- 重要な情報
- はじめに
- Datadog
- Datadog サイト
- DevSecOps
- AWS Lambda のサーバーレス
- エージェント
- インテグレーション
- コンテナ
- ダッシュボード
- アラート設定
- ログ管理
- トレーシング
- プロファイラー
- タグ
- API
- Service Catalog
- Session Replay
- Continuous Testing
- Synthetic モニタリング
- Incident Management
- Database Monitoring
- Cloud Security Management
- Cloud SIEM
- Application Security Management
- Workflow Automation
- CI Visibility
- Test Visibility
- Intelligent Test Runner
- Code Analysis
- Learning Center
- Support
- 用語集
- Standard Attributes
- ガイド
- インテグレーション
- エージェント
- OpenTelemetry
- 開発者
- 認可
- DogStatsD
- カスタムチェック
- インテグレーション
- Create an Agent-based Integration
- Create an API Integration
- Create a Log Pipeline
- Integration Assets Reference
- Build a Marketplace Offering
- Create a Tile
- Create an Integration Dashboard
- Create a Recommended Monitor
- Create a Cloud SIEM Detection Rule
- OAuth for Integrations
- Install Agent Integration Developer Tool
- サービスのチェック
- IDE インテグレーション
- コミュニティ
- ガイド
- Administrator's Guide
- API
- モバイルアプリケーション
- CoScreen
- Cloudcraft
- アプリ内
- Service Management
- インフラストラクチャー
- アプリケーションパフォーマンス
- APM
- Continuous Profiler
- データベース モニタリング
- Data Streams Monitoring
- Data Jobs Monitoring
- Digital Experience
- Software Delivery
- CI Visibility (CI/CDの可視化)
- CD Visibility
- Test Visibility
- Intelligent Test Runner
- Code Analysis
- Quality Gates
- DORA Metrics
- セキュリティ
- セキュリティの概要
- Cloud SIEM
- クラウド セキュリティ マネジメント
- Application Security Management
- AI Observability
- ログ管理
- Observability Pipelines(観測データの制御)
- ログ管理
- 管理
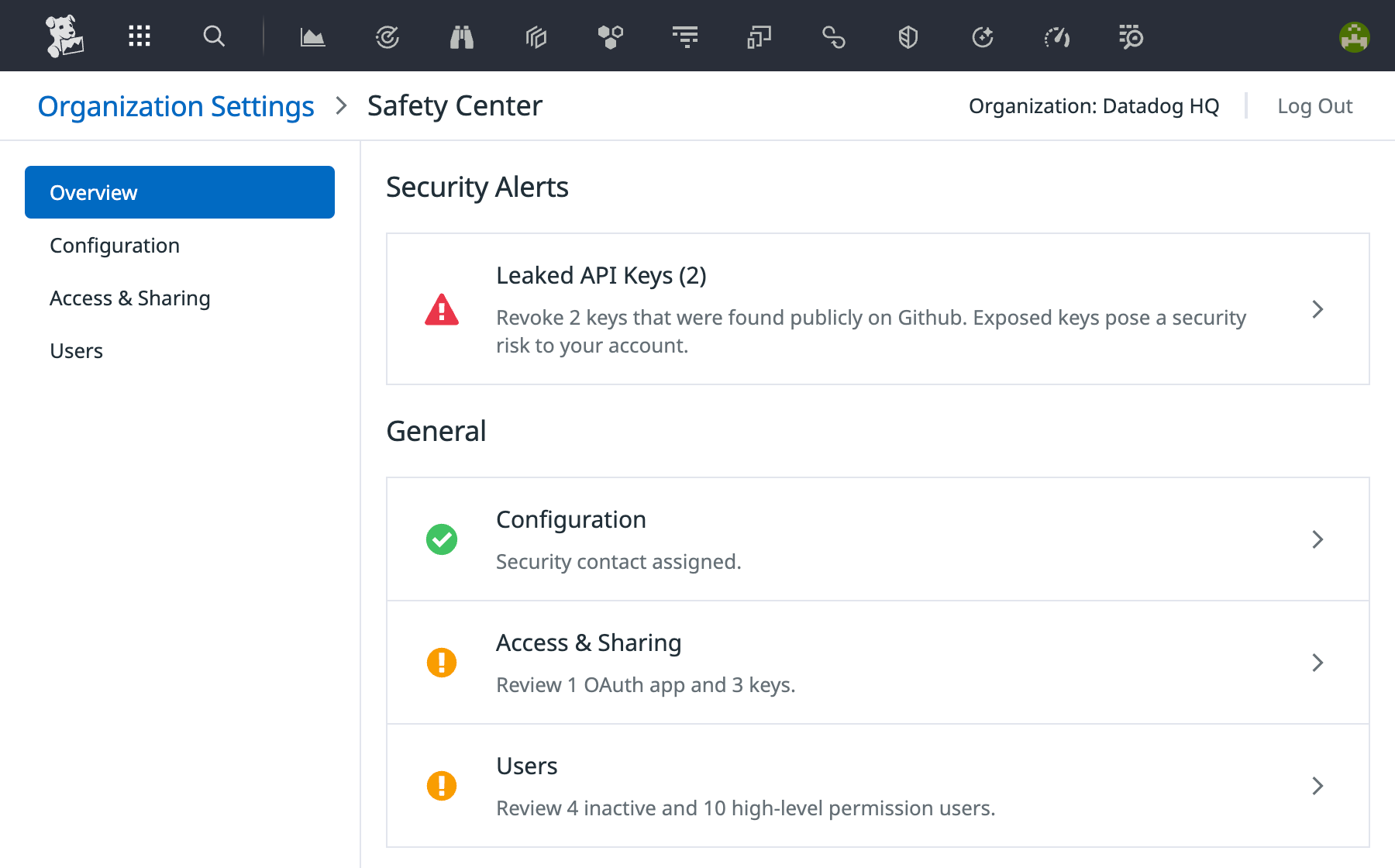
Safety Center
概要
Datadog の Safety Center は Organization Settings 内にある、セキュリティアラートとベストプラクティスを一元管理する場所です。組織の管理者はこのページを開いて、推奨事項を確認し、高優先度のセキュリティ警告やアラートに対して対策を講じることができます。
セキュリティアラート
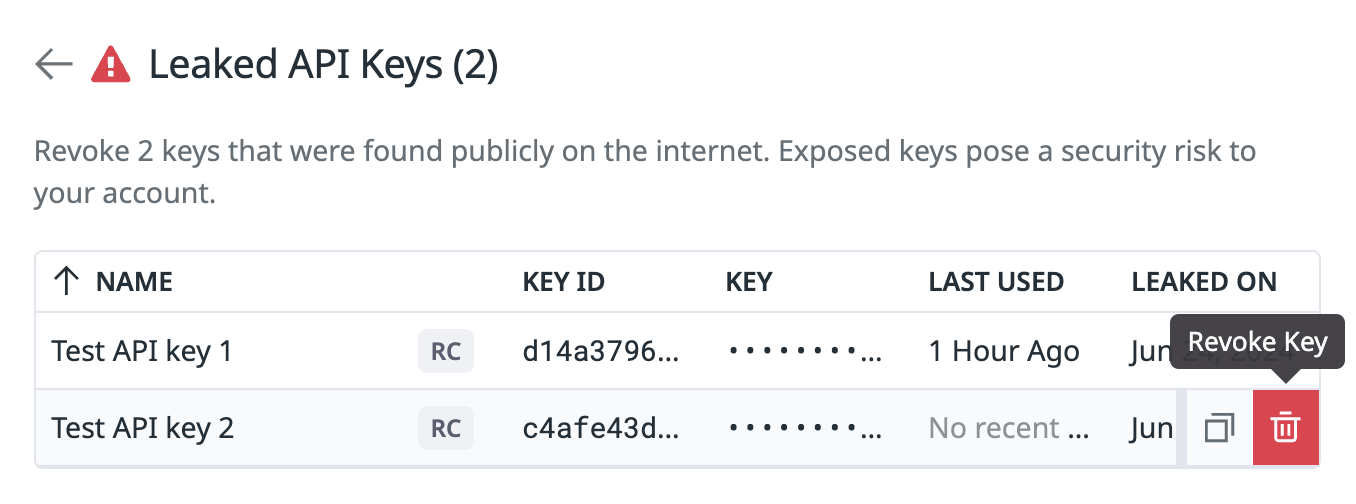
組織に高優先度のセキュリティアラートがある場合、Safety Center の Security Alerts セクションに表示されます。 Safety Center は、漏洩したアプリケーションキーと漏洩した API キーの 2 種類のアラートをサポートします。
キーの漏洩アラートは、1 つ以上のプライベートキー (アプリケーションまたは API) が侵害されたか、インターネット上で公開されたことを意味します。公開されたキーは、組織のセキュリティリスクを最小限に抑えるために、できるだけ早く取り消す必要があります。 GitHub などの公開サイトからキーを含むファイルを削除しても、他の第三者が既にアクセスしていないことを保証するものではありません。
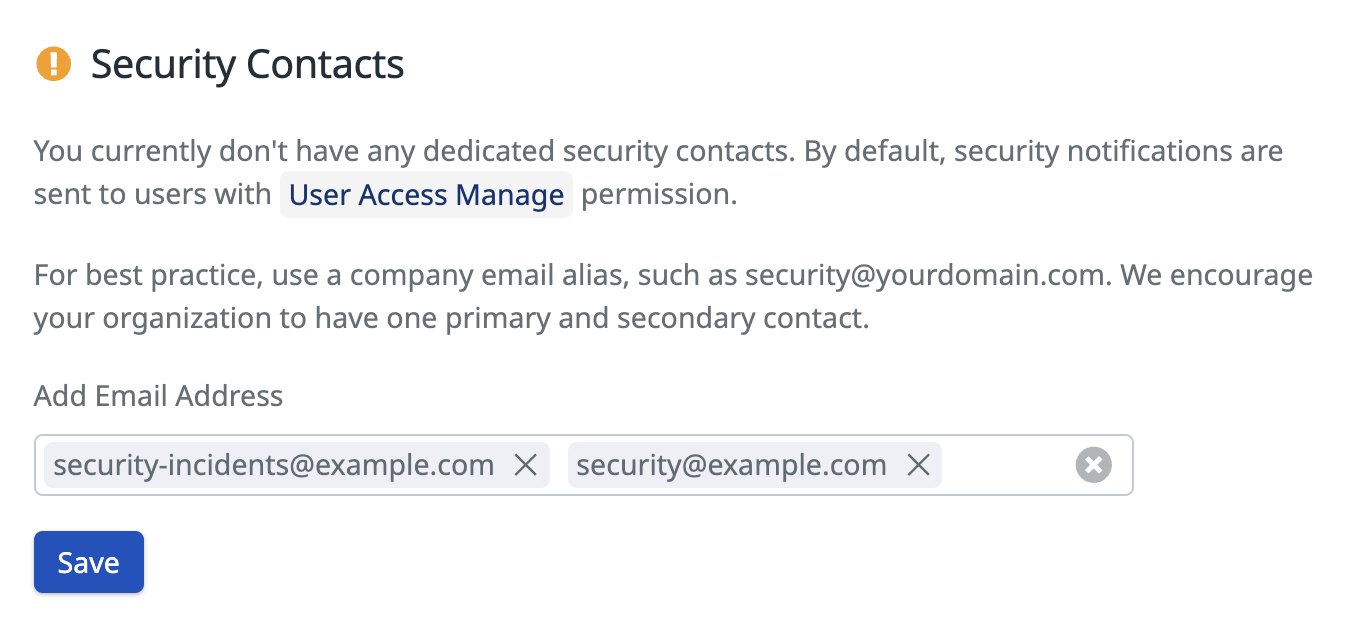
構成
Safety Center の Configuration タブでは、Security Contacts を設定できます。これは、 Datadog 組織のセキュリティ通知を受け取る一次および二次のメールアドレスです。Datadog キーが公開されたためにローテーションが必要であるなどのセキュリティ問題が検出されると、割り当てられた Security Contacts に通知されます。
潜在的なセキュリティリスクが迅速に対処および緩和されるように、Security Contacts を最新の状態に保つことが重要です。Safety Center ページは、6 か月ごとに割り当てられた Security Contacts を見直すようリマインドします。
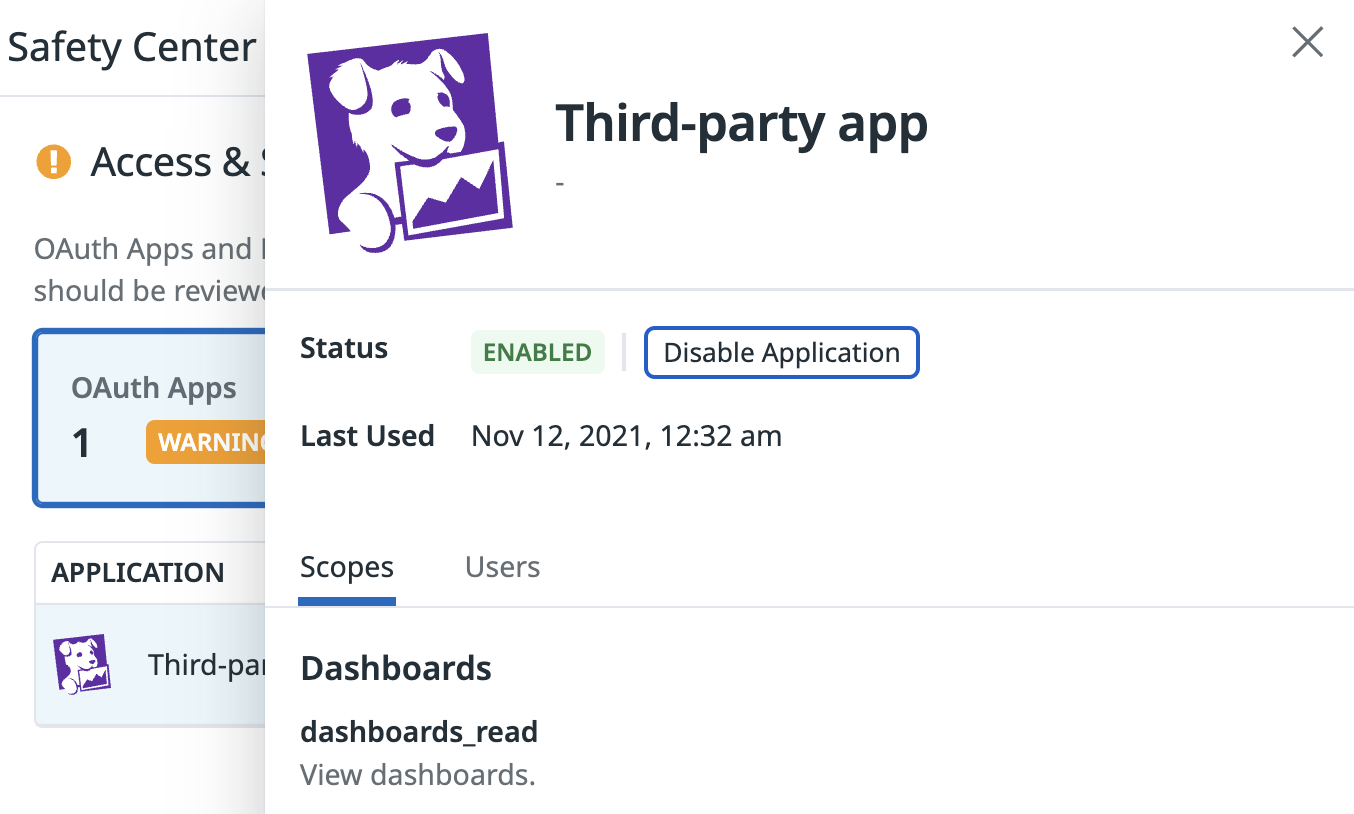
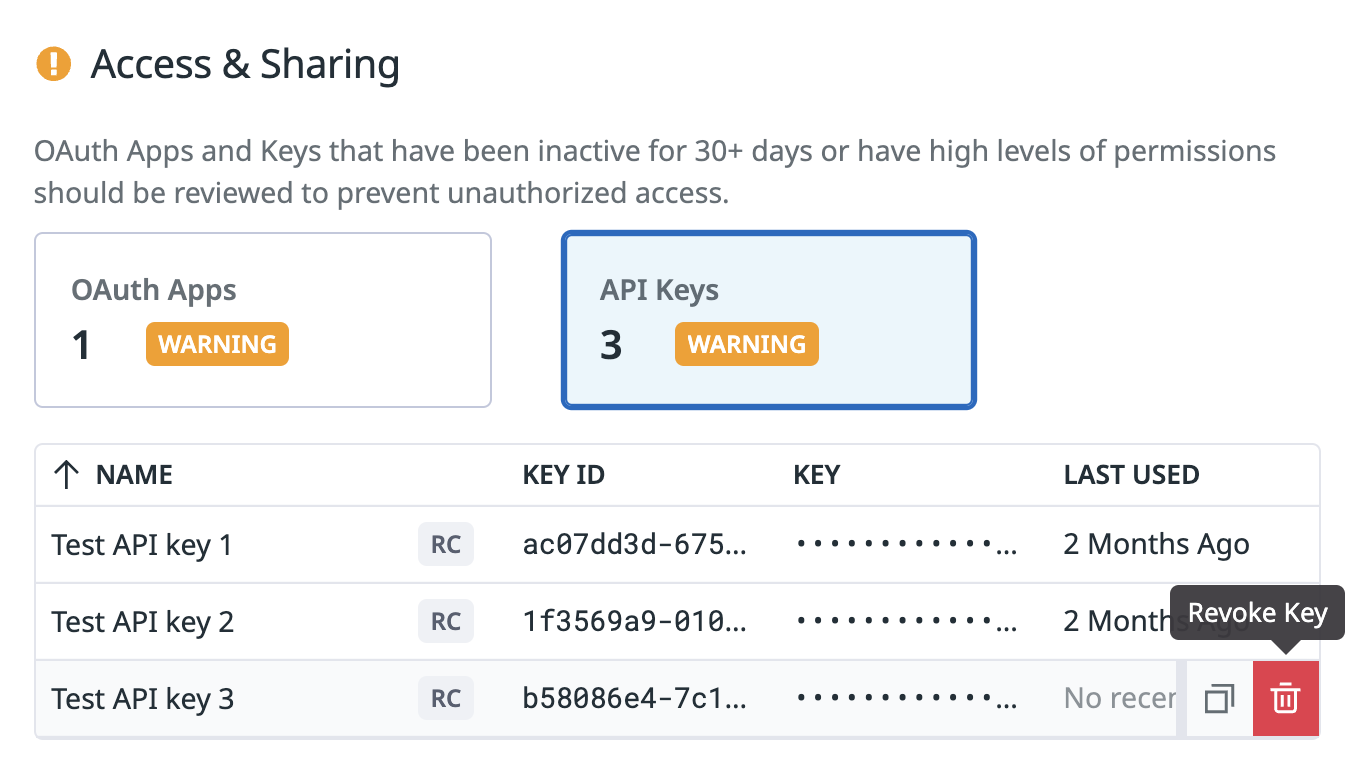
アクセスと共有
Safety Center の Access & Sharing セクションには、 Datadog 組織への外部アクセスを許可するエンティティが一覧表示されます。ここでは以下の項目がハイライトされます。
- 60 日以上非アクティブ、または書き込みアクセスがあり 30 日以上非アクティブな OAuth アプリケーション。
- 30 日以上未使用の API キー。
OAuth アプリ
非アクティブな OAuth アプリケーションは、侵害された場合、組織に潜在的なセキュリティリスクをもたらす可能性があります。定期的に見直し、使用されていないアプリケーションは無効化するべきです。
API キー
未使用の API キーは、インターネット上に公開された場合、組織への不正アクセスを容易にする可能性があります。未使用のキーは見直し、組織のインフラストラクチャーが依存していないものは取り消す必要があります。
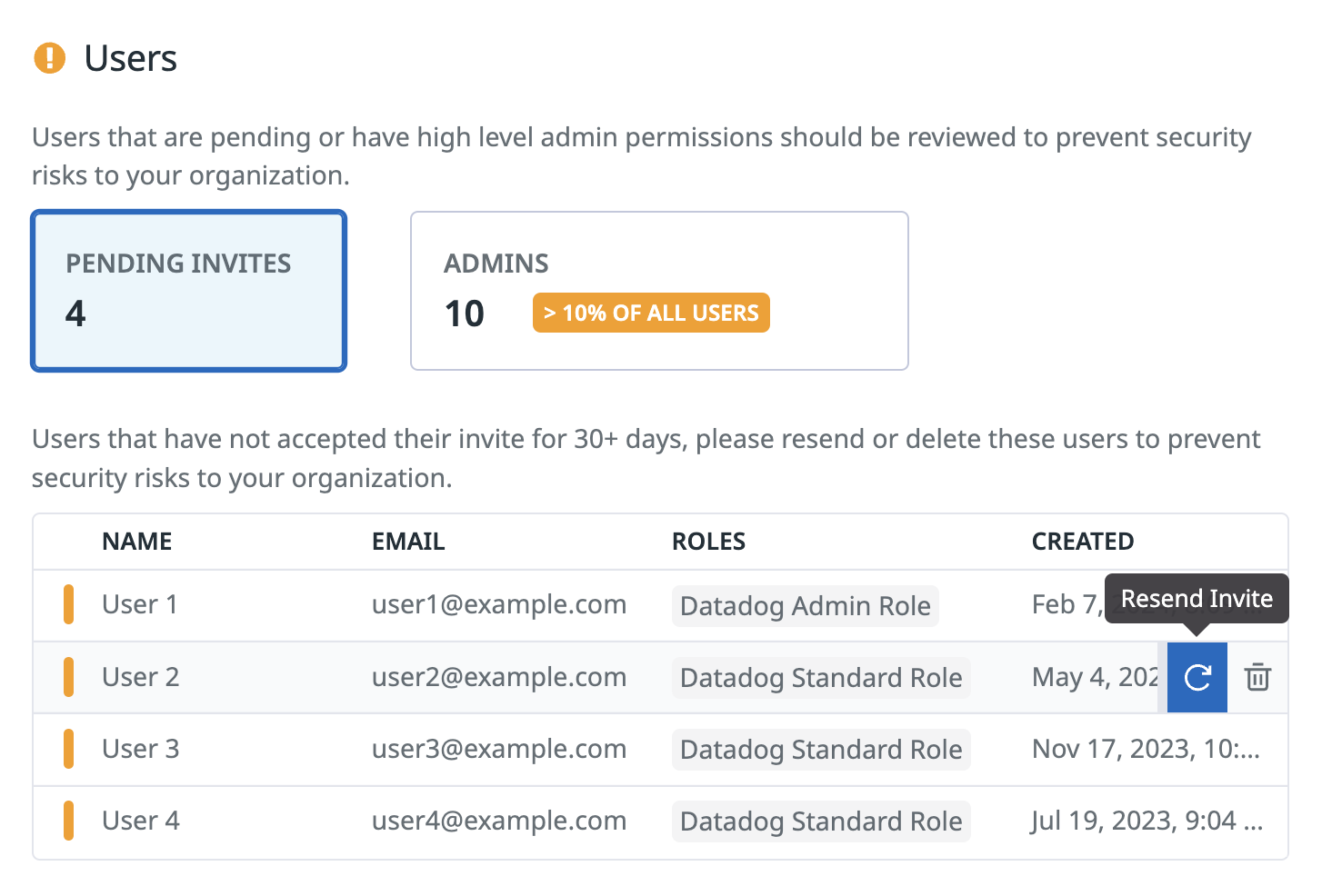
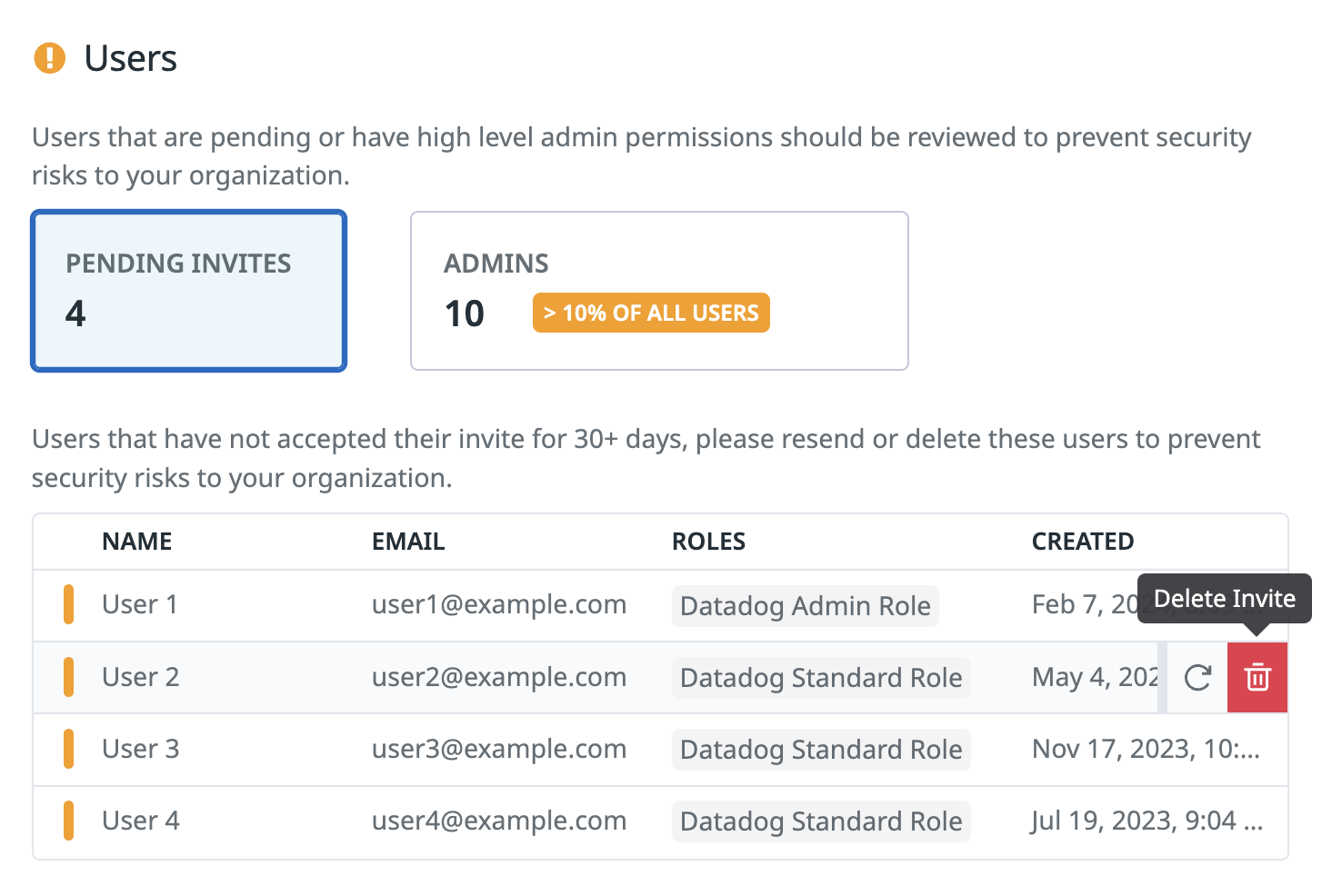
ユーザー
組織を安全に保つためには、ユーザー管理のベストプラクティスに従うことが重要です。Safety Center の Users ページでは、ユーザー関連のセキュリティ推奨事項が表示されます。
保留中の招待
非アクティブなユーザーアカウントや古い保留中のユーザー招待があると、アカウント乗っ取り攻撃のリスクが高まります。特に非アクティブなユーザーアカウントが高い権限を持っている場合は危険です。非アクティブなユーザー数を最小限に抑えるために、古い保留中の招待を再送するか、 Datadog プラットフォームへのアクセスが不要な場合は削除を検討してください。
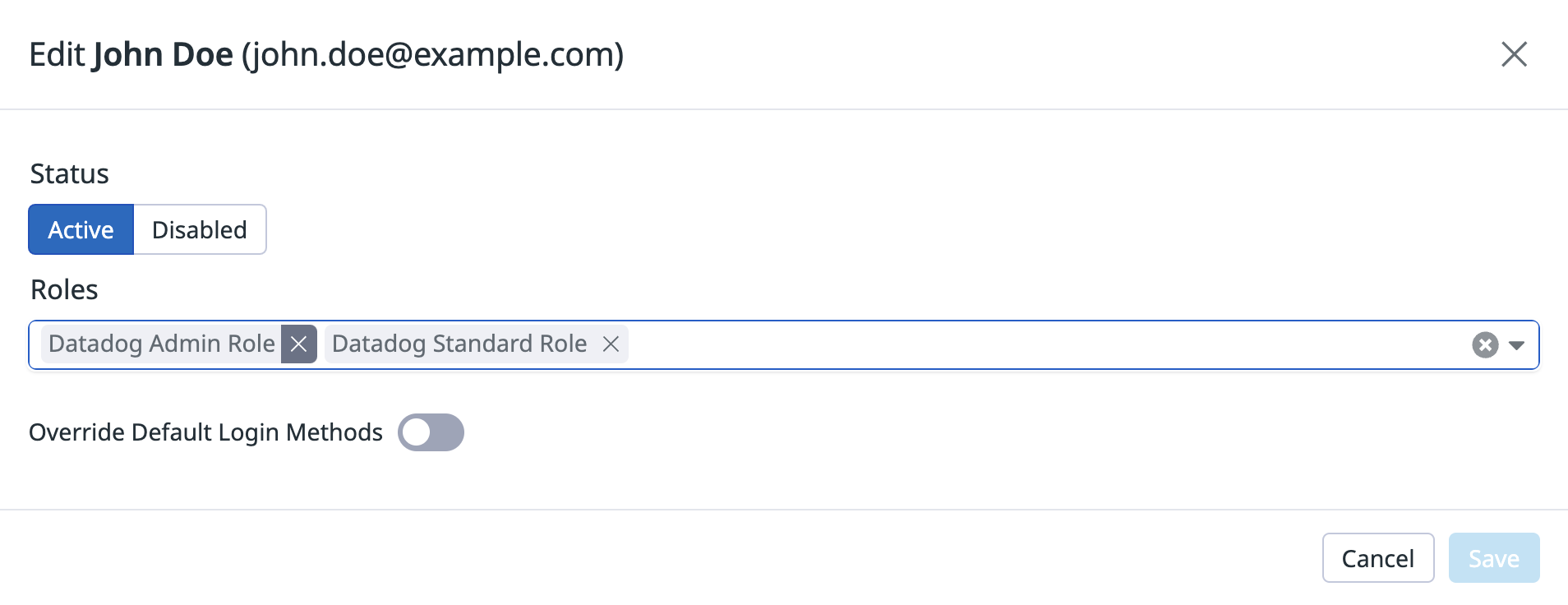
管理者
慎重な考慮なしにユーザーに管理者アクセス権を与えると、高い権限を持つユーザーアカウントが侵害された場合、潜在的なセキュリティリスクが増大します。管理者アクセス権を持つユーザーの数を減らすために、定期的に管理者ユーザーを見直し、必要のないユーザーからは管理者権限を取り消してください。
参考資料
お役に立つドキュメント、リンクや記事: