイダーからのユーザー認証の発生率は低いです。ネットワーク範囲が小さく、想定されるユーザー認証動作の範囲内にない場合は、データセンターまたは ASN 全体をブロックすることを検討してください。
Datadog は、IPinfo や Spur などのサードパーティのデータソースを使用して、IP がホスティングプロバイダーであるかどうかを判断します。Datadog はこのデータを Datadog インフラストラクチャー内で処理します。
プロキシ
Datadog は Spur を使用して、IP がプロキシであるかどうかを判断します。Datadog は、ASM が管理するアカウント乗っ取りルールでより迅速に検出するために、侵害の指標 (IOC) とアカウント乗っ取り攻撃を相関させます。
Datadog は、IP アドレスの脅威インテリジェンス IOC のみに基づいて IP アドレスをブロックしないことを推奨します。詳しくは、脅威インテリジェンスのベストプラクティスを参照してください。
所有権や脅威インテリジェンスを含む IP の詳細は、IP アドレスの詳細で確認できます。これらの詳細を表示するには、IP アドレスをクリックしてください。
分散型アカウント乗っ取りでは、2 種類のプロキシが頻繁に見られます。
ホスティングプロキシ: データセンターに存在するプロキシで、多くの場合、データセンターのホストが侵害された結果です。ホスティングプロキシとやりとりするためのガイダンスはデータセンターと同様です。
レジデンシャルプロキシ: 住宅用 IP の背後に存在するプロキシ。レジデンシャルプロキシは、モバイルアプリケーション SDK またはブラウザのプラグインによって有効化されることがよくあります。SDK またはプラグインのユーザーは通常、プロキシを実行していることに気づきません。レジデンシャルプロキシとして識別された IP アドレスから良性のトラフィックが発生することはよくあります。
モバイル ISP
Datadog は、IPinfo や Spur などのサードパーティを使用して、IP がモバイル ISP であるかどうかを判断します。
モバイル ISP をブロックする場合は注意してください。モバイル ISP は CGNAT を使用し、頻繁に各 IP アドレスの背後に多数の電話を持っています。
攻撃者の属性
攻撃者の属性を使用して、レスポンスアクションの目標を設定します。
Datadog は、攻撃者の属性の類似性によって攻撃者をクラスター化します。対応者はカスタムルールを使用して、しつこい攻撃者の属性をブロックすることができます。
保護
保護に関する以下のベストプラクティスを確認してください。
自動化された保護
管理されたルールセットを評価し、どのルールが社内の自動ブロックポリシーに適合するかを判断します。
ポリシーがない場合は、既存の検出を確認し、Signals で推奨される対応から始めます。長期間にわたって実行された最も関連性の高いアクションに基づいてポリシーを構築します。
ユーザー
Signals では、What Happened および Targeted Users セクションに、試行されたユーザー名の例が示されています。
Traces セクションでは、ユーザーが存在するかどうかを識別します。ユーザーが存在するかどうかを理解することは、インシデント対応の決定に影響します。
以下の侵害後の手順を使用して、インシデント対応計画を策定します。
- 侵害されたユーザーアカウントの監視
- 資格情報の無効化を計画し、資格情報を更新するようユーザーに連絡します。
- ASM を使用してユーザーをブロックすることを検討します。
攻撃の動機は、侵害後のアクティビティに影響を与えます。アカウントの転売を目的とする攻撃者は、侵害直後にアカウントを使用する可能性は低いでしょう。 貯蓄された資金にアクセスしようとする攻撃者は、侵害後すぐにアカウントを使用します。
攻撃者のブロックに加え、侵害されたユーザーのブロックを検討してください。
参考資料
お役に立つドキュメント、リンクや記事: