- Esenciales
- Empezando
- Agent
- API
- Rastreo de APM
- Contenedores
- Dashboards
- Monitorización de bases de datos
- Datadog
- Sitio web de Datadog
- DevSecOps
- Gestión de incidencias
- Integraciones
- Internal Developer Portal
- Logs
- Monitores
- OpenTelemetry
- Generador de perfiles
- Session Replay
- Security
- Serverless para Lambda AWS
- Software Delivery
- Monitorización Synthetic
- Etiquetas (tags)
- Workflow Automation
- Centro de aprendizaje
- Compatibilidad
- Glosario
- Atributos estándar
- Guías
- Agent
- Arquitectura
- IoT
- Plataformas compatibles
- Recopilación de logs
- Configuración
- Automatización de flotas
- Solucionar problemas
- Detección de nombres de host en contenedores
- Modo de depuración
- Flare del Agent
- Estado del check del Agent
- Problemas de NTP
- Problemas de permisos
- Problemas de integraciones
- Problemas del sitio
- Problemas de Autodiscovery
- Problemas de contenedores de Windows
- Configuración del tiempo de ejecución del Agent
- Consumo elevado de memoria o CPU
- Guías
- Seguridad de datos
- Integraciones
- Desarrolladores
- Autorización
- DogStatsD
- Checks personalizados
- Integraciones
- Build an Integration with Datadog
- Crear una integración basada en el Agent
- Crear una integración API
- Crear un pipeline de logs
- Referencia de activos de integración
- Crear una oferta de mercado
- Crear un dashboard de integración
- Create a Monitor Template
- Crear una regla de detección Cloud SIEM
- Instalar la herramienta de desarrollo de integraciones del Agente
- Checks de servicio
- Complementos de IDE
- Comunidad
- Guías
- OpenTelemetry
- Administrator's Guide
- API
- Partners
- Aplicación móvil de Datadog
- DDSQL Reference
- CoScreen
- CoTerm
- Remote Configuration
- Cloudcraft
- En la aplicación
- Dashboards
- Notebooks
- Editor DDSQL
- Reference Tables
- Hojas
- Monitores y alertas
- Watchdog
- Métricas
- Bits AI
- Internal Developer Portal
- Error Tracking
- Explorador
- Estados de problemas
- Detección de regresión
- Suspected Causes
- Error Grouping
- Bits AI Dev Agent
- Monitores
- Issue Correlation
- Identificar confirmaciones sospechosas
- Auto Assign
- Issue Team Ownership
- Rastrear errores del navegador y móviles
- Rastrear errores de backend
- Manage Data Collection
- Solucionar problemas
- Guides
- Change Tracking
- Gestión de servicios
- Objetivos de nivel de servicio (SLOs)
- Gestión de incidentes
- De guardia
- Status Pages
- Gestión de eventos
- Gestión de casos
- Actions & Remediations
- Infraestructura
- Cloudcraft
- Catálogo de recursos
- Universal Service Monitoring
- Hosts
- Contenedores
- Processes
- Serverless
- Monitorización de red
- Cloud Cost
- Rendimiento de las aplicaciones
- APM
- Términos y conceptos de APM
- Instrumentación de aplicación
- Recopilación de métricas de APM
- Configuración de pipelines de trazas
- Correlacionar trazas (traces) y otros datos de telemetría
- Trace Explorer
- Recommendations
- Code Origin for Spans
- Observabilidad del servicio
- Endpoint Observability
- Instrumentación dinámica
- Live Debugger
- Error Tracking
- Seguridad de los datos
- Guías
- Solucionar problemas
- Límites de tasa del Agent
- Métricas de APM del Agent
- Uso de recursos del Agent
- Logs correlacionados
- Stacks tecnológicos de llamada en profundidad PHP 5
- Herramienta de diagnóstico de .NET
- Cuantificación de APM
- Go Compile-Time Instrumentation
- Logs de inicio del rastreador
- Logs de depuración del rastreador
- Errores de conexión
- Continuous Profiler
- Database Monitoring
- Gastos generales de integración del Agent
- Arquitecturas de configuración
- Configuración de Postgres
- Configuración de MySQL
- Configuración de SQL Server
- Configuración de Oracle
- Configuración de MongoDB
- Setting Up Amazon DocumentDB
- Conexión de DBM y trazas
- Datos recopilados
- Explorar hosts de bases de datos
- Explorar métricas de consultas
- Explorar ejemplos de consulta
- Exploring Database Schemas
- Exploring Recommendations
- Solucionar problemas
- Guías
- Data Streams Monitoring
- Data Jobs Monitoring
- Data Observability
- Experiencia digital
- Real User Monitoring
- Pruebas y monitorización de Synthetics
- Continuous Testing
- Análisis de productos
- Entrega de software
- CI Visibility
- CD Visibility
- Deployment Gates
- Test Visibility
- Configuración
- Network Settings
- Tests en contenedores
- Repositories
- Explorador
- Monitores
- Test Health
- Flaky Test Management
- Working with Flaky Tests
- Test Impact Analysis
- Flujos de trabajo de desarrolladores
- Cobertura de código
- Instrumentar tests de navegador con RUM
- Instrumentar tests de Swift con RUM
- Correlacionar logs y tests
- Guías
- Solucionar problemas
- Code Coverage
- Quality Gates
- Métricas de DORA
- Feature Flags
- Seguridad
- Información general de seguridad
- Cloud SIEM
- Code Security
- Cloud Security Management
- Application Security Management
- Workload Protection
- Sensitive Data Scanner
- Observabilidad de la IA
- Log Management
- Observability Pipelines
- Gestión de logs
- CloudPrem
- Administración
- Gestión de cuentas
- Seguridad de los datos
- Ayuda
Snowflake
Este producto no es compatible con el sitio Datadog seleccionado. ().
Esta página aún no está disponible en español. Estamos trabajando en su traducción.
Si tienes alguna pregunta o comentario sobre nuestro actual proyecto de traducción, no dudes en ponerte en contacto con nosotros.
Si tienes alguna pregunta o comentario sobre nuestro actual proyecto de traducción, no dudes en ponerte en contacto con nosotros.
Overview
The Snowflake integration connects Datadog to your Snowflake account to sync metadata, query history, and table-level metrics. Use it to monitor data freshness, detect anomalies, and trace lineage across your warehouse and downstream tools.
Prerequisites
Before you begin, make sure you have:
- Access to the
ACCOUNTADMINrole in Snowflake. - An RSA key pair. For more information, see the Snowflake key-pair authentication docs.
- If your Snowflake account restricts network access by IP, Datadog webhook IPs must be included in your network policy allowlist. For the list of IPs, see the
webhookssection of IP ranges list.
Set up your account in Snowflake
To set up your account in Snowflake:
Define the following variables:
SET role_name = 'DATADOG_ROLE'; SET user_name = 'DATADOG_USER'; SET warehouse_name = 'DATADOG_WH'; SET database_name = '<YOUR_DATABASE>';Create a role, warehouse, and key-pair-authenticated user.
USE ROLE ACCOUNTADMIN; -- Create monitoring role CREATE ROLE IF NOT EXISTS IDENTIFIER($role_name); GRANT ROLE IDENTIFIER($role_name) TO ROLE SYSADMIN; -- Create an X-SMALL warehouse (auto-suspend after 30s) CREATE WAREHOUSE IF NOT EXISTS IDENTIFIER($warehouse_name) WAREHOUSE_SIZE = XSMALL WAREHOUSE_TYPE = STANDARD AUTO_SUSPEND = 30 AUTO_RESUME = TRUE INITIALLY_SUSPENDED = TRUE; -- Create Datadog user—key-pair only (no password) -- Replace <PUBLIC_KEY> with your RSA public key (PEM, no headers/newlines) CREATE USER IF NOT EXISTS IDENTIFIER($user_name) LOGIN_NAME = $user_name DEFAULT_ROLE = $role_name DEFAULT_WAREHOUSE = $warehouse_name RSA_PUBLIC_KEY = '<PUBLIC_KEY>'; GRANT ROLE IDENTIFIER($role_name) TO USER IDENTIFIER($user_name);Grant monitoring privileges to the role.
-- Warehouse usage GRANT USAGE ON WAREHOUSE IDENTIFIER($warehouse_name) TO ROLE IDENTIFIER($role_name); -- Account‐level monitoring (tasks, pipes, query history) GRANT MONITOR EXECUTION ON ACCOUNT TO ROLE IDENTIFIER($role_name); -- Imported privileges on Snowflake's ACCOUNT_USAGE GRANT IMPORTED PRIVILEGES ON DATABASE SNOWFLAKE TO ROLE IDENTIFIER($role_name); -- Imported privileges on any external data shares -- GRANT IMPORTED PRIVILEGES ON DATABASE IDENTIFIER($database_name) TO ROLE IDENTIFIER($role_name); -- Grant the following ACCOUNT_USAGE views to the new role. Do this if you wish to collect Snowflake account usage logs and metrics. GRANT DATABASE ROLE SNOWFLAKE.OBJECT_VIEWER TO ROLE IDENTIFIER($role_name); GRANT DATABASE ROLE SNOWFLAKE.USAGE_VIEWER TO ROLE IDENTIFIER($role_name); GRANT DATABASE ROLE SNOWFLAKE.GOVERNANCE_VIEWER TO ROLE IDENTIFIER($role_name); GRANT DATABASE ROLE SNOWFLAKE.SECURITY_VIEWER TO ROLE IDENTIFIER($role_name); -- Grant ORGANIZATION_USAGE_VIEWER to the new role. Do this if you wish to collect Snowflake organization usage metrics. GRANT DATABASE ROLE SNOWFLAKE.ORGANIZATION_USAGE_VIEWER TO ROLE IDENTIFIER($role_name); -- Grant ORGANIZATION_BILLING_VIEWER to the new role. Do this if you wish to collect Snowflake cost data. GRANT DATABASE ROLE SNOWFLAKE.ORGANIZATION_BILLING_VIEWER TO ROLE IDENTIFIER($role_name);To avoid missing new tables, use schema-level future grants. Snowflake gives schema-level grants precedence over database-level ones. If Datadog only has database-level grants but other roles have schema-level grants on the same schemas, new tables may not appear in Datadog. See Snowflake's documentation for details.Grant read-only access to your data.
USE DATABASE IDENTIFIER($database_name); CREATE OR REPLACE PROCEDURE grantFutureAccess(databaseName string, roleName string) returns string not null language javascript as $$ var schemaResultSet = snowflake.execute({ sqlText: 'SELECT SCHEMA_NAME FROM ' + '"' + DATABASENAME + '"' + ".INFORMATION_SCHEMA.SCHEMATA WHERE SCHEMA_NAME != 'INFORMATION_SCHEMA';"}); var numberOfSchemasGranted = 0; while (schemaResultSet.next()) { numberOfSchemasGranted += 1; var schemaAndRoleSuffix = ' in schema "' + DATABASENAME + '"."' + schemaResultSet.getColumnValue('SCHEMA_NAME') + '" to role ' + ROLENAME + ';' snowflake.execute({ sqlText: 'grant USAGE on schema "' + DATABASENAME + '"."' + schemaResultSet.getColumnValue('SCHEMA_NAME') + '" to role ' + ROLENAME + ';'}); snowflake.execute({ sqlText: 'grant SELECT on all tables' + schemaAndRoleSuffix}); snowflake.execute({ sqlText: 'grant SELECT on all views' + schemaAndRoleSuffix}); snowflake.execute({ sqlText: 'grant SELECT on all event tables' + schemaAndRoleSuffix}); snowflake.execute({ sqlText: 'grant SELECT on all external tables' + schemaAndRoleSuffix}); snowflake.execute({ sqlText: 'grant SELECT on all dynamic tables' + schemaAndRoleSuffix}); snowflake.execute({ sqlText: 'grant SELECT on future tables' + schemaAndRoleSuffix}); snowflake.execute({ sqlText: 'grant SELECT on future views' + schemaAndRoleSuffix}); snowflake.execute({ sqlText: 'grant SELECT on future event tables' + schemaAndRoleSuffix}); snowflake.execute({ sqlText: 'grant SELECT on future external tables' + schemaAndRoleSuffix}); snowflake.execute({ sqlText: 'grant SELECT on future dynamic tables' + schemaAndRoleSuffix}); } return 'Granted access to ' + numberOfSchemasGranted + ' schemas'; $$ ; GRANT USAGE ON DATABASE IDENTIFIER($database_name) TO ROLE IDENTIFIER($role_name); CALL grantFutureAccess('<DATABASE_NAME>', '<ROLE_NAME>');(Optional) If your organization uses Snowflake event tables, you can grant the Datadog role access to them.
-- Grant usage on the database, schema, and table of the event table GRANT USAGE ON DATABASE <EVENT_TABLE_DATABASE> TO ROLE IDENTIFIER($role_name); GRANT USAGE ON SCHEMA <EVENT_TABLE_DATABASE>.<EVENT_TABLE_SCHEMA> TO ROLE IDENTIFIER($role_name); GRANT SELECT ON TABLE <EVENT_TABLE_DATABASE>.<EVENT_TABLE_SCHEMA>.<EVENT_TABLE_NAME> TO ROLE IDENTIFIER($role_name); -- Snowflake-provided application roles for event logs GRANT APPLICATION ROLE SNOWFLAKE.EVENTS_VIEWER TO ROLE IDENTIFIER($role_name); GRANT APPLICATION ROLE SNOWFLAKE.EVENTS_ADMIN TO ROLE IDENTIFIER($role_name);After completing the Snowflake setup, configure the Snowflake integration in Datadog.
Configure the Snowflake integration in Datadog
To configure the Snowflake integration in Datadog:
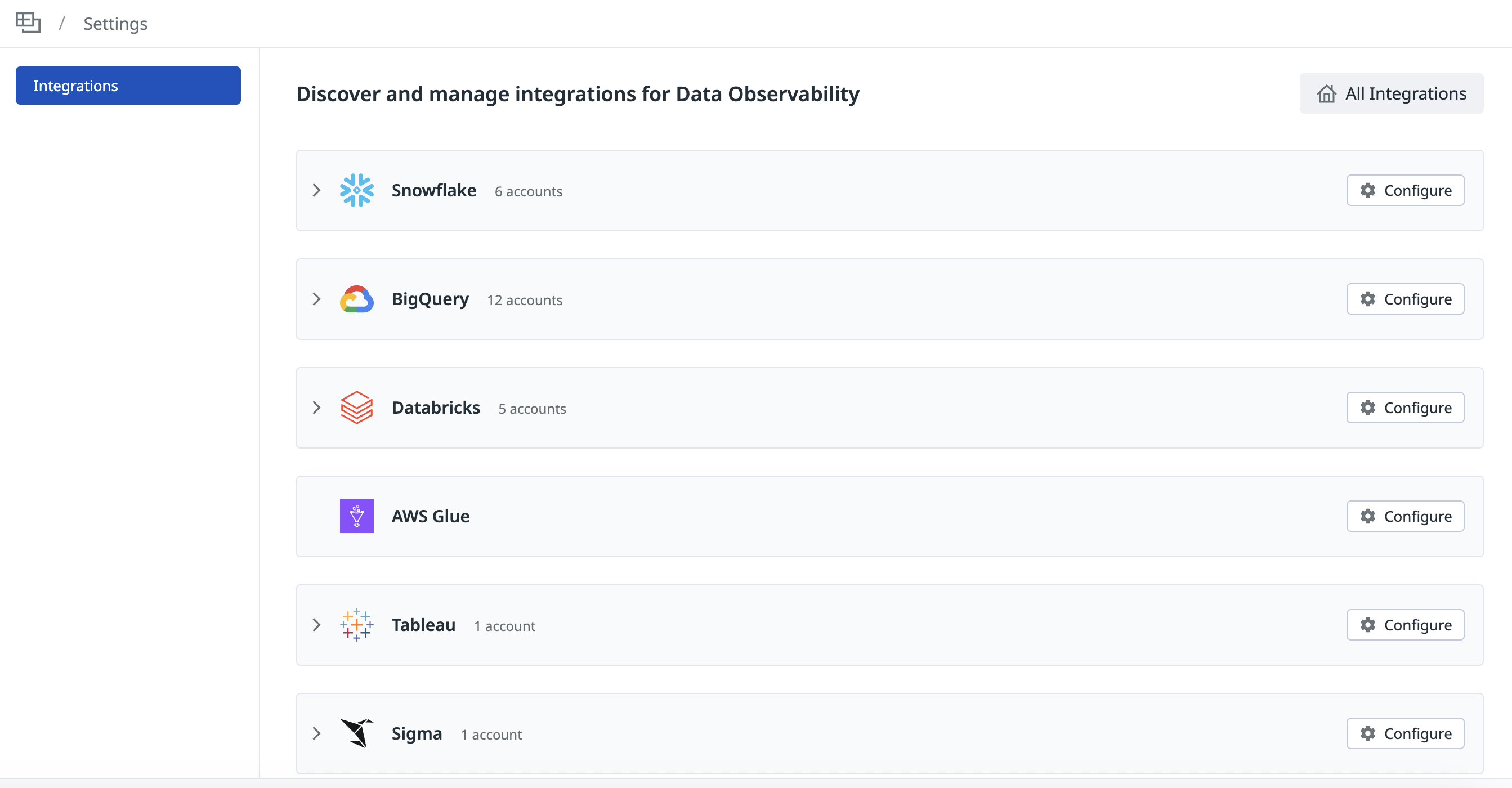
Navigate to Datadog Data Observability > Settings.
Click the Configure button for the Snowflake option.
Follow the flow to enter your account details and upload a private key.
Turn on Enable Data Observability for Snowflake tables.
Click Save & Test.
Snowflake tasks and Snowpipes
Datadog derives lineage from Snowflake tasks and Snowpipes by parsing their SQL definitions.
- For tasks, this includes task-to-task dependencies and lineage to destination tables.
- For Snowpipes, Datadog derives lineage from the source stage to the destination table.
Both features require the GRANT MONITOR EXECUTION ON ACCOUNT permission granted during setup.
Snowflake tasks traces are in preview. Contact your account representative to enable this feature.
When enabled, each task graph run appears as a trace in APM with individual tasks as spans, including execution details such as status, duration, and errors. To find them:
- In Datadog, go to APM > Trace Explorer.
- Filter the Explorer:
- For the top-level task graph span, filter by
operation_name:snowflake.task_graph - For individual task spans, filter by
operation_name:snowflake.task
- For the top-level task graph span, filter by
Next steps
After you save, Datadog begins syncing your information schema and query history in the background. Initial syncs can take up to several hours depending on the size of your Snowflake deployment.
After the initial sync completes, create a Data Observability monitor to start alerting on freshness, row count, column-level metrics, and custom SQL metrics.
Troubleshoot permissions
If Datadog is unable to see expected databases, schemas, or tables in your Snowflake account, follow these steps to verify that the Datadog role has the correct access.
The Snowflake console enables secondary roles by default, which can make it appear that a role has more access than it actually does. Step 2 below helps ensure you are testing with only the Datadog role's permissions.
Set the role and user to the same ones provisioned for Datadog:
USE ROLE DATADOG_ROLE;Disable secondary roles so that only the Datadog role’s grants are active:
USE SECONDARY ROLES NONE;Check that the correct role is set and no secondary roles are in use:
SELECT CURRENT_ROLE(), CURRENT_SECONDARY_ROLES();List the databases the Datadog role can access:
SELECT database_name FROM snowflake.information_schema.databases;Check access to specific schemas or tables:
SHOW SCHEMAS IN DATABASE "<DATABASE_NAME>"; SHOW TABLES IN SCHEMA "<DATABASE_NAME>"."<SCHEMA_NAME>";
Further reading
Más enlaces, artículos y documentación útiles: