- 重要な情報
- はじめに
- Datadog
- Datadog サイト
- DevSecOps
- AWS Lambda のサーバーレス
- エージェント
- インテグレーション
- コンテナ
- ダッシュボード
- アラート設定
- ログ管理
- トレーシング
- プロファイラー
- タグ
- API
- Service Catalog
- Session Replay
- Continuous Testing
- Synthetic モニタリング
- Incident Management
- Database Monitoring
- Cloud Security Management
- Cloud SIEM
- Application Security Management
- Workflow Automation
- CI Visibility
- Test Visibility
- Intelligent Test Runner
- Code Analysis
- Learning Center
- Support
- 用語集
- Standard Attributes
- ガイド
- インテグレーション
- エージェント
- OpenTelemetry
- 開発者
- 認可
- DogStatsD
- カスタムチェック
- インテグレーション
- Create an Agent-based Integration
- Create an API Integration
- Create a Log Pipeline
- Integration Assets Reference
- Build a Marketplace Offering
- Create a Tile
- Create an Integration Dashboard
- Create a Recommended Monitor
- Create a Cloud SIEM Detection Rule
- OAuth for Integrations
- Install Agent Integration Developer Tool
- サービスのチェック
- IDE インテグレーション
- コミュニティ
- ガイド
- Administrator's Guide
- API
- モバイルアプリケーション
- CoScreen
- Cloudcraft
- アプリ内
- Service Management
- インフラストラクチャー
- アプリケーションパフォーマンス
- APM
- Continuous Profiler
- データベース モニタリング
- Data Streams Monitoring
- Data Jobs Monitoring
- Digital Experience
- Software Delivery
- CI Visibility (CI/CDの可視化)
- CD Visibility
- Test Visibility
- Intelligent Test Runner
- Code Analysis
- Quality Gates
- DORA Metrics
- セキュリティ
- セキュリティの概要
- Cloud SIEM
- クラウド セキュリティ マネジメント
- Application Security Management
- AI Observability
- ログ管理
- Observability Pipelines(観測データの制御)
- ログ管理
- 管理
Datadog の Lambda 関数で AWS サービスのログを送信する
AWS サービスログは、Datadog Forwarder Lambda 関数を使用して収集できます。S3 Buckets、CloudWatch ロググループ、および EventBridge イベントでトリガーするこの Lambda は、ログを Datadog に転送します。
AWS サービスからログの収集を開始するには
- AWS アカウントで Datadog Forwarder Lambda 関数をセットアップします。
- AWS サービスでログを有効にします (大部分の AWS サービスは、S3 バケットまたは CloudWatch ログ グループにログインできます)。
- 転送する新しいログがあったときに Forwarder Lambda を実行させるトリガーの設定をします。トリガーの構成は 2 通りあります。
注: AWS us-east-1 リージョンにいる場合は、Datadog-AWS Private Link を利用してください。
注: Cloudformation は、すべてのリソースに対して KMS:Decrypt を含む IAM ポリシーを作成し、AWS Security Hub のベストプラクティスと一致しません。この権限は、Lambda 関数を設定するために KMS で暗号化された S3 バケットからオブジェクトを復号するために使用され、どの KMS キーが S3 バケットの暗号化に使用されているかは予測できません。インストーラーが正常に終了したら、この権限を安全に削除することができます。
AWS サービスのログを有効にする
S3 バケットまたは CloudWatch ロググループにログを生成する AWS サービスがサポートされています。以下の表で、よく使用されるサービスのセットアップ手順を参照してください。
| AWS サービス | AWS サービス ログを有効にする | AWS ログを Datadog に送信する |
|---|---|---|
| API Gateway | Amazon API Gateway ログを有効にする | 手動および自動ログコレクション。 |
| Cloudfront | Amazon CloudFront ログを有効にする | 手動および自動ログコレクション。 |
| CloudTrail | AWS CloudTrail ログを有効にする | 手動ログコレクション。AWS CloudTrail for Cloud SIEM を設定する場合は、AWS Configuration for Cloud SIEM11 を参照してください。 |
| DynamoDB | Amazon DynamoDB ログを有効にする | 手動ログコレクション。 |
| EC2 | - | Datadog Agent を使用してログを Datadog に送信します。 |
| ECS | - | docker Agent を使用してログを収集します。 |
| Elastic Load Balancing (ELB) | Amazon ELB ログを有効にする | 手動および自動ログコレクション。 |
| Lambda | - | 手動および自動ログコレクション。 |
| RDS | Amazon RDS ログを有効にする | 手動ログコレクション。 |
| Route 53 | Amazon Route 53 ログを有効にする | 手動ログコレクション。 |
| S3 | Amazon S3 ログを有効にする | 手動および自動ログコレクション。 |
| SNS | SNS はログを提供しませんが、SNS サービスに送信されるログとイベントを処理することができます。 | 手動ログコレクション。 |
| RedShift | Amazon Redshift ログを有効にする | 手動および自動ログコレクション。 |
| Verified Access | Verified Access ログを有効にする | 手動ログコレクション。 |
| VPC | Amazon VPC ログを有効にする | 手動ログコレクション。 |
| Step Functions | Amazon Step Functions ログを有効にする | 手動ログ収集。 |
| Web Application Firewall | Amazon WAF ログを有効にする | 手動および[自動][#automatically-set-up-triggers]ログ収集。 |
| MWAA | Amazon MWAA ログを有効にする | 手動ログ収集。 |
トリガーの設定
Datadog Forwarder Lambda 関数でトリガーを構成する場合、オプションは 2 つあります。
- 自動: Datadog は、選択されている AWS サービスのログロケーションを自動的に受信し、Datadog Forwarder Lambda 関数のトリガーとして追加します。また、リストを最新状態に維持します。
- 手動: 各トリガーをセットアップします。
トリガーを自動的にセットアップする
Datadog は、Datadog Forwarder Lambda 関数にトリガーを自動的に構成し、以下のソースとロケーションから AWS ログを収集することができます。
| ソース | 所在地 |
|---|---|
APIKEY を AccessKey ボックスに貼り付けます (Datadog API 設定ページから API キーを取得できます)。 | CloudWatch |
| API ゲートウェイの実行ログ | CloudWatch |
| アプリケーション ELB アクセスログ | S3 |
| クラシック ELB アクセスログ | S3 |
| CloudFront のアクセスログ | S3 |
| Lambda ログ | CloudWatch |
| Redshift ログ | S3 |
| S3 アクセスログ | S3 |
| Step Functions | CloudWatch |
| Web Application Firewall | S3、CloudWatch |
注: サブスクリプション フィルターは、DatadogForwarder によって自動的に作成されません。ロググループで直接作成してください。
Datadog ログコレクション AWS Lambda 関数をまだセットアップしていない場合は、セットアップします。
Datadog と AWS のインテグレーションに使用する IAM ロールのポリシーに、次のアクセス許可があることを確認します。この許可の使用方法については、以下に説明されています。
