- Agents
- Essentials
- Getting Started
- Agent
- API
- APM Tracing
- Containers
- Dashboards
- Database Monitoring
- Datadog
- Datadog Site
- DevSecOps
- Incident Management
- Integrations
- Internal Developer Portal
- Logs
- Monitors
- Notebooks
- OpenTelemetry
- Profiler
- Search
- Session Replay
- Security
- Serverless for AWS Lambda
- Software Delivery
- Synthetic Monitoring and Testing
- Tags
- Workflow Automation
- Learning Center
- Support
- Glossary
- Standard Attributes
- Guides
- Agent
- Integrations
- Extend Datadog
- Authorization
- DogStatsD
- Custom Checks
- Integrations
- Build an Integration with Datadog
- Create an Agent-based Integration
- Create an API-based Integration
- Create a Log Pipeline
- Integration Assets Reference
- Build a Marketplace Offering
- Create an Integration Dashboard
- Create a Monitor Template
- Create a Cloud SIEM Detection Rule
- Install Agent Integration Developer Tool
- Service Checks
- Community
- Guides
- OpenTelemetry
- Administrator's Guide
- API
- Partners
- Datadog Mobile App
- DDSQL Reference
- CoScreen
- CoTerm
- Remote Configuration
- Cloudcraft (Standalone)
- In The App
- Dashboards
- Notebooks
- DDSQL Editor
- Reference Tables
- Sheets
- Monitors and Alerting
- Service Level Objectives
- Metrics
- Watchdog
- Bits AI
- Internal Developer Portal
- Error Tracking
- Change Tracking
- Event Management
- Incident Response
- Actions & Remediations
- Infrastructure
- Cloudcraft
- Resource Catalog
- Universal Service Monitoring
- End User Device Monitoring
- Hosts
- Containers
- Processes
- Serverless
- Network Monitoring
- Storage Management
- Cloud Cost
- Application Performance
- APM
- Continuous Profiler
- Database Monitoring
- Agent Integration Overhead
- Setup Architectures
- Setting Up Postgres
- Setting Up MySQL
- Setting Up SQL Server
- Setting Up Oracle
- Setting Up Amazon DocumentDB
- Setting Up MongoDB
- Setting Up ClickHouse
- Connecting DBM and Traces
- Data Collected
- Exploring Database Hosts
- Exploring Query Metrics
- Exploring Query Samples
- Exploring Database Schemas
- Exploring Recommendations
- Troubleshooting
- Guides
- Data Streams Monitoring
- Data Observability
- Digital Experience
- Real User Monitoring
- Synthetic Testing and Monitoring
- Continuous Testing
- Experiments
- Product Analytics
- Session Replay
- Software Delivery
- CI Visibility
- CD Visibility
- Deployment Gates
- Test Optimization
- Code Coverage
- PR Gates
- DORA Metrics
- Feature Flags
- Developer Integrations
- Security
- Security Overview
- Cloud SIEM
- Code Security
- Cloud Security
- App and API Protection
- AI Guard
- Workload Protection
- Sensitive Data Scanner
- AI Observability
- Log Management
- Observability Pipelines
- Configuration
- Sources
- Processors
- Destinations
- Packs
- Akamai CDN
- Amazon CloudFront
- Amazon VPC Flow Logs
- AWS Application Load Balancer Logs
- AWS CloudTrail
- AWS Elastic Load Balancer Logs
- AWS Network Load Balancer Logs
- Cisco ASA
- Cloudflare
- F5
- Fastly
- Fortinet Firewall
- HAProxy Ingress
- Istio Proxy
- Juniper SRX Firewall Traffic Logs
- Netskope
- NGINX
- Okta
- Palo Alto Firewall
- Windows XML
- ZScaler ZIA DNS
- Zscaler ZIA Firewall
- Zscaler ZIA Tunnel
- Zscaler ZIA Web Logs
- Search Syntax
- Scaling and Performance
- Monitoring and Troubleshooting
- Guides and Resources
- Log Management
- CloudPrem
- Administration
- Account Management
- Data Security
- Help
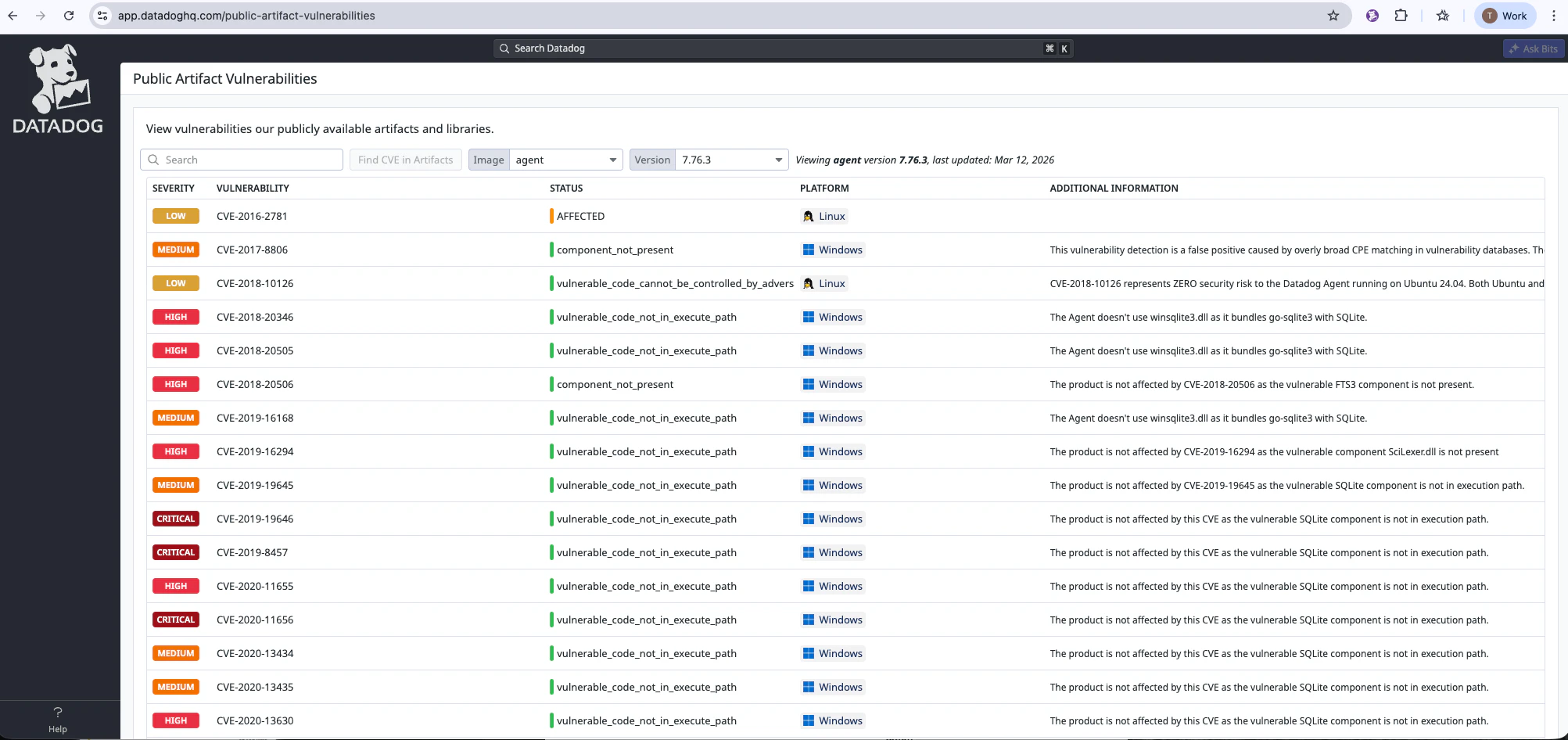
Public Artifact Vulnerabilities
Overview
The Public Artifact Vulnerabilities page lets you view vulnerability and response information for Datadog’s publicly available artifacts and libraries. Use it to look up:
- Which vulnerabilities affect a given artifact (by image/version)
- Which artifacts are affected by a given CVE
- Status, justification, impact, and action statements for each vulnerability
How to access
The Public Artifact Vulnerabilities page is accessible through the Help page under Public Artifact Vulnerabilities.
Using the page
Look up by image and version (artifact-centric)
Use this to see all vulnerabilities for a specific artifact and version (for example, the Datadog Agent image version 7.52.0).
- Image: Choose an artifact from the Image dropdown (for example, agent, cluster-agent, synthetic-private-location-worker). The list is built from available public artifacts.
- Version: Choose a Version for that image. Versions are sorted by newest first.
The table loads and shows one row per vulnerability affecting that image/version.
Table columns (by image/version):
| Column | Purpose |
|---|---|
| Severity | Severity of the vulnerability (for example, Critical, High, Medium, Low, and Info). |
| Vulnerability | CVE or vulnerability identifier and name. |
| Platform | Platform(s) the statement applies to (for example, Linux, Windows). The platform column also shows the list of variants affected by the CVE (for example, fips, jmx, and servercore). |
| Status | Current status: for example, Not affected, Affected, Fixed, and Under investigation. |
| Additional Information | More information on the status of the CVE and justification of the status if needed. For example, if the status is component_not_present, this column explains why the CVE does not affect the artifact and how that conclusion was reached. Some statuses, such as Under investigation, do not have additional information because the impact is still being analyzed. |
You can use the search/filter box above the table to filter these rows by keyword.
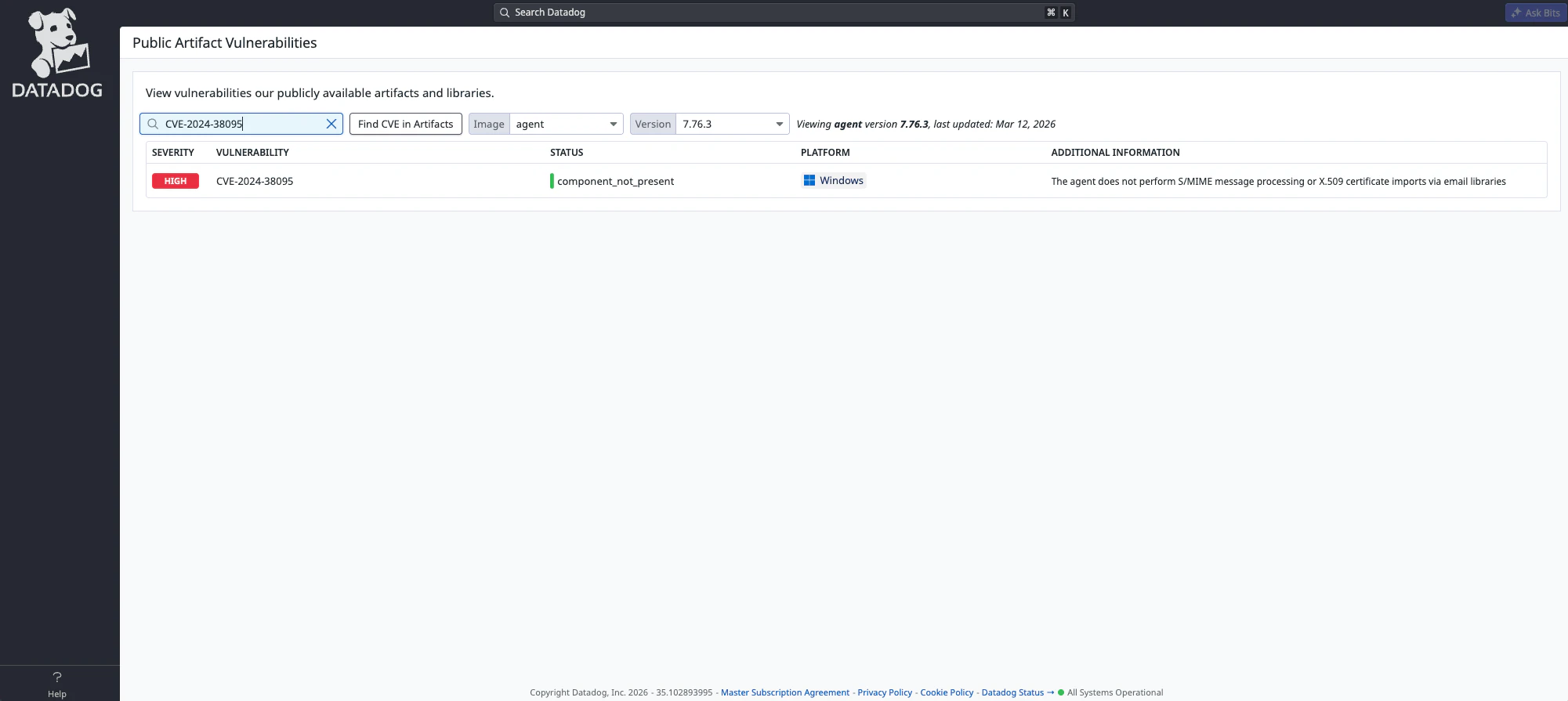
Look up by CVE (CVE-centric)
Use this to find which artifacts/versions are affected and the status for each.
- In the search box at the top of the table, enter one or more CVE IDs (for example,
CVE-2024-1234orCVE-2024-1234, CVE-2024-5678for multiple). - Click Find CVE in artifacts.
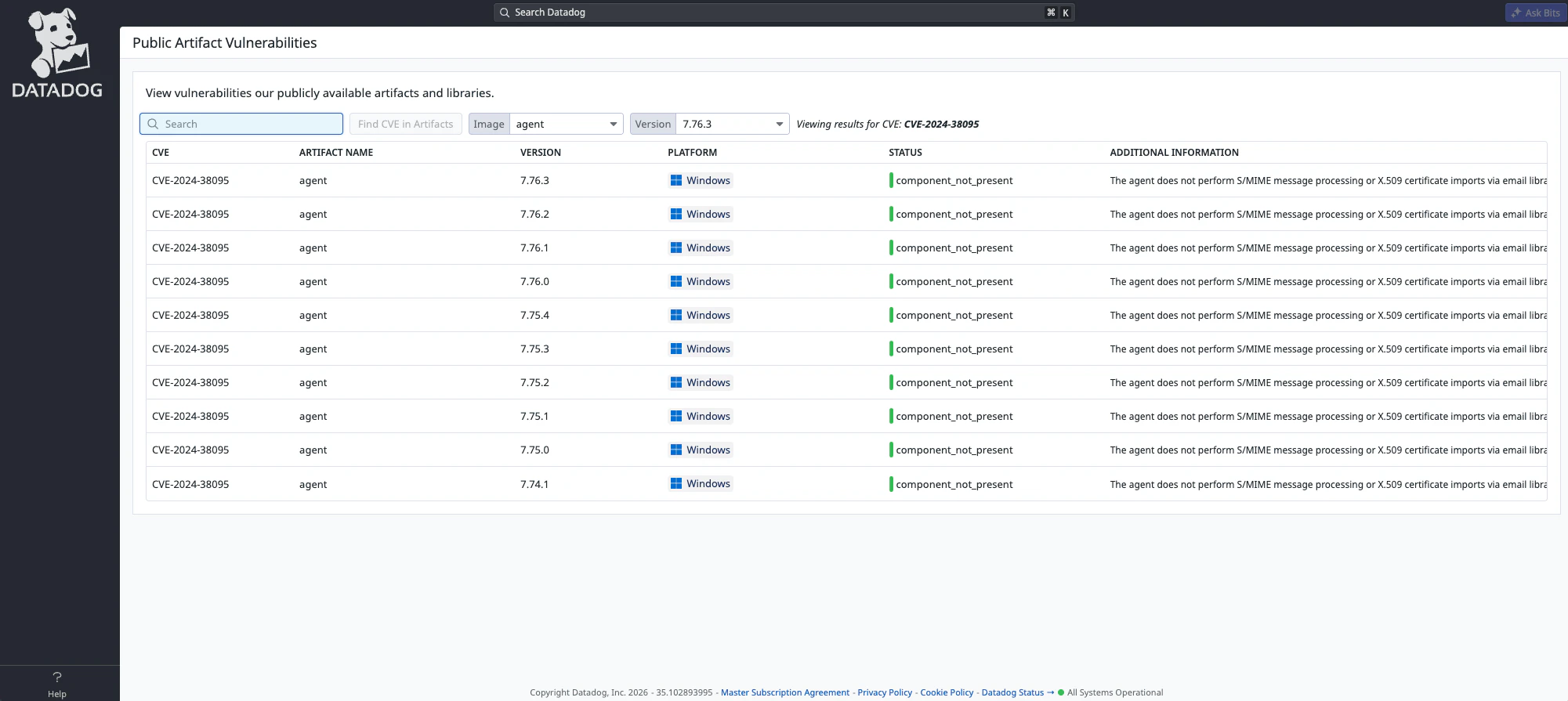
The table switches to CVE mode and shows one row per (CVE, artifact, version, status) combination.
Table columns (by CVE):
| Column | Purpose |
|---|---|
| CVE | The CVE ID. |
| Artifact Name | Name of the artifact (for example, agent, library name). |
| Version | Version of the artifact. |
| Platform | Platform(s) for this row (for example, Linux, Windows). |
| Status | Status for this CVE/artifact/version (for example, Not affected, Affected, Fixed, and Under investigation). |
| Additional Information | More information on the status of the CVE and justification of the status if needed. |
After you search for a CVE, the table filter clears so all returned rows are visible. You can type in the search box again to filter the current result set.
Available artifacts (images)
The Image dropdown is populated from the list of tracked public artifacts. If an expected artifact is missing, contact Datadog Support to request that it be added.
Options and actions on the page
| Option or action | Description |
|---|---|
| Search / global filter | Filter table rows by any text. In “by image/version” mode, the same search box is used before clicking Find CVE in artifacts to run a CVE lookup. |
| Find CVE in artifacts | Runs a CVE lookup using the current search box value (supports comma-separated CVE IDs). Only relevant when you want to look up by CVE. |
| Pagination | Use the table pagination to move through large result sets (for example, 50 rows per page). |
| Resizable columns | You can resize column widths for readability. |