- Essentials
- Getting Started
- Agent
- API
- APM Tracing
- Containers
- Dashboards
- Database Monitoring
- Datadog
- Datadog Site
- DevSecOps
- Incident Management
- Integrations
- Internal Developer Portal
- Logs
- Monitors
- Notebooks
- OpenTelemetry
- Profiler
- Search
- Session Replay
- Security
- Serverless for AWS Lambda
- Software Delivery
- Synthetic Monitoring and Testing
- Tags
- Workflow Automation
- Learning Center
- Support
- Glossary
- Standard Attributes
- Guides
- Agent
- Integrations
- Extend Datadog
- Authorization
- DogStatsD
- Custom Checks
- Integrations
- Build an Integration with Datadog
- Create an Agent-based Integration
- Create an API-based Integration
- Create a Log Pipeline
- Integration Assets Reference
- Build a Marketplace Offering
- Create an Integration Dashboard
- Create a Monitor Template
- Create a Cloud SIEM Detection Rule
- Install Agent Integration Developer Tool
- Service Checks
- Community
- Guides
- OpenTelemetry
- Administrator's Guide
- API
- Partners
- Datadog Mobile App
- DDSQL Reference
- CoScreen
- CoTerm
- Remote Configuration
- Cloudcraft (Standalone)
- In The App
- Dashboards
- Notebooks
- DDSQL Editor
- Reference Tables
- Sheets
- Monitors and Alerting
- Service Level Objectives
- Metrics
- Watchdog
- Bits AI
- Internal Developer Portal
- Error Tracking
- Change Tracking
- Event Management
- Incident Response
- Actions & Remediations
- Infrastructure
- Cloudcraft
- Resource Catalog
- Universal Service Monitoring
- End User Device Monitoring
- Hosts
- Containers
- Processes
- Serverless
- Network Monitoring
- Storage Management
- Cloud Cost
- Application Performance
- APM
- Continuous Profiler
- Database Monitoring
- Agent Integration Overhead
- Setup Architectures
- Setting Up Postgres
- Setting Up MySQL
- Setting Up SQL Server
- Setting Up Oracle
- Setting Up Amazon DocumentDB
- Setting Up MongoDB
- Setting Up ClickHouse
- Connecting DBM and Traces
- Data Collected
- Exploring Database Hosts
- Exploring Query Metrics
- Exploring Query Samples
- Exploring Database Schemas
- Exploring Recommendations
- Troubleshooting
- Guides
- Data Streams Monitoring
- Data Observability
- Digital Experience
- Real User Monitoring
- Synthetic Testing and Monitoring
- Continuous Testing
- Product Analytics
- Session Replay
- Software Delivery
- CI Visibility
- CD Visibility
- Deployment Gates
- Test Optimization
- Code Coverage
- PR Gates
- DORA Metrics
- Feature Flags
- Developer Integrations
- Security
- Security Overview
- Cloud SIEM
- Code Security
- Cloud Security
- App and API Protection
- AI Guard
- Workload Protection
- Sensitive Data Scanner
- AI Observability
- Log Management
- Observability Pipelines
- Configuration
- Sources
- Processors
- Destinations
- Packs
- Akamai CDN
- Amazon CloudFront
- Amazon VPC Flow Logs
- AWS Application Load Balancer Logs
- AWS CloudTrail
- AWS Elastic Load Balancer Logs
- AWS Network Load Balancer Logs
- Cisco ASA
- Cloudflare
- F5
- Fastly
- Fortinet Firewall
- HAProxy Ingress
- Istio Proxy
- Juniper SRX Firewall Traffic Logs
- Netskope
- NGINX
- Okta
- Palo Alto Firewall
- Windows XML
- ZScaler ZIA DNS
- Zscaler ZIA Firewall
- Zscaler ZIA Tunnel
- Zscaler ZIA Web Logs
- Search Syntax
- Scaling and Performance
- Monitoring and Troubleshooting
- Guides and Resources
- Log Management
- CloudPrem
- Administration
- Account Management
- Data Security
- Help
- feature_flags_client
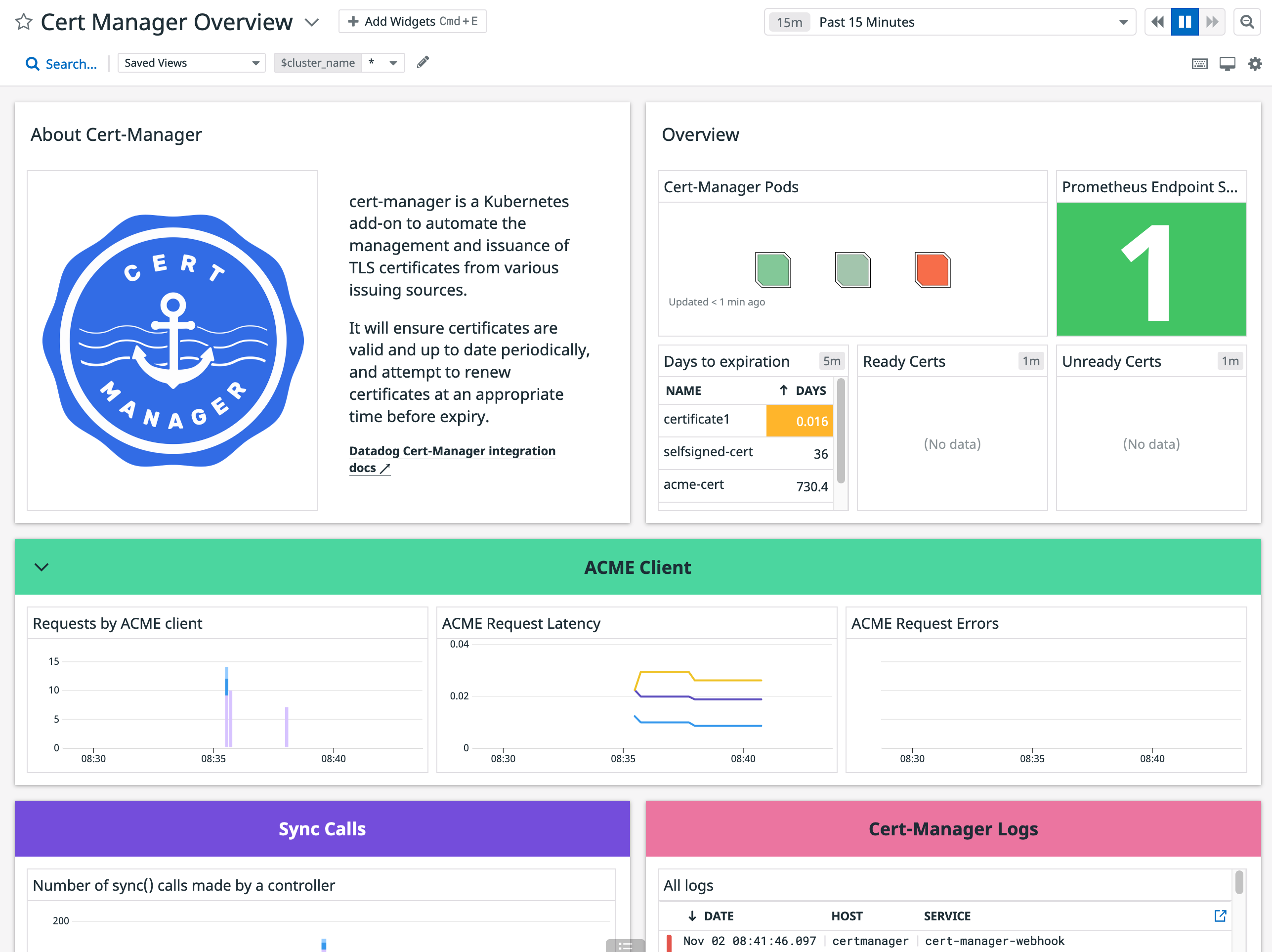
cert-manager
Supported OS
Integration version6.3.0
Overview
This check collects metrics from cert-manager.
Minimum Agent version: 7.22.0
Setup
Follow the instructions below to install and configure this check for an Agent running on a host. For containerized environments, see the Autodiscovery Integration Templates for guidance on applying these instructions.
Installation
The cert_manager check is included in the Datadog Agent package. No additional installation is needed on your server.
Configuration
Edit the
cert_manager.d/conf.yamlfile in theconf.d/folder at the root of your Agent’s configuration directory to start collecting your cert_manager performance data. See the sample cert_manager.d/conf.yaml for all available configuration options.
Validation
Run the Agent’s status subcommand and look for cert_manager under the Checks section.
Data Collected
Metrics
| cert_manager.certificate.expiration_timestamp (gauge) | The date after which the certificate expires. Expressed as a Unix Epoch Time Shown as second |
| cert_manager.certificate.ready_status (gauge) | The ready status of the certificate |
| cert_manager.certificate.renewal_timestamp (gauge) | The date at which the certificate will be renewed. Expressed as a Unix Epoch Time Shown as second |
| cert_manager.clock_time (gauge) | The clock time given in seconds (from 1970/01/01 UTC) Shown as second |
| cert_manager.controller.sync_call.count (count) | The number of sync() calls made by a controller |
| cert_manager.http_acme_client.request.count (count) | The number of requests made by the ACME client |
| cert_manager.http_acme_client.request.duration.count (count) | The count of the HTTP request latencies in seconds for the ACME client |
| cert_manager.http_acme_client.request.duration.quantile (gauge) | The quantiles of the HTTP request latencies in seconds for the ACME client |
| cert_manager.http_acme_client.request.duration.sum (count) | The sum of the HTTP request latencies in seconds for the ACME client |
Events
The cert_manager integration does not include any events.
Service Checks
cert_manager.openmetrics.health
Returns CRITICAL if the agent fails to connect to the OpenMetrics endpoint, otherwise OK.
Statuses: ok, critical
Troubleshooting
Duplicate name tags
Each certificate name is exposed within the name label in the Prometheus payload and is converted to a tag by the Datadog Agent. If your hosts also use the name tag (for instance, automatically collected by the AWS integration), metrics coming from this integration will present both values. To avoid duplicate name tags, you can use the rename_labelsconfiguration parameter to map the Prometheus label name to the Datadog tag cert_name. This ensures you have a single value within the tag cert_name to identify your certificates :
init_config:
instances:
- openmetrics_endpoint: <OPENMETRICS_ENDPOINT>
rename_labels:
name: cert_name
Need further help? Contact Datadog support.