"cloudfront:GetDistributionConfig", "cloudfront:ListDistributions", "elasticloadbalancing:DescribeLoadBalancers", "elasticloadbalancing:DescribeLoadBalancerAttributes", "lambda:List*", "lambda:GetPolicy", "redshift:DescribeClusters", "redshift:DescribeLoggingStatus", "s3:GetBucketLogging", "s3:GetBucketLocation", "s3:GetBucketNotification", "s3:ListAllMyBuckets", "s3:PutBucketNotification", "states:ListStateMachines", "states:DescribeStateMachine", "wafv2:ListLoggingConfigurations", "logs:PutSubscriptionFilter", "logs:DeleteSubscriptionFilter", "logs:DescribeSubscriptionFilters"AWS アクセス許可 説明 cloudfront:GetDistributionConfigCloudFront アクセスログを含む S3 バケットの名前を取得します。 cloudfront:ListDistributionsすべての CloudFront ディストリビューションを一覧表示します。 elasticloadbalancing:DescribeLoadBalancersすべてのロードバランサーを一覧表示します。 ロググループインデックスページ の Subscriptionsをチェックして、新しい Kinesis ストリームがロググループをサブスクライブしているかを確認します。lambda:List*すべての Lambda 関数を一覧表示します。 lambda:GetPolicyトリガーが解除された際に Lambda ポリシーを取得します。 redshift:DescribeClustersすべての Redshift クラスターを一覧表示します。 redshift:DescribeLoggingStatusRedshift ログを含む S3 バケットの名前を取得します。 s3:GetBucketLoggingS3 アクセスログを含む S3 バケットの名前を取得します。 s3:GetBucketLocationS3 アクセスログを含む S3 バケットのリージョンを取得します。 s3:GetBucketNotification既存の Lambda トリガーコンフィギュレーションを取得します。 お役に立つドキュメント、リンクや記事:
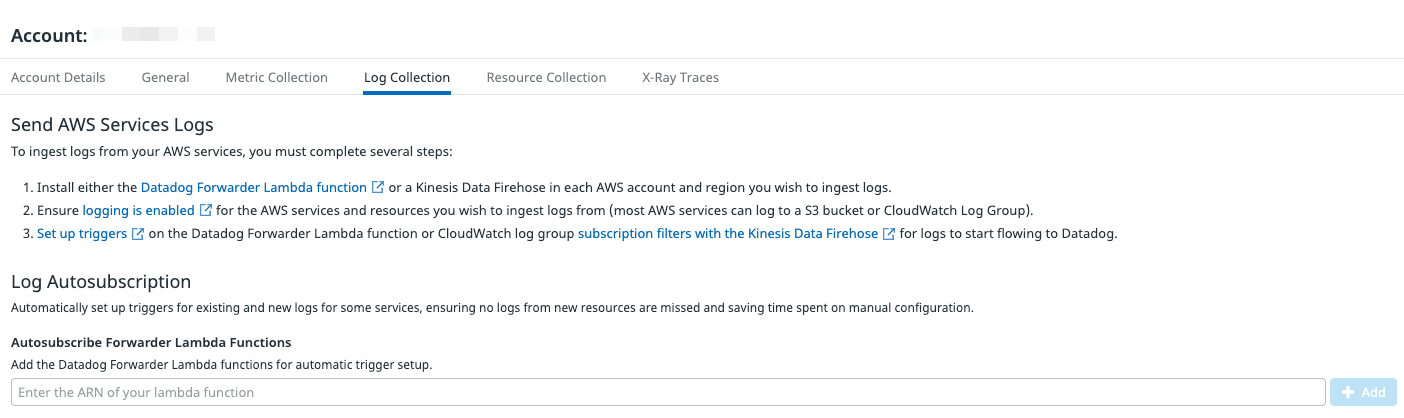
s3:PutBucketNotificationS3 バケットのイベントに基づいて Lambda トリガーを追加または削除します。 states:ListStateMachinesすべての Step Function を一覧表示します。 states:DescribeStateMachineStep Function に関するログの詳細を取得します。 wafv2:ListLoggingConfigurationsWeb Application Firewall のすべてのログ構成を一覧表示します。 logs:PutSubscriptionFilterCloudWatch ログのイベントに基づいて Lambda トリガーを追加します。 logs:DeleteSubscriptionFilterCloudWatch ログのイベントに基づいて Lambda トリガーを削除します。 logs:DescribeSubscriptionFilters特定のロググループのサブスクリプションフィルターを一覧表示します。 AWS インテグレーションページで、ログを収集する AWS アカウントを選択し、Log Collection タブをクリックします。
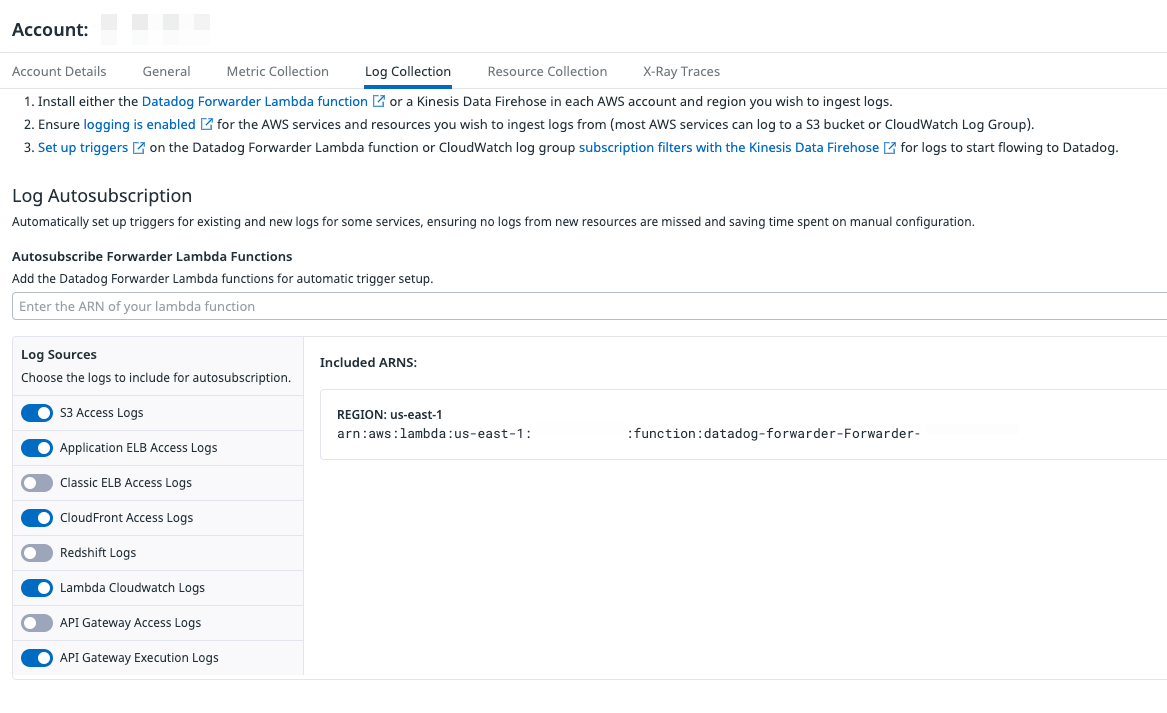
前のセクションで作成した Lambda の ARN を入力し、Add をクリックします。
ログを収集するサービスを選択し、Save をクリックします。特定のサービスからのログの収集を停止するには、ログソースの選択を解除します。
複数のリージョンにログがある場合は、そのリージョンに追加の Lambda 関数を作成して、このページに入力する必要があります。
すべての AWS ログの収集を停止するには、Lambda にカーソルを合わせ、Delete アイコンをクリックします。その関数のトリガーがすべて削除されます。
この初期のセットアップから数分以内に、AWS ログが Datadog ログエクスプローラーに表示されるようになります。
手動でトリガーをセットアップする
CloudWatch ロググループからログを収集する
CloudWatch のロググループからログを収集している場合、以下のいずれかの方法で Datadog Forwarder Lambda 関数へのトリガーを構成します。
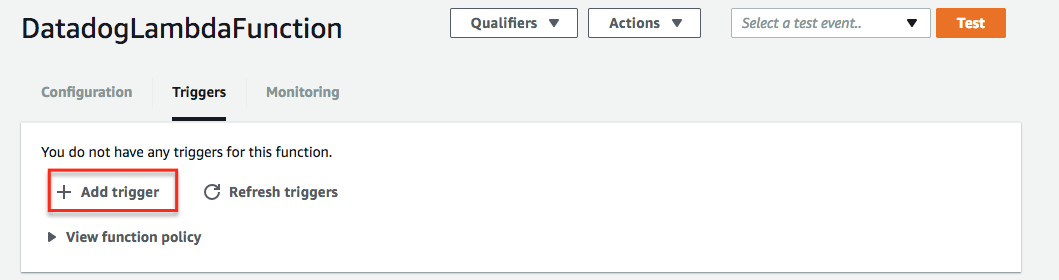
- AWS コンソールで、Lambda に移動します。
- Functions をクリックし、Datadog Forwarder を選択します。
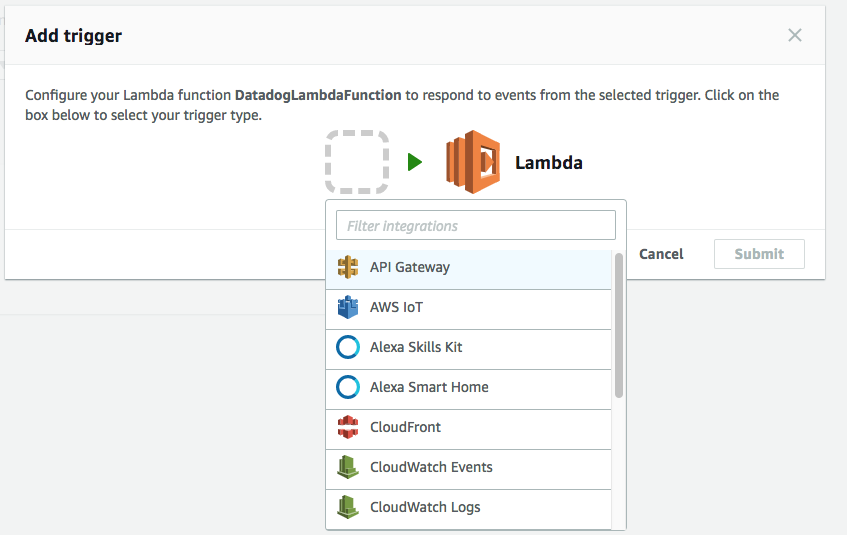
- Add trigger をクリックし、CloudWatch Logs を選択します。
- ドロップダウンメニューからロググループを選択します。
- フィルターの名前を入力し、オプションでフィルターパターンを指定します。
- Add をクリックします。
- Datadog Log セクションにアクセスし、ロググループに送信された新しいログイベントを確認します。
Terraform ユーザーは、aws_cloudwatch_log_subscription_filter リソースを使いトリガーのプロビジョニングと管理ができます。以下のサンプルコードを参照してください。
resource "aws_cloudwatch_log_subscription_filter" "datadog_log_subscription_filter" {
name = "datadog_log_subscription_filter"
log_group_name = <CLOUDWATCH_LOG_GROUP_NAME> # 例: /aws/lambda/my_lambda_name
destination_arn = <DATADOG_FORWARDER_ARN> # 例: arn:aws:lambda:us-east-1:123:function:datadog-forwarder
filter_pattern = ""
}
AWS CloudFormation ユーザーは、CloudFormation AWS::Logs::SubscriptionFilter リソースを使いトリガーのプロビジョニングと管理ができます。以下のサンプルコードを参照してください。
このサンプルコードは、AWS の SAM と Serverless Framework でも動作します。Serverless Framework の場合は、serverless.yml の resources セクションにコードを記述してください。
Resources:
MyLogSubscriptionFilter:
Type: "AWS::Logs::SubscriptionFilter"
Properties:
DestinationArn: "<DATADOG_FORWARDER_ARN>"
LogGroupName: "<CLOUDWATCH_LOG_GROUP_NAME>"
FilterPattern: ""
S3 バケットからログを収集する
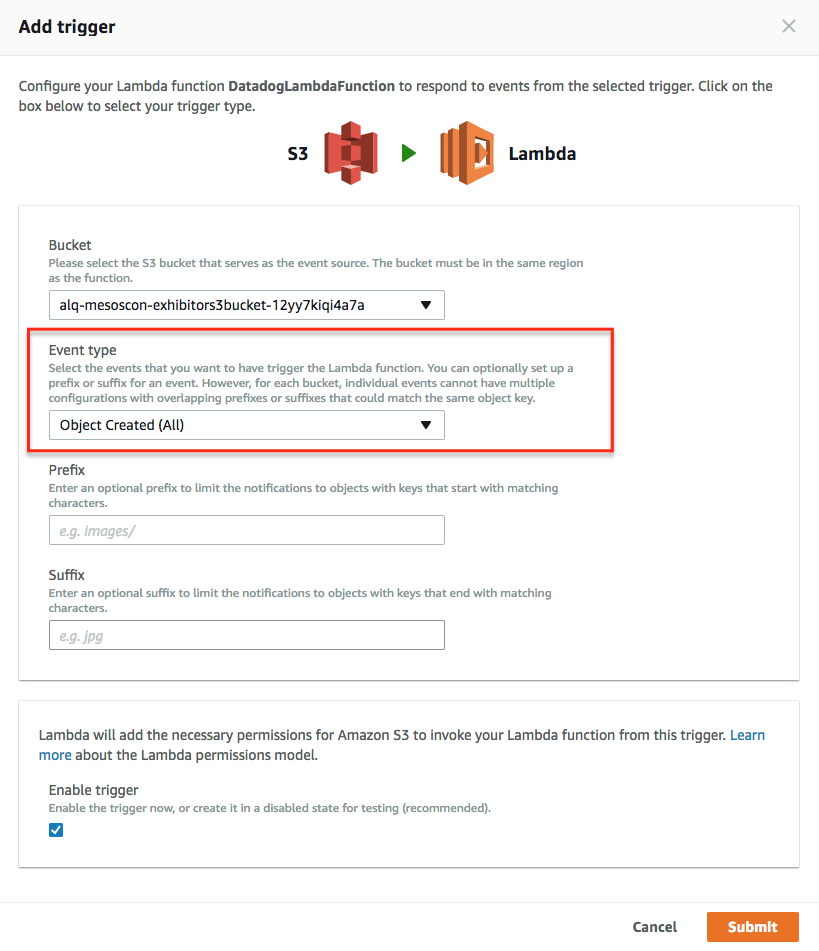
S3 バケットからログを収集している場合、以下のいずれかの方法で Datadog Forwarder Lambda 関数へのトリガーを構成します。
Lambda 関数がインストールされたら、AWS コンソールから手動で、ログを含む S3 バケットにトリガーを追加します。
バケットを選択して AWS の指示に従います。
S3 バケットで正しいイベントタイプを設定します。
完了したら、Datadog Log セクションに移動し、ログを確認します。
Terraform ユーザーは、aws_s3_bucket_notification リソースを使用してトリガーのプロビジョニングと管理ができます。以下のサンプルコードを参照してください。
resource "aws_s3_bucket_notification" "my_bucket_notification" {
bucket = my_bucket
lambda_function {
lambda_function_arn = "<DATADOG_FORWARDER_ARN>"
events = ["s3:ObjectCreated:*"]
filter_prefix = "AWSLogs/"
filter_suffix = ".log"
}
}
CloudFormation をご利用の方は、S3 バケットの CloudFormation NotificationConfiguration を利用してトリガーを構成することが可能です。以下のサンプルコードをご参照ください。
Resources:
Bucket:
Type: AWS::S3::Bucket
Properties:
BucketName: "<MY_BUCKET>"
NotificationConfiguration:
LambdaConfigurations:
- Event: 's3:ObjectCreated:*'
Function: "<DATADOG_FORWARDER_ARN>"
スクラビングとフィルター
Lambda 関数から送信されるログからメールや IP アドレスをスクラブしたり、カスタムスクラブルールを Lambda パラメーターで定義することができます。 また、フィルターオプションを使用して、特定のパターンに一致するログのみを除外または送信することができます。
参考資料
お役に立つドキュメント、リンクや記事: