- Agents
- Essentials
- Getting Started
- Agent
- API
- APM Tracing
- Containers
- Dashboards
- Database Monitoring
- Datadog
- Datadog Site
- DevSecOps
- Incident Management
- Integrations
- Internal Developer Portal
- Logs
- Monitors
- Notebooks
- OpenTelemetry
- Profiler
- Search
- Session Replay
- Security
- Serverless for AWS Lambda
- Software Delivery
- Synthetic Monitoring and Testing
- Tags
- Workflow Automation
- Learning Center
- Support
- Glossary
- Standard Attributes
- Guides
- Agent
- Integrations
- Extend Datadog
- Authorization
- DogStatsD
- Custom Checks
- Integrations
- Build an Integration with Datadog
- Create an Agent-based Integration
- Create an API-based Integration
- Create a Log Pipeline
- Integration Assets Reference
- Build a Marketplace Offering
- Create an Integration Dashboard
- Create a Monitor Template
- Create a Cloud SIEM Detection Rule
- Install Agent Integration Developer Tool
- Service Checks
- Community
- Guides
- OpenTelemetry
- Administrator's Guide
- API
- Partners
- Datadog Mobile App
- DDSQL Reference
- CoScreen
- CoTerm
- Remote Configuration
- Cloudcraft (Standalone)
- In The App
- Dashboards
- Notebooks
- DDSQL Editor
- Reference Tables
- Sheets
- Monitors and Alerting
- Service Level Objectives
- Metrics
- Watchdog
- Bits AI
- Internal Developer Portal
- Error Tracking
- Change Tracking
- Event Management
- Incident Response
- Actions & Remediations
- Infrastructure
- Cloudcraft
- Resource Catalog
- Universal Service Monitoring
- End User Device Monitoring
- Hosts
- Containers
- Processes
- Serverless
- Network Monitoring
- Storage Management
- Cloud Cost
- Application Performance
- APM
- Continuous Profiler
- Database Monitoring
- Agent Integration Overhead
- Setup Architectures
- Setting Up Postgres
- Setting Up MySQL
- Setting Up SQL Server
- Setting Up Oracle
- Setting Up Amazon DocumentDB
- Setting Up MongoDB
- Setting Up ClickHouse
- Connecting DBM and Traces
- Data Collected
- Exploring Database Hosts
- Exploring Query Metrics
- Exploring Query Samples
- Exploring Database Schemas
- Exploring Recommendations
- Troubleshooting
- Guides
- Data Streams Monitoring
- Data Observability
- Digital Experience
- Real User Monitoring
- Synthetic Testing and Monitoring
- Continuous Testing
- Experiments
- Product Analytics
- Session Replay
- Software Delivery
- CI Visibility
- CD Visibility
- Deployment Gates
- Test Optimization
- Code Coverage
- PR Gates
- DORA Metrics
- Feature Flags
- Developer Integrations
- Security
- Security Overview
- Cloud SIEM
- Code Security
- Cloud Security
- App and API Protection
- AI Guard
- Workload Protection
- Sensitive Data Scanner
- AI Observability
- Log Management
- Observability Pipelines
- Configuration
- Sources
- Processors
- Destinations
- Packs
- Akamai CDN
- Amazon CloudFront
- Amazon VPC Flow Logs
- AWS Application Load Balancer Logs
- AWS CloudTrail
- AWS Elastic Load Balancer Logs
- AWS Network Load Balancer Logs
- Cisco ASA
- Cloudflare
- F5
- Fastly
- Fortinet Firewall
- HAProxy Ingress
- Istio Proxy
- Juniper SRX Firewall Traffic Logs
- Netskope
- NGINX
- Okta
- Palo Alto Firewall
- Windows XML
- ZScaler ZIA DNS
- Zscaler ZIA Firewall
- Zscaler ZIA Tunnel
- Zscaler ZIA Web Logs
- Search Syntax
- Scaling and Performance
- Monitoring and Troubleshooting
- Guides and Resources
- Log Management
- CloudPrem
- Administration
Keycloak
Supported OS
Integration version1.2.0
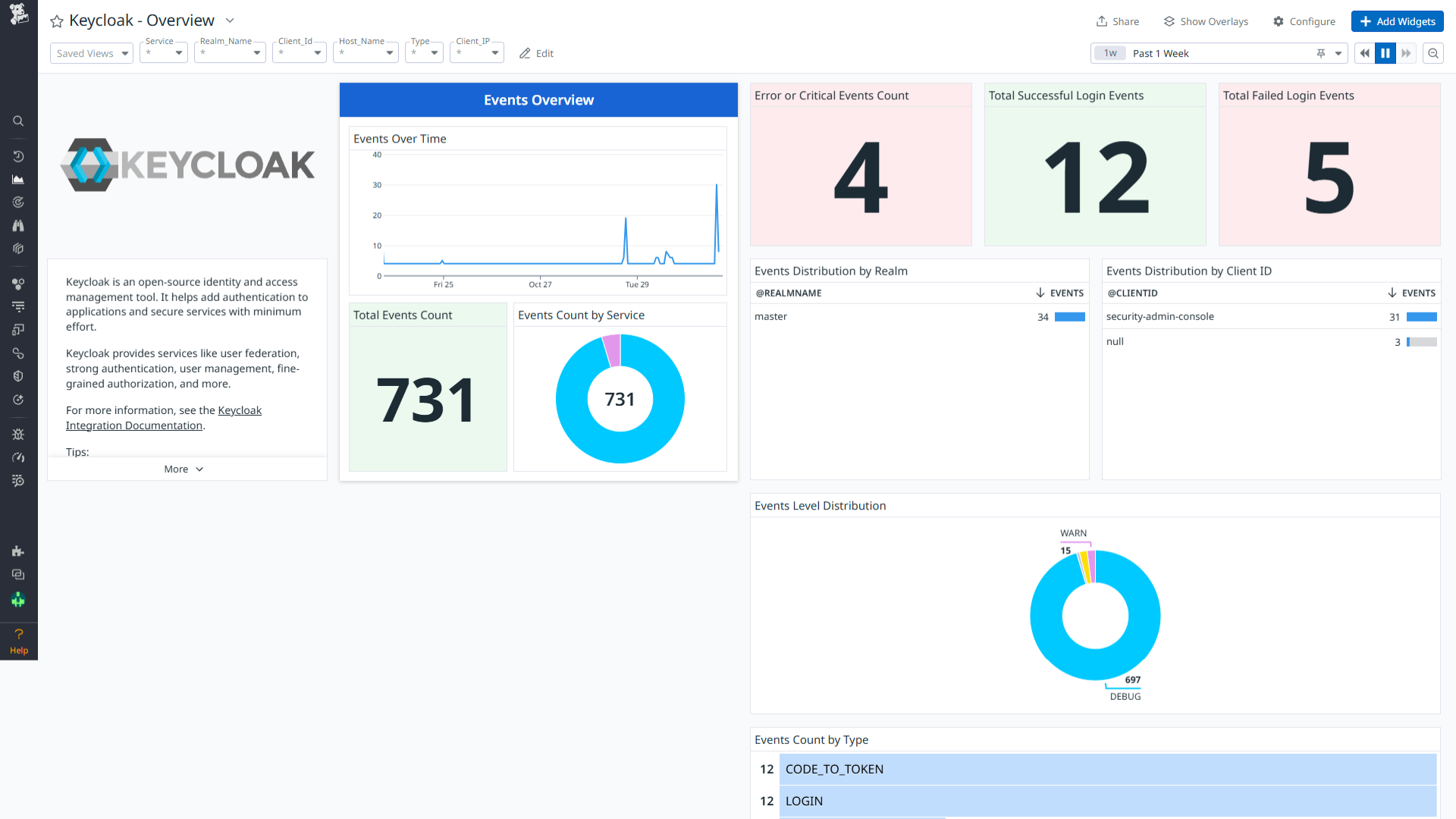
Keycloak - Overview
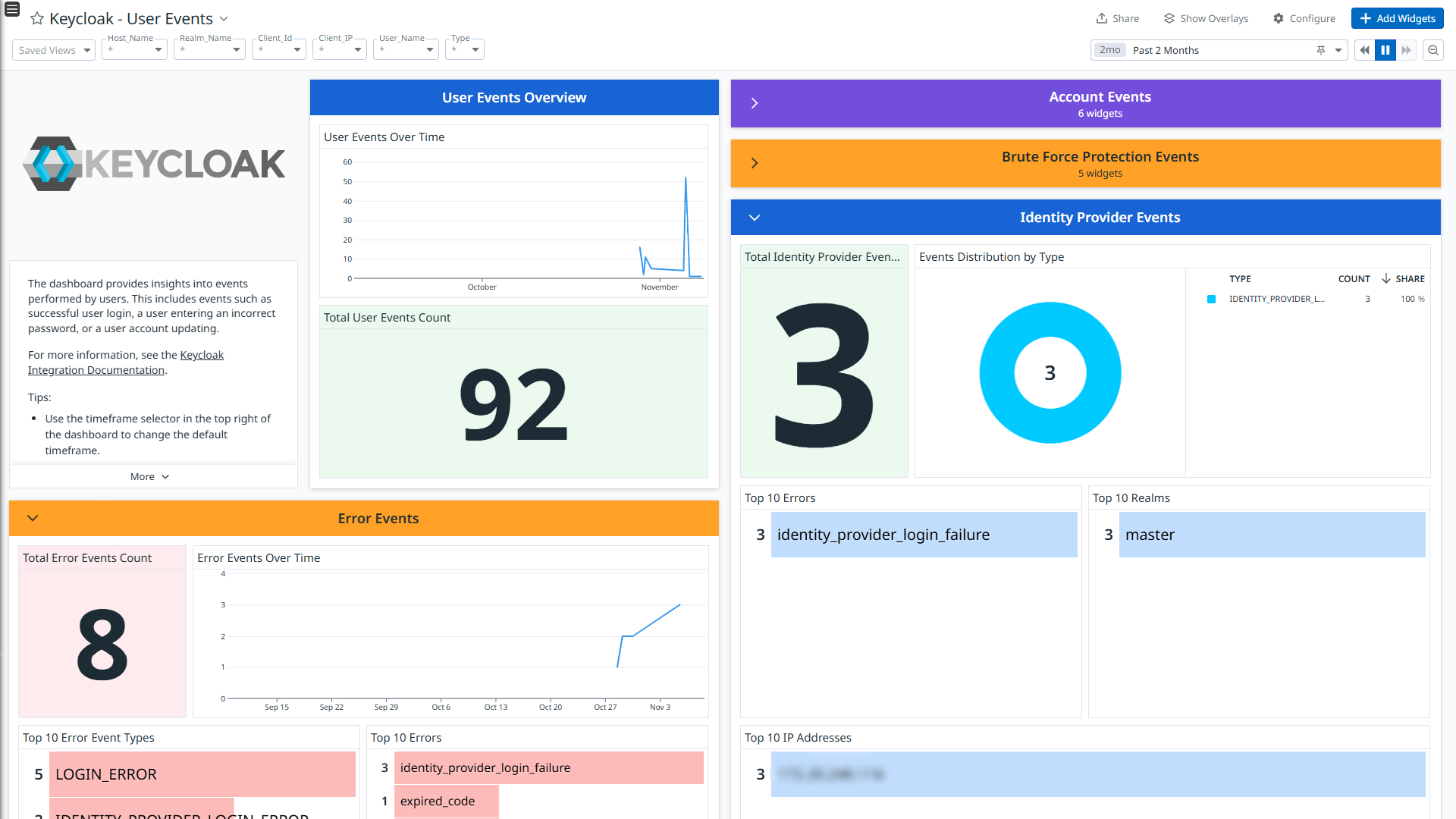
Keycloak - User Events
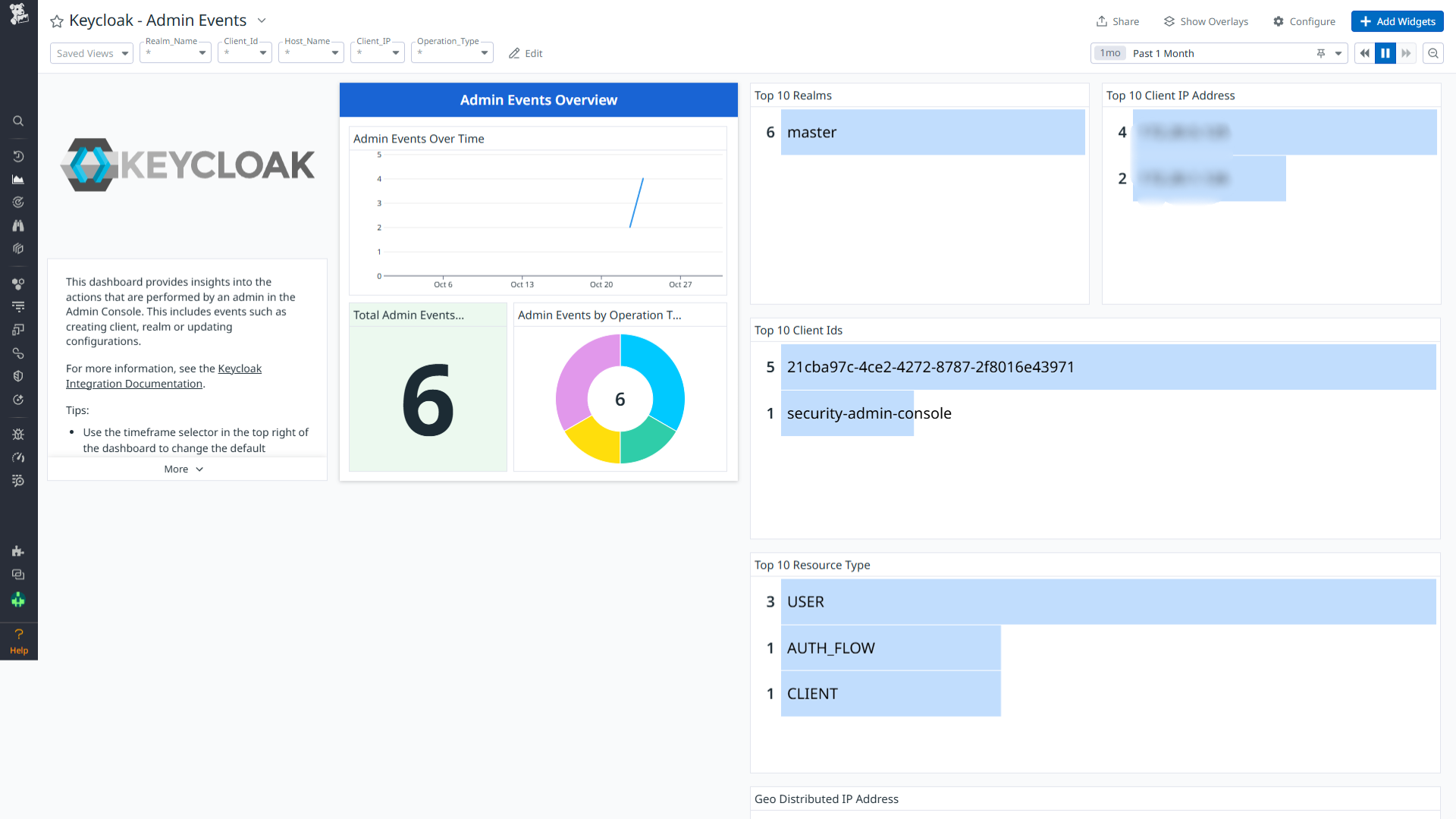
Keycloak - Admin Events
Overview
Keycloak is an open-source identity and access management tool. It helps add authentication to applications and secure services with minimum effort. Keycloak provides user federation, strong authentication, user management, fine-grained authorization, and more.
This integration parses the following types of logs:
- user-event : Events generated from activity of users like authentication, and profile updates.
- admin-event : Events generated from the activity of the admin.
Visualize detailed insights into these logs through the out-of-the-box dashboards. Additionally, out-of-the-box detection rules are available to help you monitor and respond to potential security threats effectively.
Minimum Agent version: 7.64.0
Setup
Installation
To install the Keycloak integration, run the following Agent installation command and the steps below. For more information, see the Integration Management documentation.
Note: This step is not necessary for Agent version >= 7.63.0.
Linux command
sudo -u dd-agent -- datadog-agent integration install datadog-keycloak==1.0.0
Configuration
Log collection
Collecting logs is disabled by default in the Datadog Agent. Enable it in the
datadog.yaml:logs_enabled: trueAdd this configuration block to your
keycloak.d/conf.yamlfile to start collecting your logs.See the sample keycloak.d/conf.yaml for available configuration options. The appropriate protocol (either TCP or UDP) should be chosen based on the Keycloak syslog forwarding configuration. By default, Keycloak uses TCP.
- TCP: If TCP protocol is used for syslog forwarding, set the type to
tcp. - UDP: If UDP protocol is used for syslog forwarding, modify the type to
udp.
logs: - type: <tcp/udp> port: <PORT> source: keycloak service: keycloakNote:
PORT: Port should be similar to the port provided in Configure syslog message forwarding from keycloak section.- It is recommended not to change the service and source values, as these parameters are integral to the pipeline’s operation.
- TCP: If TCP protocol is used for syslog forwarding, set the type to
Configure syslog message forwarding from keycloak
- Connect to the remote machine where Keycloak is installed.
- Navigate to the directory where Keycloak is installed (typically located at
/opt/keycloak, depending on the configuration). - Add the following options in the start command to configure Keycloak to forward logs on the Datadog Agent server and execute the same options on the Keycloak server terminal.
--log="syslog"
--log-level=org.keycloak.events:debug
--log-syslog-endpoint=<IP Address>:<Port>
--log-syslog-output=json
Optional: To use UDP instead of TCP for syslog forwarding, include the following option in the Keycloak start command:
--log-syslog-protocol=udp
- After adding the above configuration option, the start command would look like the following:
bin/kc.[sh|bat] start --log="syslog" --log-syslog-endpoint=<IP Address>:<Port> --log-level=org.keycloak.events:debug --log-syslog-output=json
IP ADDRESS: IP address where your Datadog Agent is running.
PORT: Port number to send syslog messages.
Reference: Keycloak Syslog Configuration
Validation
Run the Agent’s status subcommand and look for keycloak under the Checks section.
Data Collected
Log
| Format | Event Types |
|---|---|
| JSON | user-event, admin-event |
Metrics
The Keycloak integration does not include any metrics.
Events
The Keycloak integration does not include any events.
Service Checks
The Keycloak integration does not include any service checks.
Troubleshooting
Permission denied while port binding:
If you see a Permission denied error while port binding in the Agent logs:
Binding to a port number under 1024 requires elevated permissions. Grant access to the port using the
setcapcommand:sudo setcap CAP_NET_BIND_SERVICE=+ep /opt/datadog-agent/bin/agent/agentVerify the setup is correct by running the
getcapcommand:sudo getcap /opt/datadog-agent/bin/agent/agentWith the expected output:
/opt/datadog-agent/bin/agent/agent = cap_net_bind_service+epNote: Re-run this
setcapcommand every time you upgrade the Agent.
Data is not being collected:
Ensure traffic is bypassed from the configured port if the firewall is enabled.
Port already in use:
If you see the Port <PORT_NUMBER> Already in Use error, see the following instructions. The following example is for port 514:
- On systems using Syslog, if the Agent listens for events on port 514, the following error can appear in the Agent logs:
Can't start UDP forwarder on port 514: listen udp :514: bind: address already in use. This error occurs because by default, Syslog listens on port 514. To resolve this error, take one of the following steps:- Disable Syslog.
- Configure the Agent to listen on a different, available port.
For further assistance, contact Datadog support.
