- Essentials
- Getting Started
- Agent
- API
- APM Tracing
- Containers
- Dashboards
- Database Monitoring
- Datadog
- Datadog Site
- DevSecOps
- Incident Management
- Integrations
- Internal Developer Portal
- Logs
- Monitors
- OpenTelemetry
- Profiler
- Session Replay
- Security
- Serverless for AWS Lambda
- Software Delivery
- Synthetic Monitoring and Testing
- Tags
- Workflow Automation
- Learning Center
- Support
- Glossary
- Standard Attributes
- Guides
- Agent
- Integrations
- Developers
- Authorization
- DogStatsD
- Custom Checks
- Integrations
- Create an Agent-based Integration
- Create an API Integration
- Create a Log Pipeline
- Integration Assets Reference
- Build a Marketplace Offering
- Create a Tile
- Create an Integration Dashboard
- Create a Monitor Template
- Create a Cloud SIEM Detection Rule
- OAuth for Integrations
- Install Agent Integration Developer Tool
- Service Checks
- IDE Plugins
- Community
- Guides
- OpenTelemetry
- Administrator's Guide
- API
- Partners
- Datadog Mobile App
- DDSQL Reference
- CoScreen
- CoTerm
- Cloudcraft (Standalone)
- In The App
- Dashboards
- Notebooks
- DDSQL Editor
- Reference Tables
- Sheets
- Monitors and Alerting
- Metrics
- Watchdog
- Bits AI
- Internal Developer Portal
- Error Tracking
- Change Tracking
- Service Management
- Actions & Remediations
- Infrastructure
- Cloudcraft
- Resource Catalog
- Universal Service Monitoring
- Hosts
- Containers
- Processes
- Serverless
- Network Monitoring
- Cloud Cost
- Application Performance
- APM
- APM Terms and Concepts
- Application Instrumentation
- APM Metrics Collection
- Trace Pipeline Configuration
- Correlate Traces with Other Telemetry
- Trace Explorer
- Recommendations
- Code Origins for Spans
- Service Observability
- Endpoint Observability
- Dynamic Instrumentation
- Live Debugger
- Error Tracking
- Data Security
- Guides
- Troubleshooting
- Continuous Profiler
- Database Monitoring
- Agent Integration Overhead
- Setup Architectures
- Setting Up Postgres
- Setting Up MySQL
- Setting Up SQL Server
- Setting Up Oracle
- Setting Up Amazon DocumentDB
- Setting Up MongoDB
- Connecting DBM and Traces
- Data Collected
- Exploring Database Hosts
- Exploring Query Metrics
- Exploring Query Samples
- Exploring Database Schemas
- Exploring Recommendations
- Troubleshooting
- Guides
- Data Streams Monitoring
- Data Jobs Monitoring
- Data Observability
- Digital Experience
- Real User Monitoring
- Synthetic Testing and Monitoring
- Continuous Testing
- Product Analytics
- Software Delivery
- CI Visibility
- CD Visibility
- Deployment Gates
- Test Optimization
- Quality Gates
- DORA Metrics
- Security
- Security Overview
- Cloud SIEM
- Code Security
- Cloud Security
- App and API Protection
- Workload Protection
- Sensitive Data Scanner
- AI Observability
- Log Management
- Observability Pipelines
- Log Management
- Administration
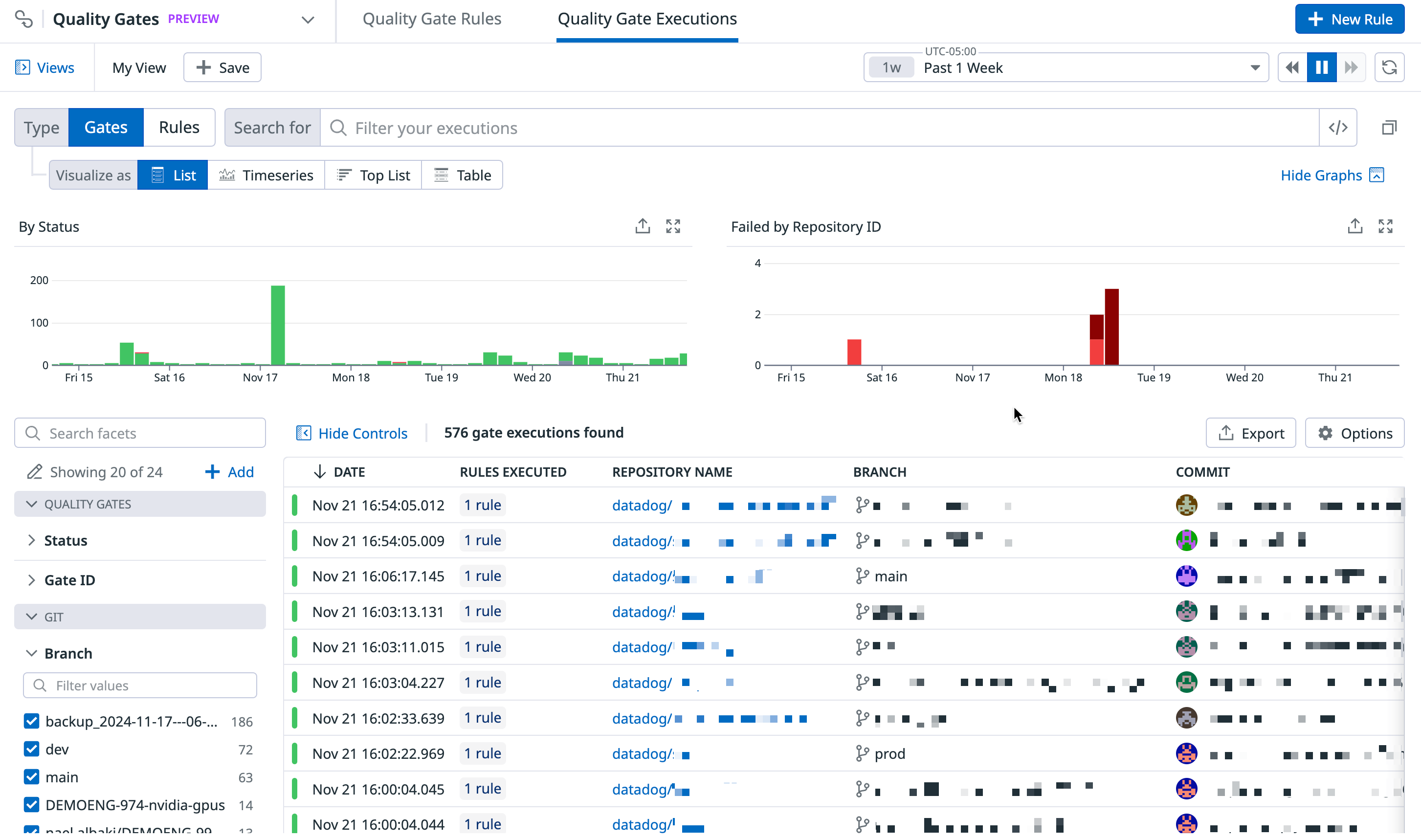
Quality Gates Explorer
This product is not supported for your selected Datadog site. ().
Overview
The Quality Gates Explorer allows you to search and filter, visualize, and export quality gates or rule executions at multiple levels using any tag.
Navigate to Software Delivery > Quality Gates > Quality Gate Executions to see your Quality Gates.
The Quality Gates panel on the left lists default facets you can use to search for your gates.
| Facet | Description |
|---|---|
| Status | The quality gate status: Passed or Failed. |
| Gate ID | The ID of the quality gate. |
Quality Gate details
You can see aggregated data about quality gates over the selected time frame. Use the search field and facets to filter the list to show the gates you want to investigate.
Quality Gate data
Quality Gate data is available in dashboards and notebooks, enabling build engineering teams to customize their communication about high-priority work and CI trends over time.
Navigate to Software Delivery > Quality Gates > Quality Gate Executions to see your Quality Gate rule executions.
The Quality Gates panel on the left lists default facets you can use to search for your rule executions.
| Facet | Description |
|---|---|
| Status | The quality gate status: Passed or Failed. |
| Rule Name | The user-given name to identify a particular rule. |
| Blocking Status | Determines whether or not the rule status will cause the CI workflow to fail: true or false. |
| Creator | The user who created the quality gate rule. |
| Data Source | The source of data being evaluated for the rule (tests, static analysis). |
| Gate ID | The ID of the quality gate. |
Rule executions details
You can see aggregated data about rule executions over the selected time frame. Use the search field and facets to filter the list to show the executions you want to investigate.
Rule execution data
Quality Gate rules data is available in dashboards and notebooks, enabling build engineering teams to customize their communication about high-priority work and CI trends over time.
Search and filter
You can narrow down, broaden, or shift your focus on a subset of quality gates or rule executions by clicking on the facets to the left or writing your own custom query in the search bar. When you select and deselect facets, the search bar automatically reflects your changes. Similarly, you can modify the search bar query or write a query from scratch.
- To learn how to search for quality gate rules, see Search and Manage.
- To learn how to create queries, see Search Syntax.
Analyze
Group quality gates or rule executions into higher-level fields, patterns, and transactions to derive or consolidate information. You do not need to create a facet in order to search for an attribute. Use facets to:
- Identify trends and patterns in Quality Gate executions: Understand which repositories or pipelines are being blocked most often.
- Identify trends and patterns in Quality Gate Rule executions: Understand which types of rules are failing most often across the organization.
Visualize
Select a visualization type to visualize the outcomes of filters and aggregations and better understand your quality gates or rule executions. For example, you can view gate results in a list to organize gates data into columns, or in a timeseries graph to measure gate execution data over time.
Export
Export your view in the Quality Gates Explorer to reuse it later or in different contexts. For more information, see Saved Views.
Further reading
Additional helpful documentation, links, and articles: